Connected Apps for Google Drive
Connected Apps allows Skyhigh CASB Incident Managers to discover third-party applications associated with Google Drive and connected to your corporate environment via OAuth. Then it provides a workflow for you to manually remediate, audit, allow, or block Connected Apps access to users data, to notify users via email of an app's status, and revoke access as needed.
For more general information on Connected Apps, see About Connected Apps. For information on creating and managing policies, see Connected Apps Policies.
Configure Connected Apps Monitoring in Google Admin
For this procedure, see Configure Google Drive.
OAuth Scopes
Connected Apps provides visibility into OAuth Scopes, which are strings of permissions used by Google APIs to request access to resources, such as user data. For more information, see OAuth 2.0 Scopes for Google APIs.
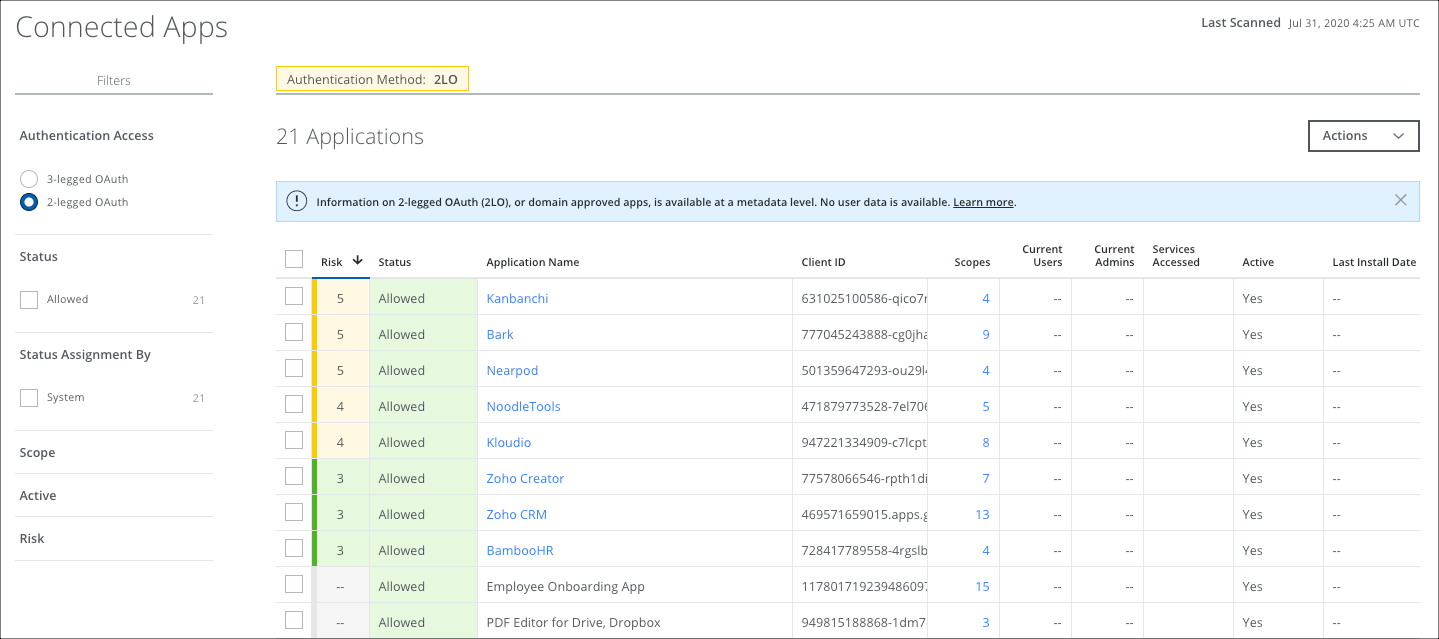
2-Legged OAuth in Connected Apps for Google Drive
On the Connected Apps page, you can filter to display 2-legged or 3-legged OAuth apps for Google Drive Connected Apps.
3-legged OAuth
A 3-legged OAuth flow involves three parties: the end-user (or resource owner), the client (the third-party application), and the server (or authorization server). This is the default filter view on the Connected Apps page.
Google considers 3-legged OAuth apps user-managed apps, where they are downloaded from a marketplace and installed by the user in a domain.
2-legged OAuth
A 2-legged OAuth flow describes an OAuth-authenticated request without end-user involvement. 2-legged Connected Apps are approved across the enterprise. Information on 2-legged OAuth is available at a metadata level. No user data is available.
Google considers 2-legged OAuth apps administrator-managed apps, where an admin grants access to an application at the domain level to access data for all users. Though in some administrator-managed apps, the user's consent is also required.
In the Connected Apps page, all administrator-managed apps are allowed by default because the admin has given consent for all users to use it. Admins cannot change the status of the app.
Events associated with 2-legged apps are not processed by Skyhigh CASB. They are dropped because they are already approved and don't require further processing.
For this reason, the following columns in the table view are not used for 2-legged Connected Apps:
- Current Users
- Current Admins
Revoke and Remove a 2-legged App
If an admin revokes access to or removes a 2-legged Connected App, the app will be treated as a 3-legged app going forward. After removing or revoking access to the app, the app will not appear in either table until a new event is detected. Then it will appear in the 3-legged OAuth table.
NOTE: Google's SLA allows 2 hours before events are submitted. For details, see Data retention and lag times for token.
Disabling an App in Google Admin Console
An admin can perform the following actions in the Google admin console:
- Domain Install an App. The Connected App is displayed in Skyhigh CASB in the 2-legged OAuth table.
- Revoke an App. This removes the Connected App from the 2-legged OAuth table. It is displayed on the 3-legged OAuth table only after an event occurs.
- Disable an App. No action occurs in Skyhigh CASB. The Connected App still appears in the Skyhigh CASB 2-legged OAuth table.
- Remove an App. The Connected App is removed from the 2-legged OAuth table. It is displayed on the 3-legged OAuth table only after an event occurs.
NOTE: In the Google admin console, toggling enable or disable on an app has no effect.

