Set up Inline DLP for Gmail
IMPORTANT: Before setting up Gmail Inline DLP, you must open a support ticket, and request assistance in pre-configuring your tenant.
Step 1: Create a Gmail Instance in Skyhigh CASB
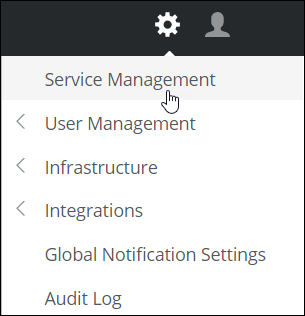
- Log in to Skyhigh CASB.
- Go to Settings > Service Management.
- Click Add Service Instance.
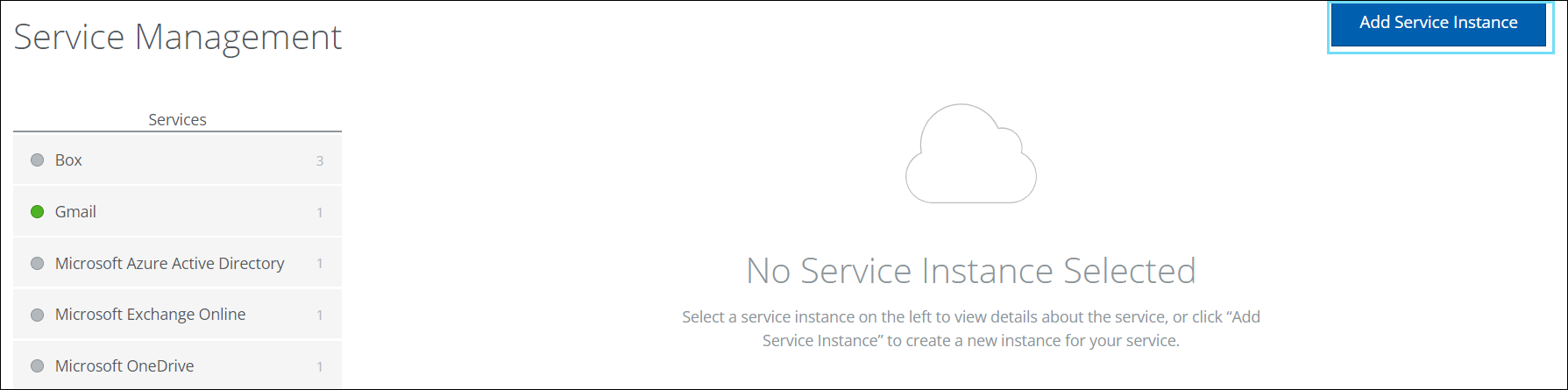
- Select Gmail, enter a name for this new instance, and click Done.
- To configure the instance, click Configure.
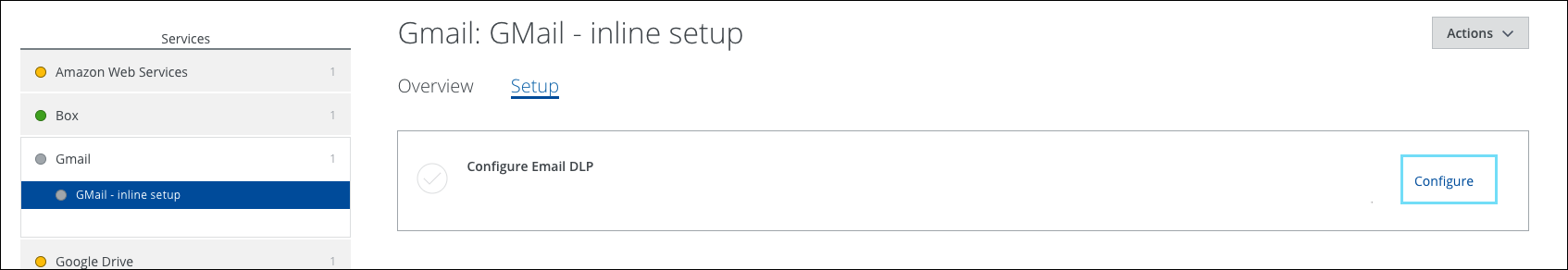
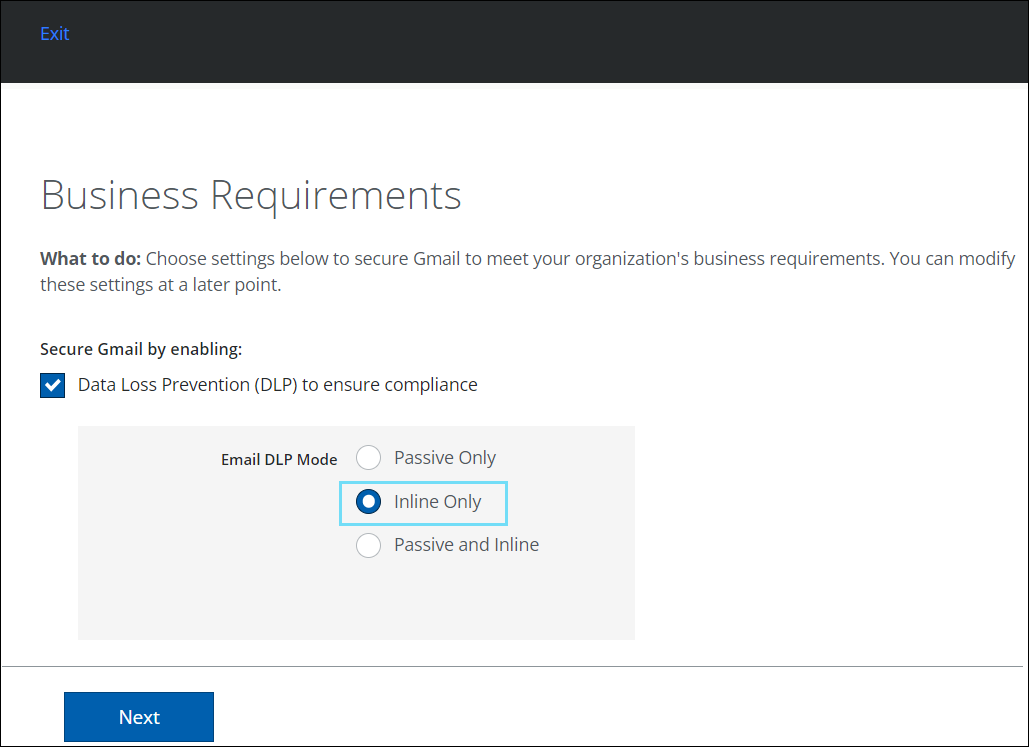
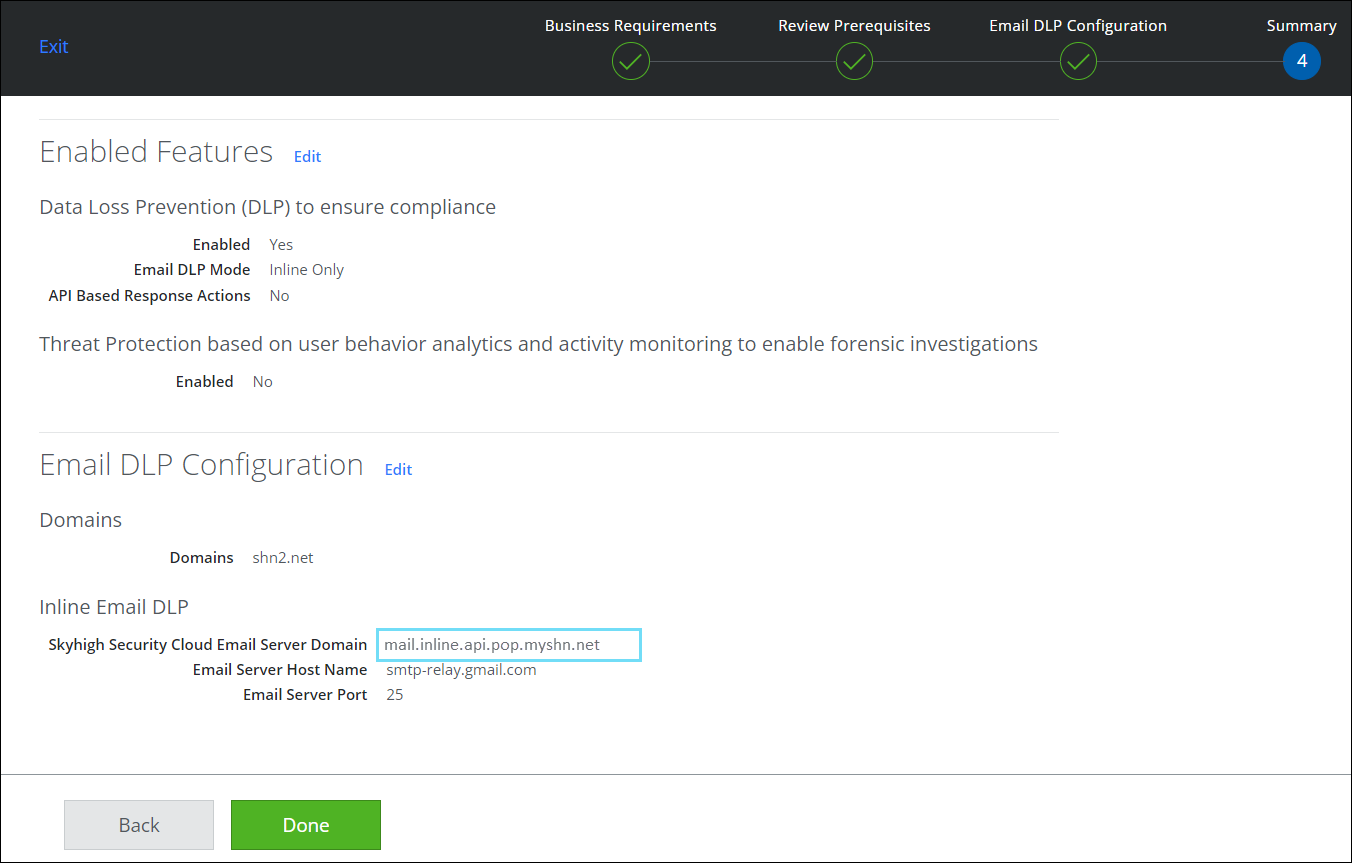
- Activate the Data Loss Prevention (DLP) to ensure compliance checkbox, and under Email DLP Mode, select Inline Only.
- Click Next.
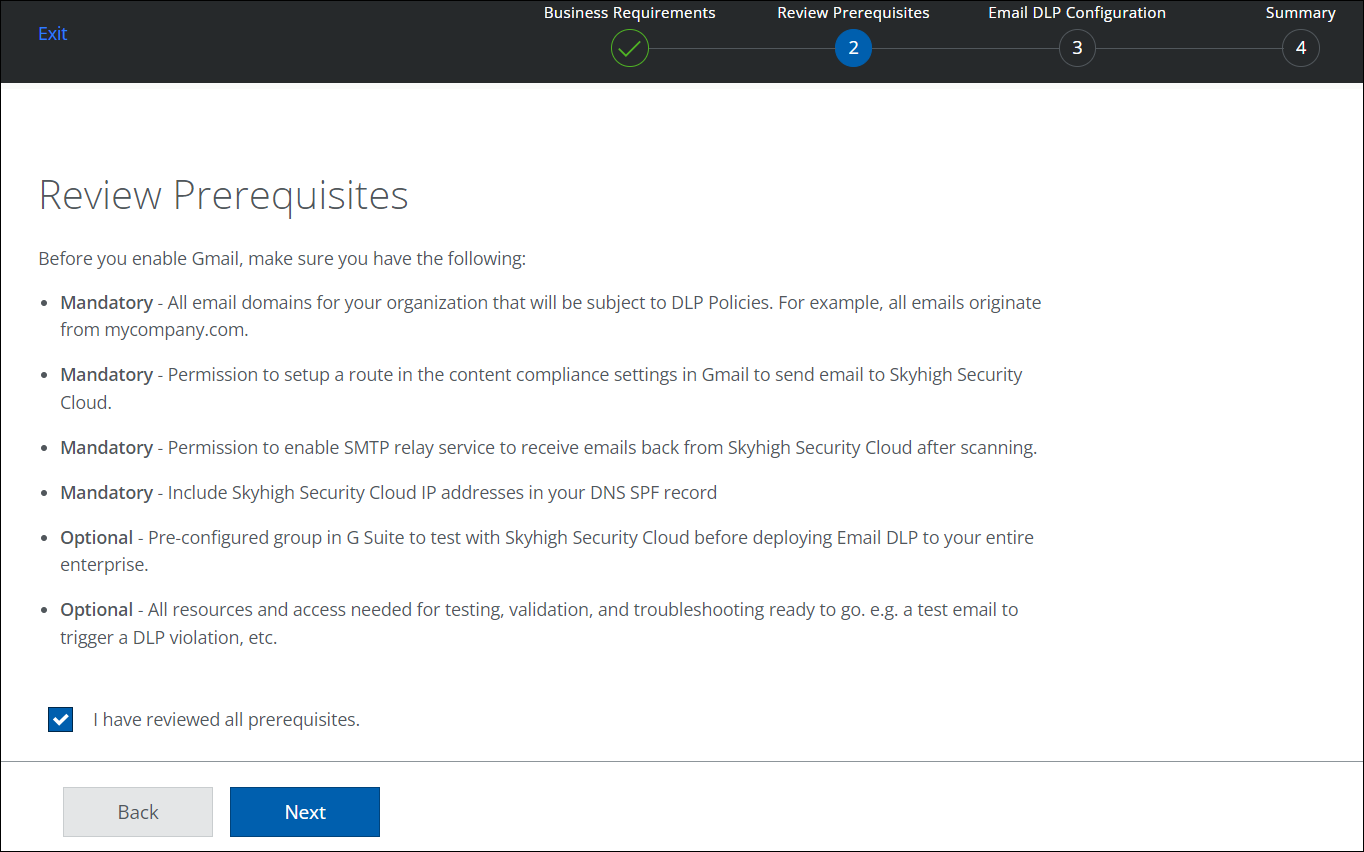
- Review the prerequisites, and activate I have reviewed all prerequisites checkbox and click Next.
- Make sure the following are complete:
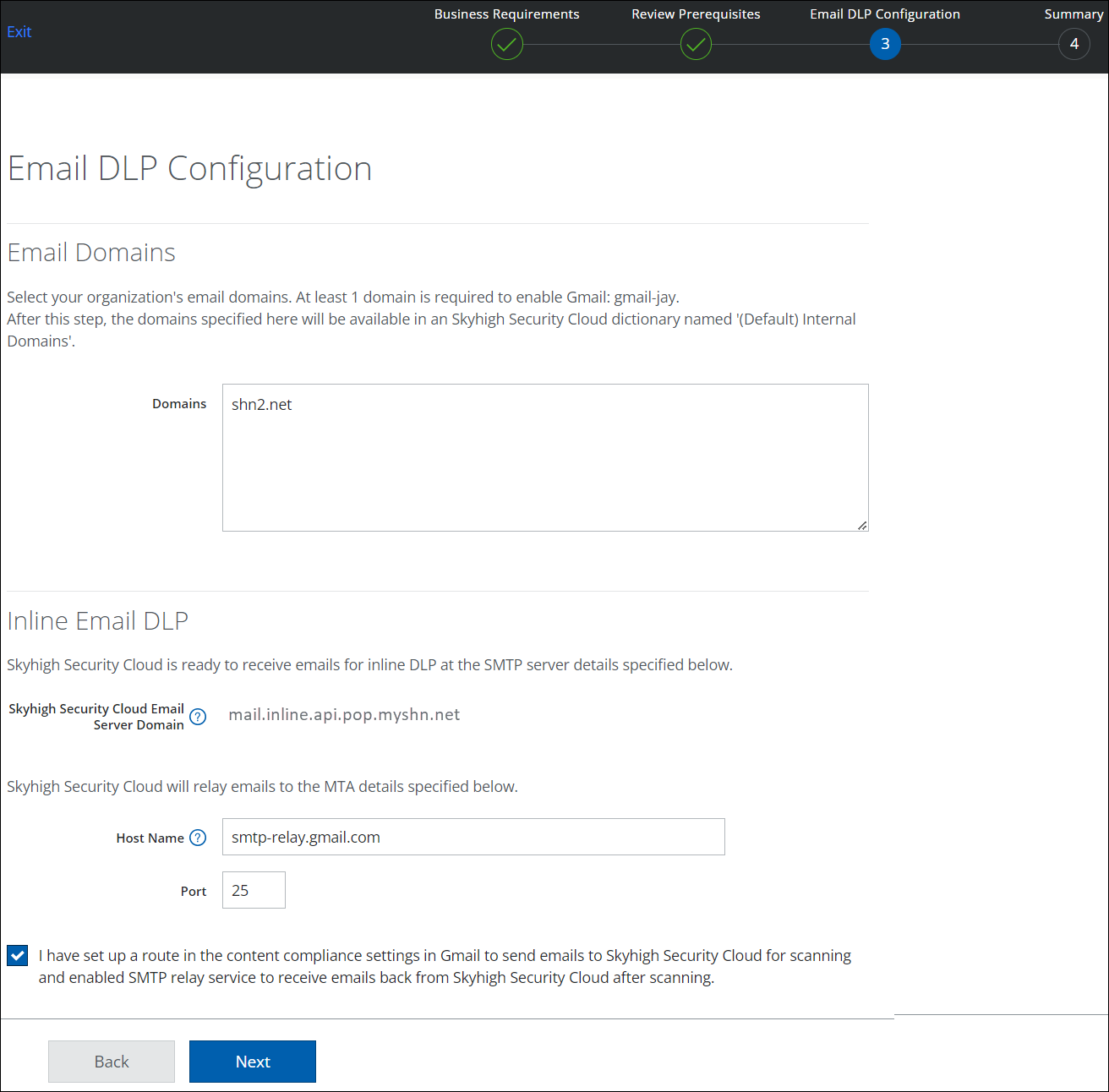
- Domains. Populate with all public domains configured with the Google Suite tenant. Make sure that the domains belong to your tenant and are not common public domains.
NOTE: Skyhigh CASB Inline DLP for Gmail supports emails only from your organization's email domains and not from public domains. For example, you must not add gmail.com or google.com domains.
- Take note of the Skyhigh CASB Email Service Domain. You will need this later.
- Select the checkbox confirming you've configured Gmail, as you need this in the next step and click Next.
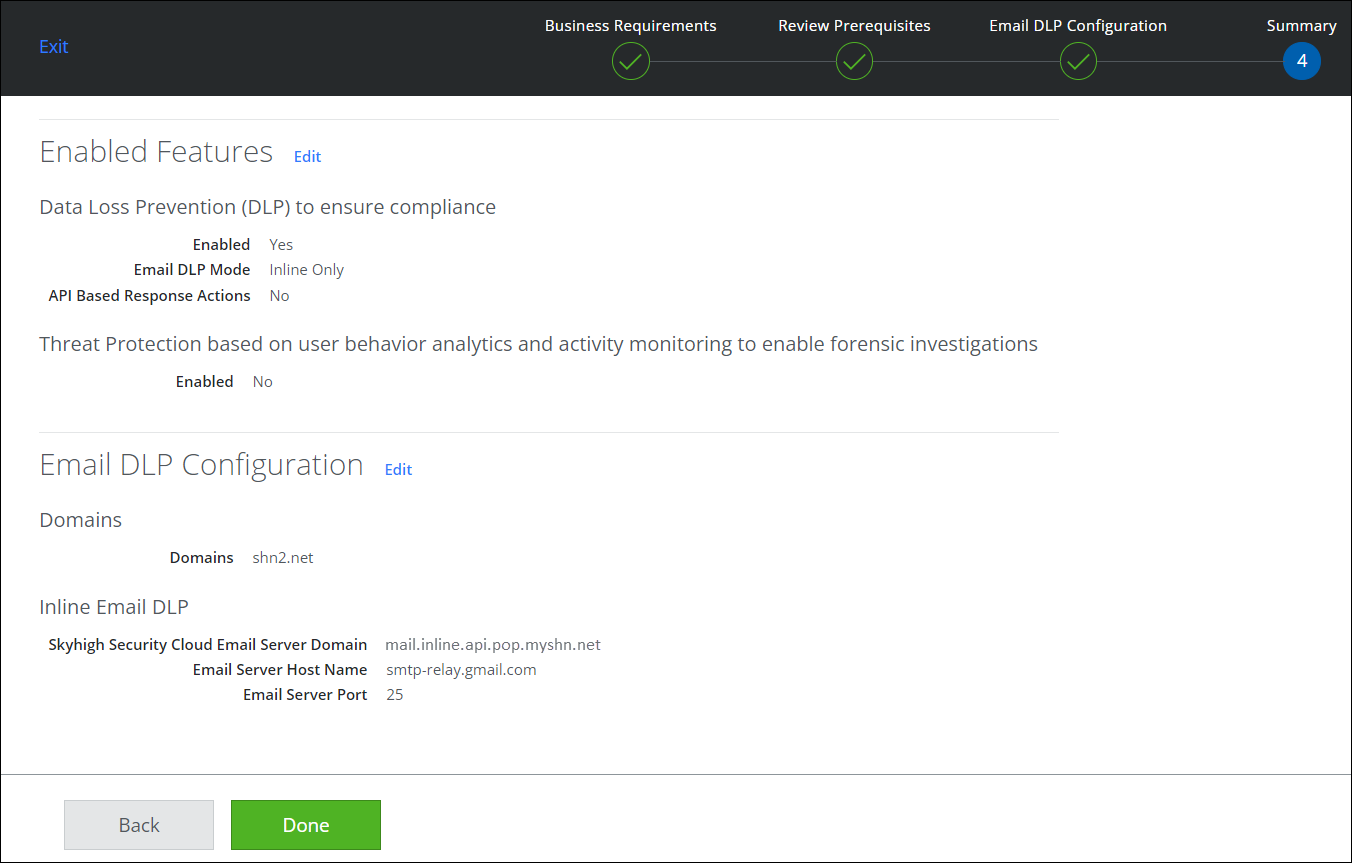
- Review the settings, and click Done.
Step 2: Configure Gmail to Route Email to Skyhigh CASB
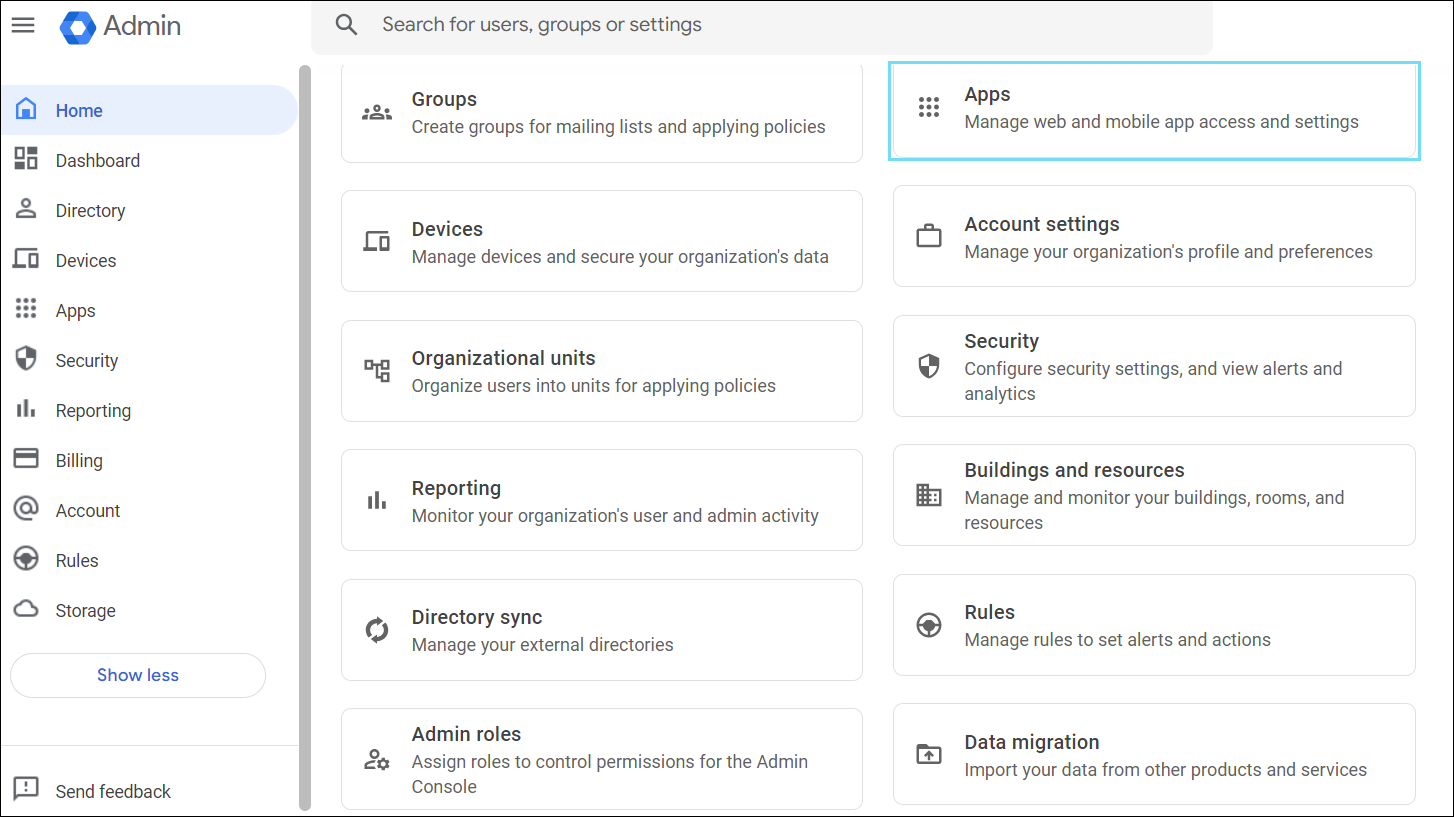
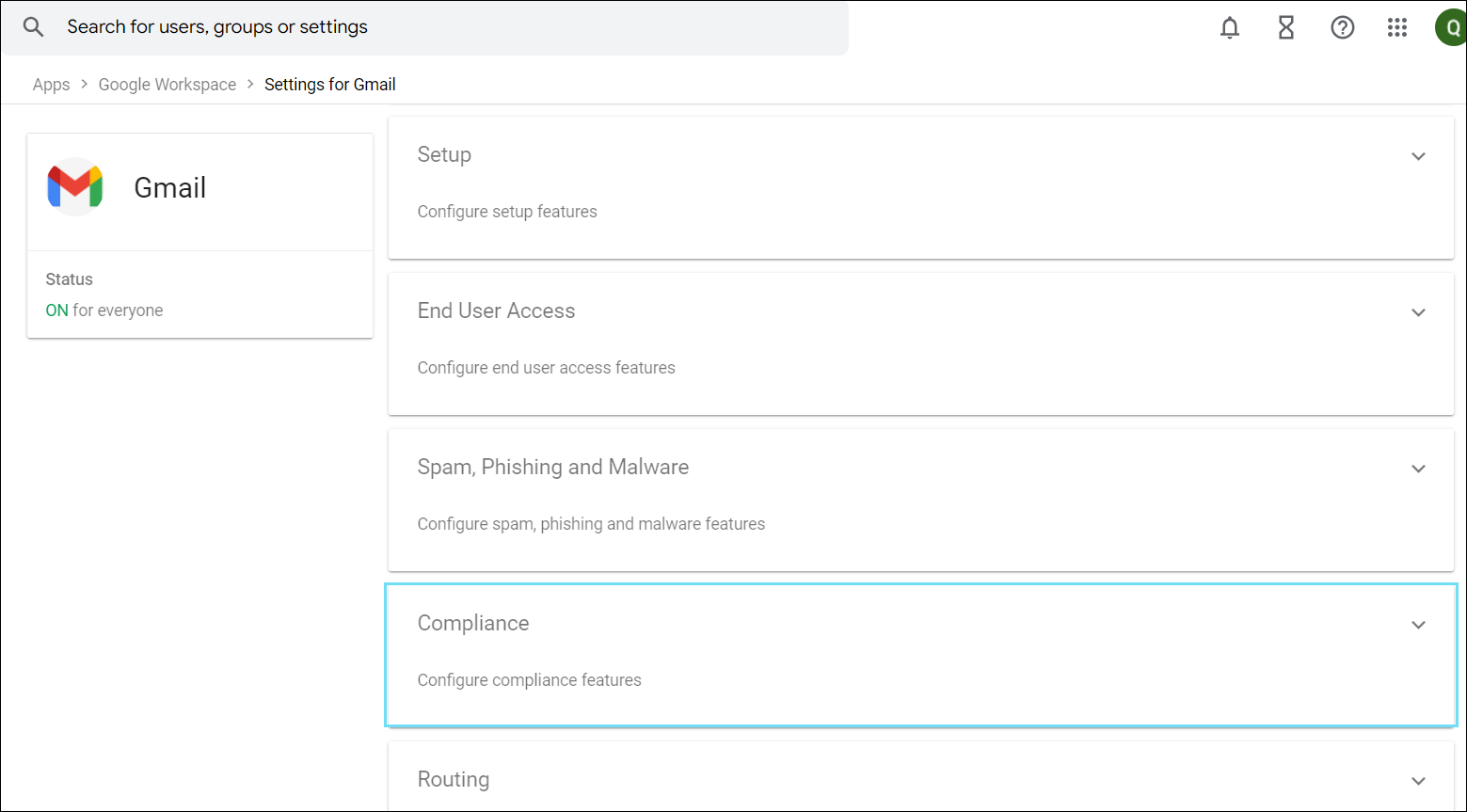
- Log in to Google Suite admin (https://admin.google.com), and go to Apps.
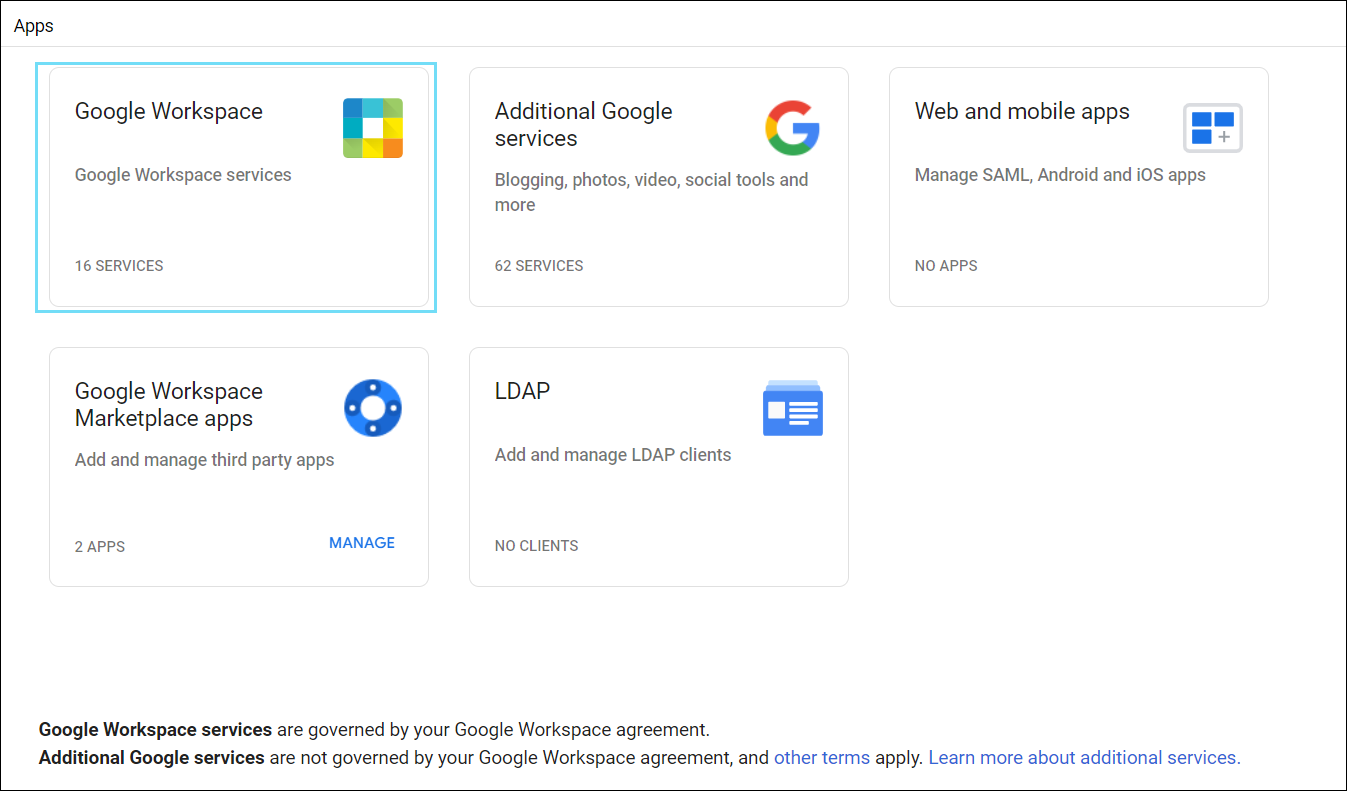
- Select Google Workspace.
- Select Gmail.
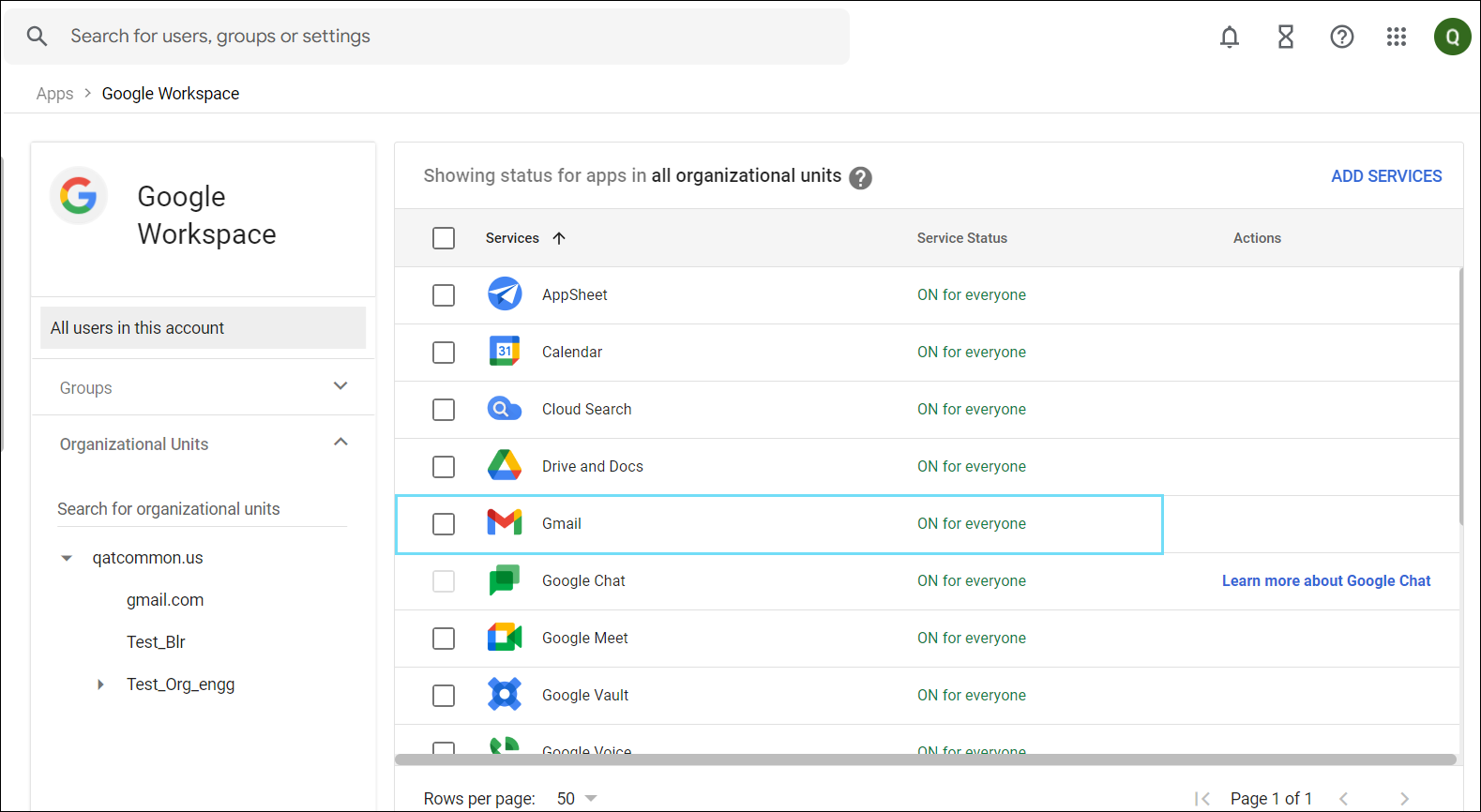
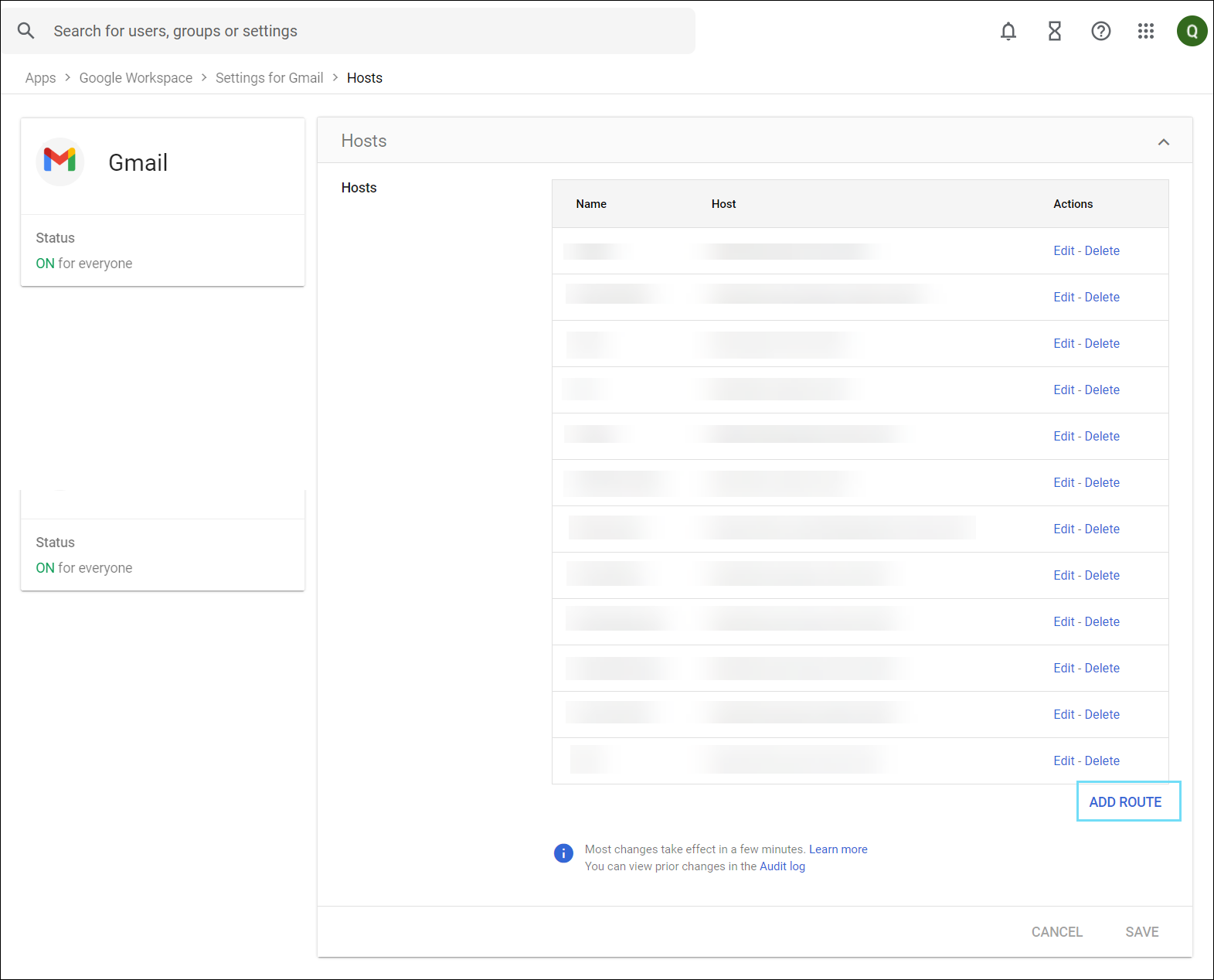
- Scroll down and select Hosts.
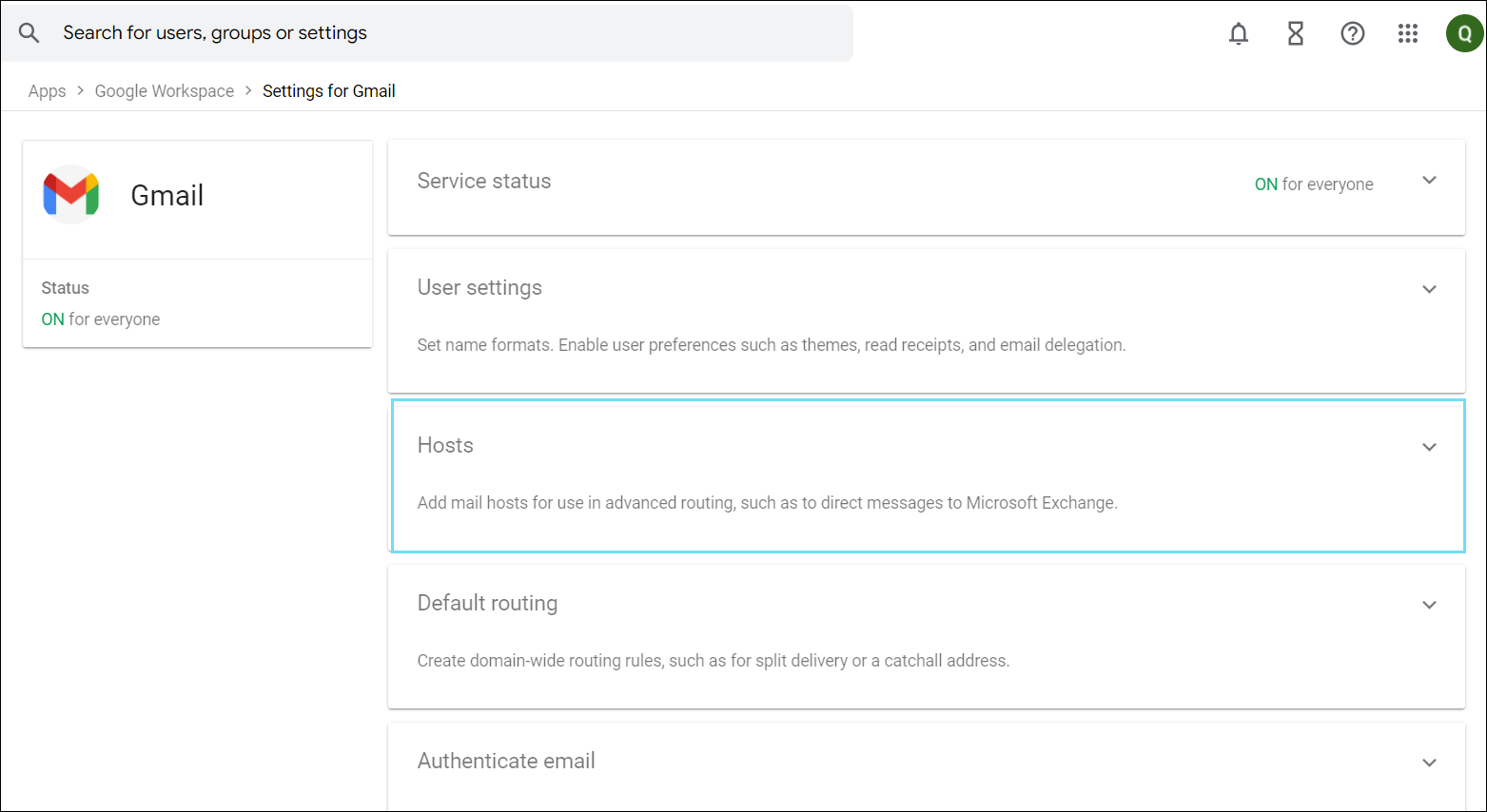
- On the Hosts tab, click CONFIGURE. If you have an existing host on your Gmail account, then you will see the option ADD ROUTE. Click ADD Route to add more hosts.
- Enter the following details for the new mail route:
- Enter a name.
- Enter the single host as captured earlier (Skyhigh CASB Email Service Domain in step 1)
-
- ► See image
- Enter port 25.
- Disable MX lookup and Require secure transport TLS.
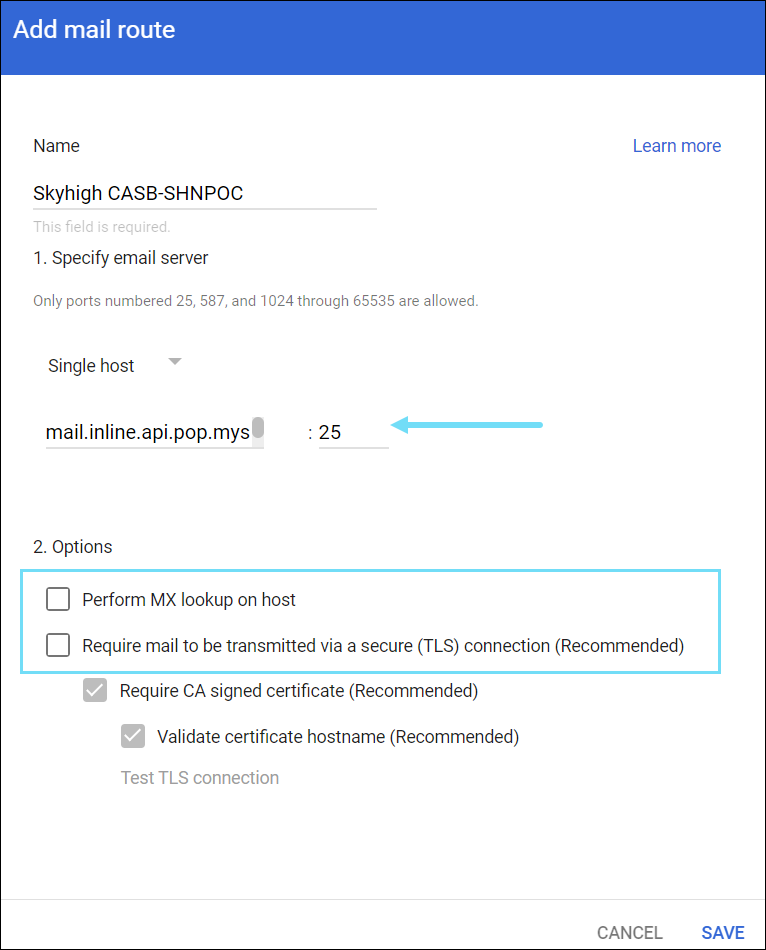
- Click SAVE.
NOTE: Do not enable Require secure transport (TLS) because it requires communication between the email servers initiated with TLS. Skyhigh CASB uses START-TLS instead, which initiates communication with standard SMTP. Then upgrade to TLS after the connection is set up.
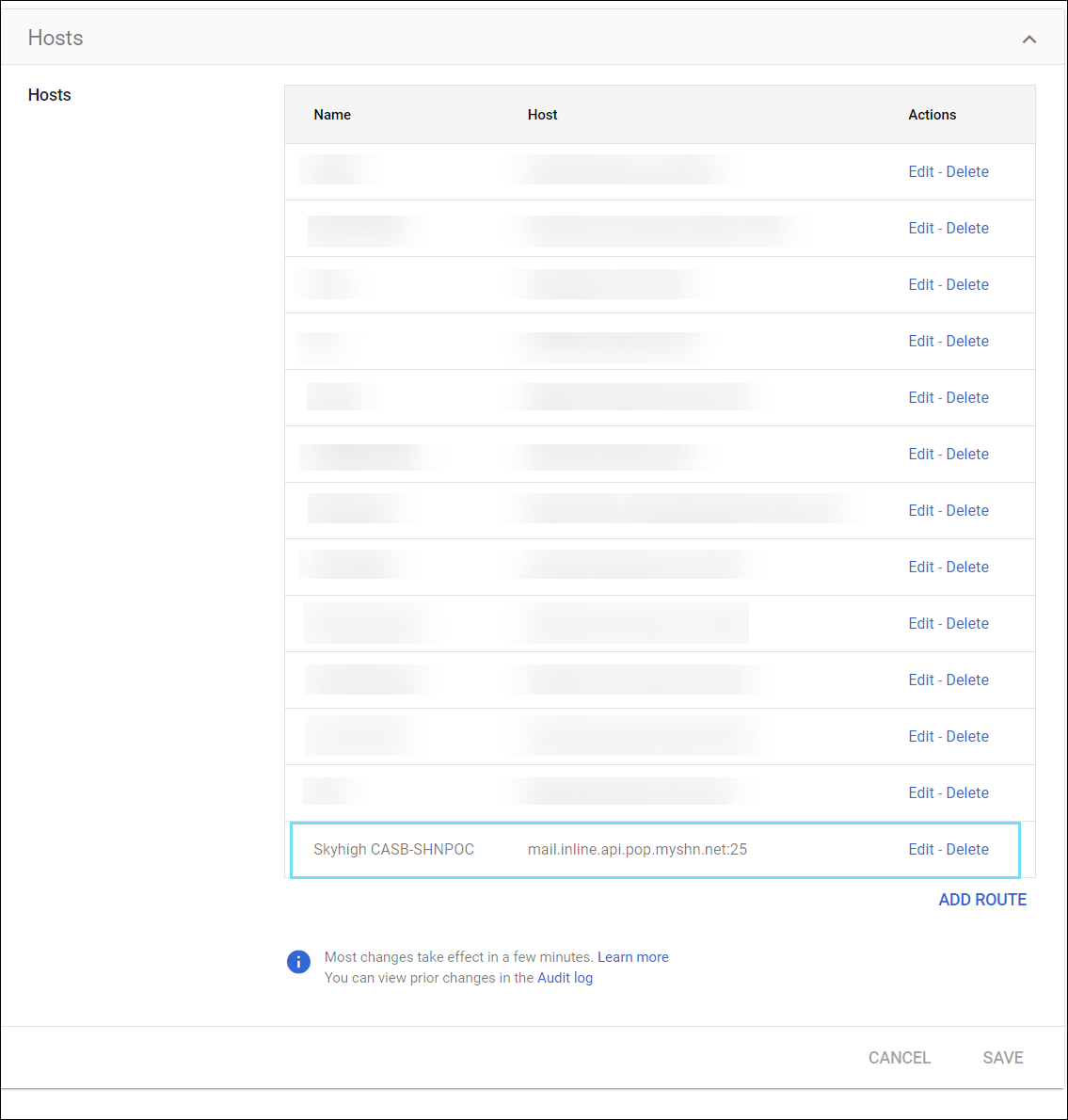
- The new mail route is saved on the Hosts tab.
- Select the Settings for Gmail tab, and click Compliance.
-
Under the Content compliance section, click CONFIGURE. If you have an existing compliance rule on your Gmail account, then you will see the option ADD ANOTHER RULE. Click ADD ANOTHER RULE to add more rules to your compliance feature.
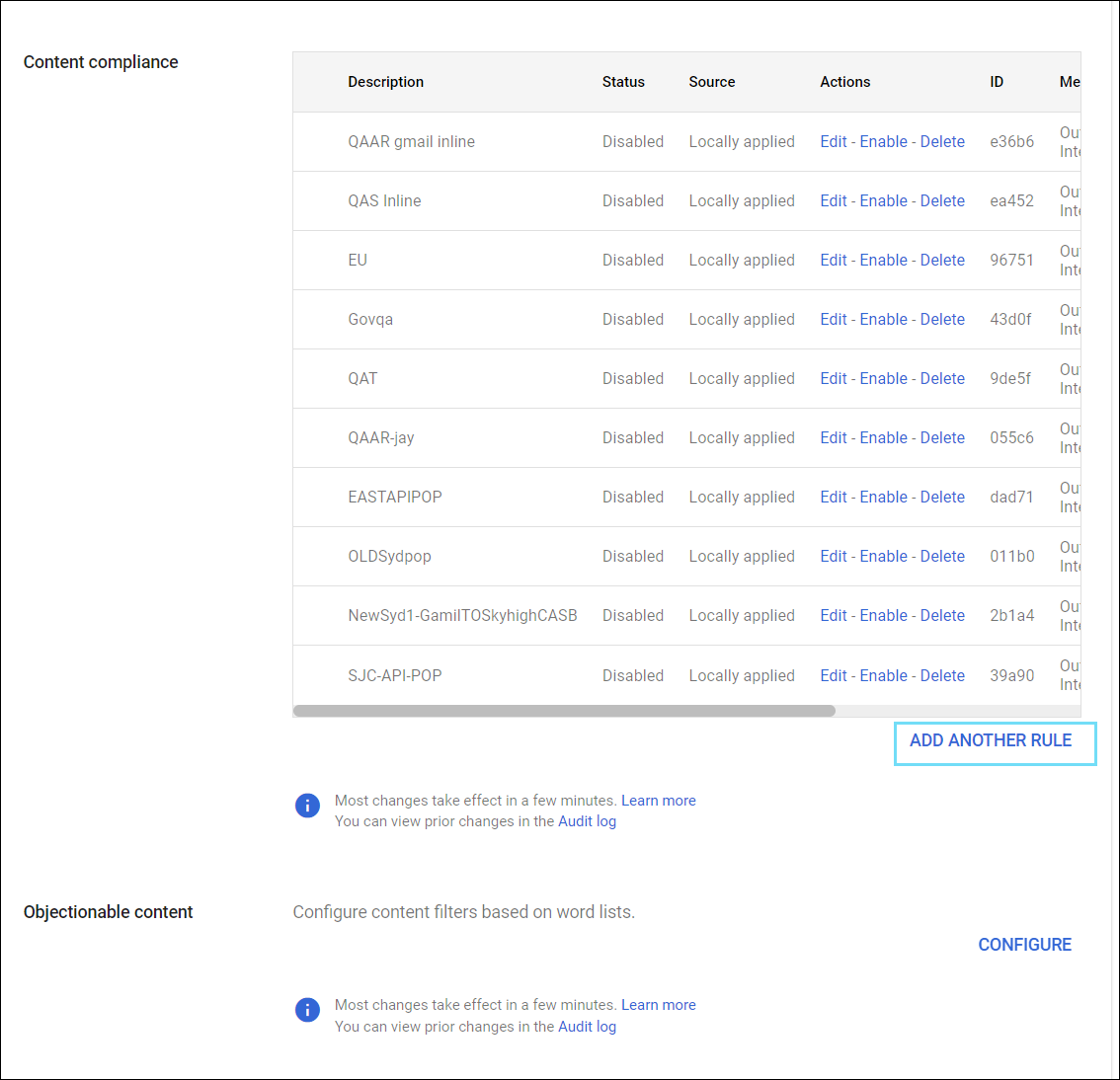
- On the Add setting page, configure the rule as follows:
- Content compliance. Enter a name for the rule which helps to identify the settings easily. For example, Skyhigh CASB DLP
- Email messages to affect. Select Outbound and select Internal - sending to enable scanning for internal emails, sent from GMail to the Skyhigh CASB PoP.
- Click ADD.
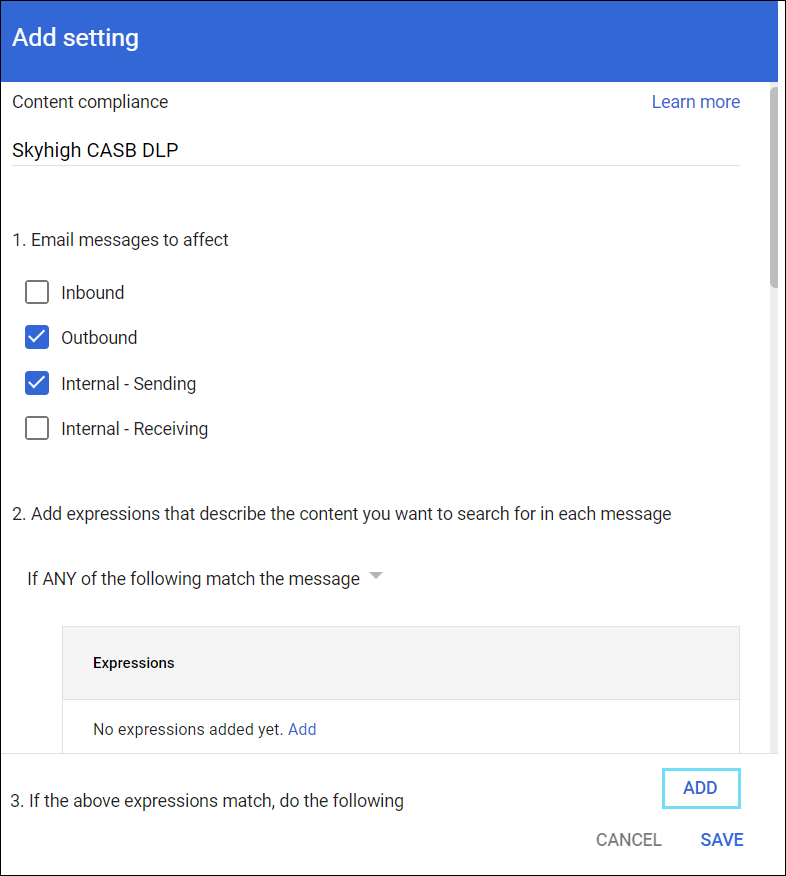
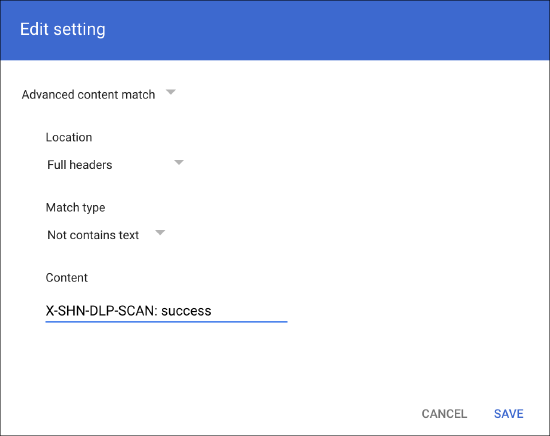
- Select Advanced content match from the menu.
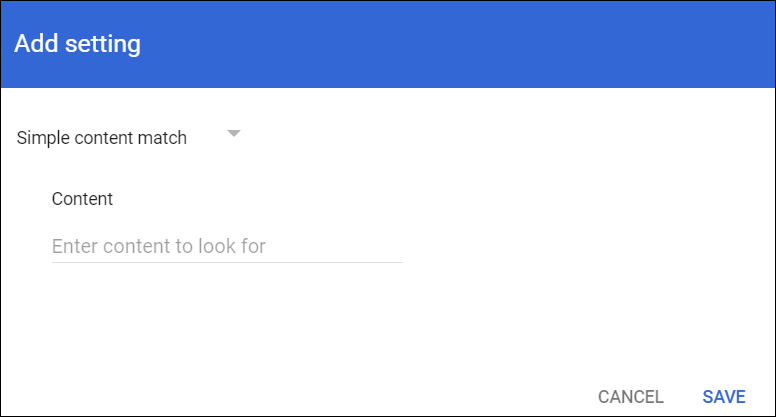
- On the Advanced content match menu, configure the following:
- Location. Select Full headers from the menu
- Match Type. Select Not contains text from the menu
- Content. Enter the content as X-SHN-DLP-SCAN: success
- Click SAVE.
- Under Route, activate the Change route checkbox and select the host created earlier.
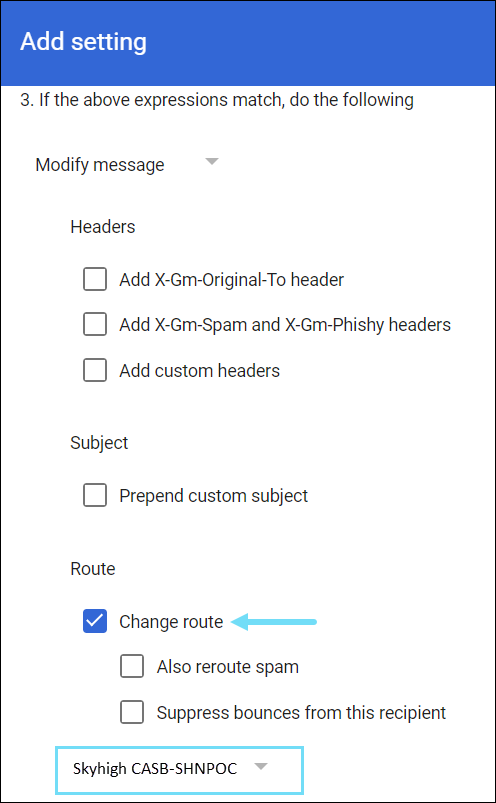
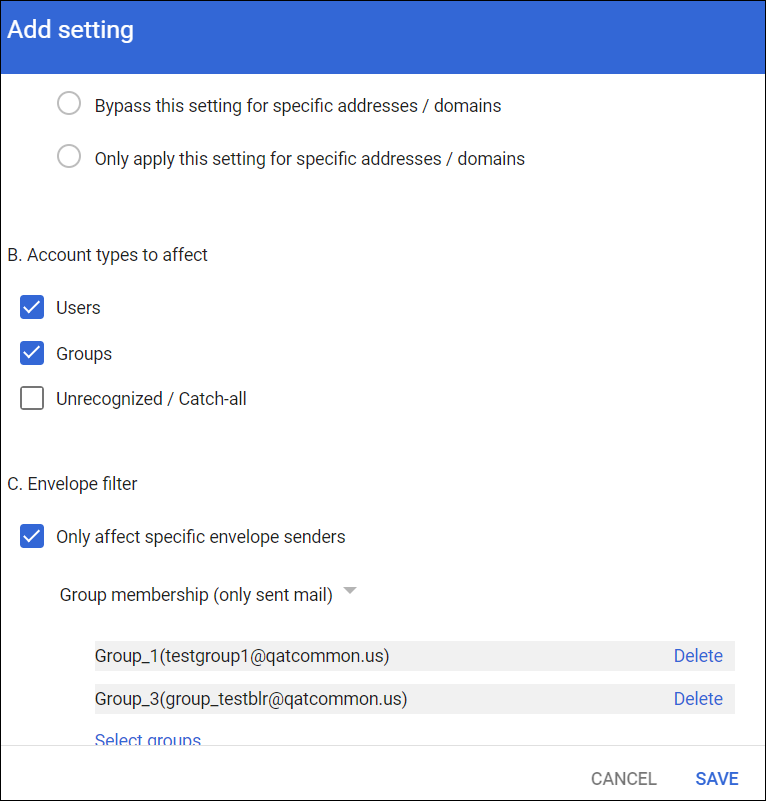
- Click Show options to open the below options:
- Under Account types to affect, select Users and Groups.
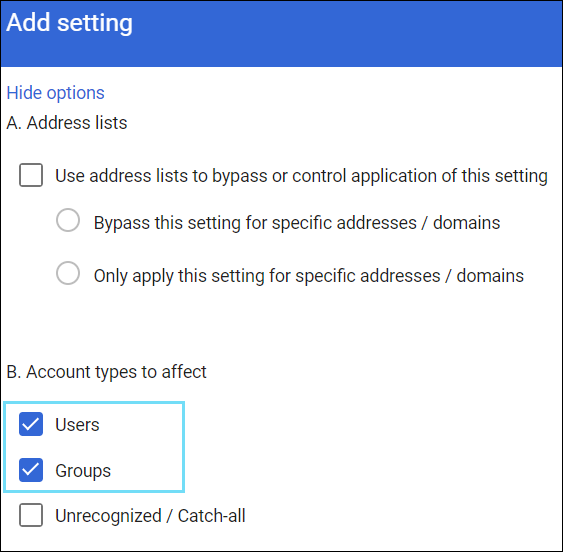
- Under Account types to affect, select Users and Groups.
IMPORTANT:
- If this is a production environment, apply this rule to a test user/group so all mailboxes are not impacted.
- Do not save the configuration yet.
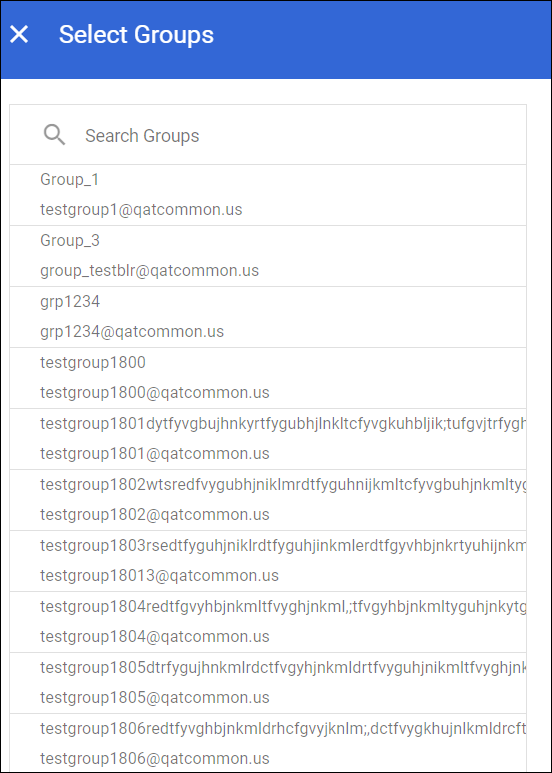
- To enable DLP for specific users or mail groups, configure the following:
- Under the Envelope filter, select Only affect specific envelope senders.
- Select Group membership (only sent mail) from the menu to enable DLP for mail groups.
- Click Select groups.
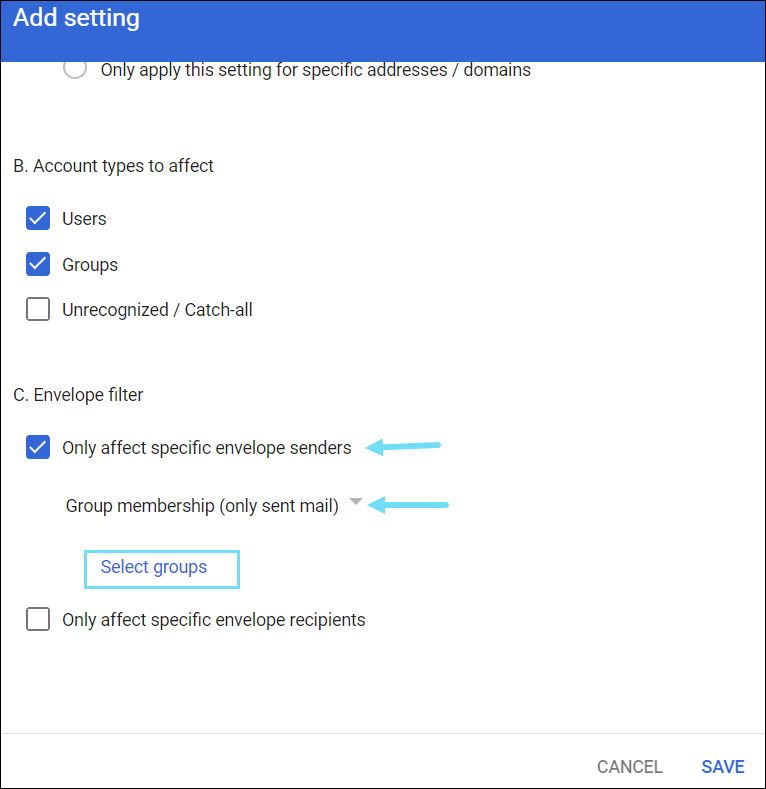
- From the Select Groups dialog, select the required mail groups.
- Click SAVE.
- Under the Settings for Gmail, select Routing.
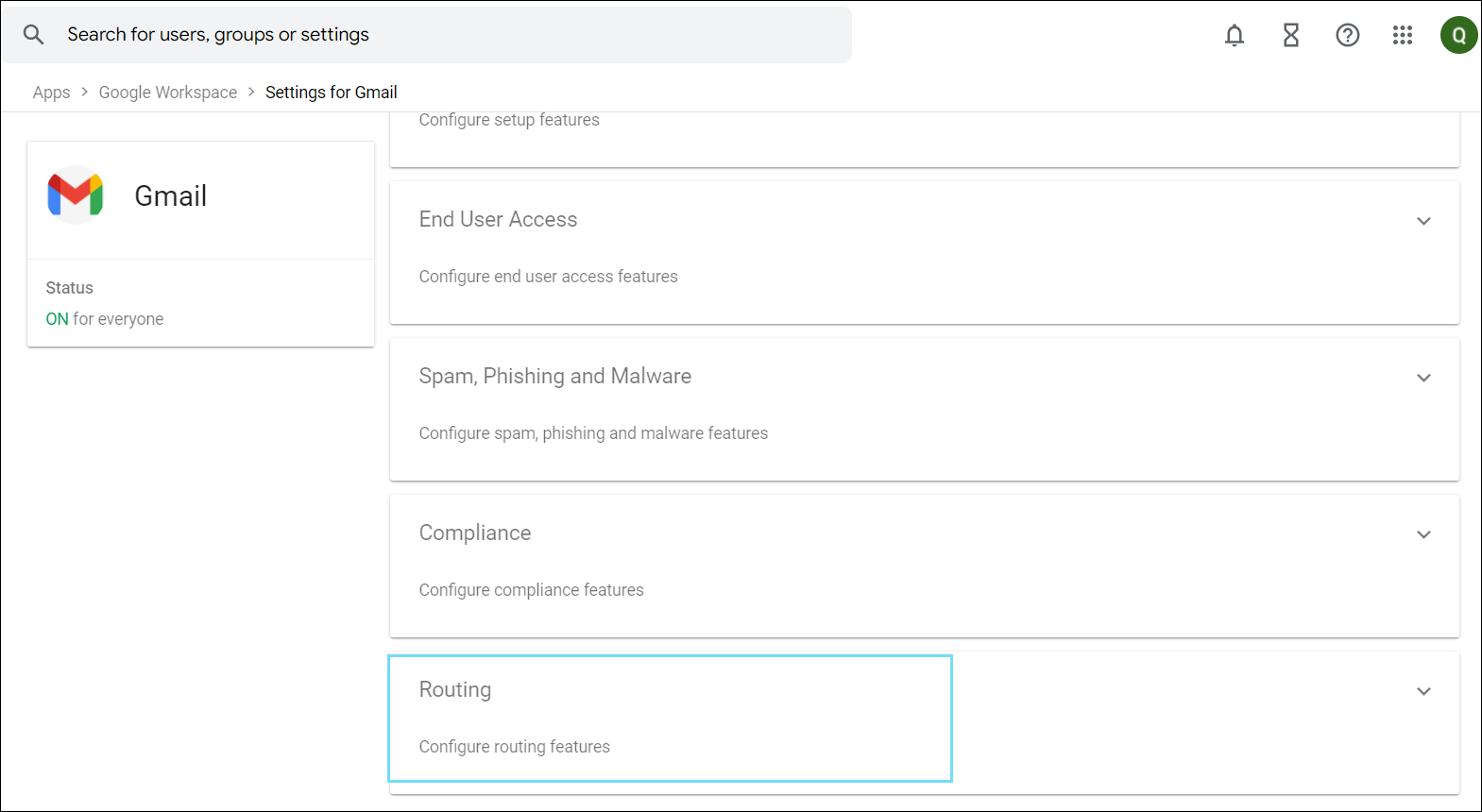
- Find the SMTP relay service and click CONFIGURE. If you have an existing SMTP relay service rule on your Gmail account, then you will see the option ADD ANOTHER RULE. Click ADD ANOTHER RULE to add more rules to your SMTP relay service.
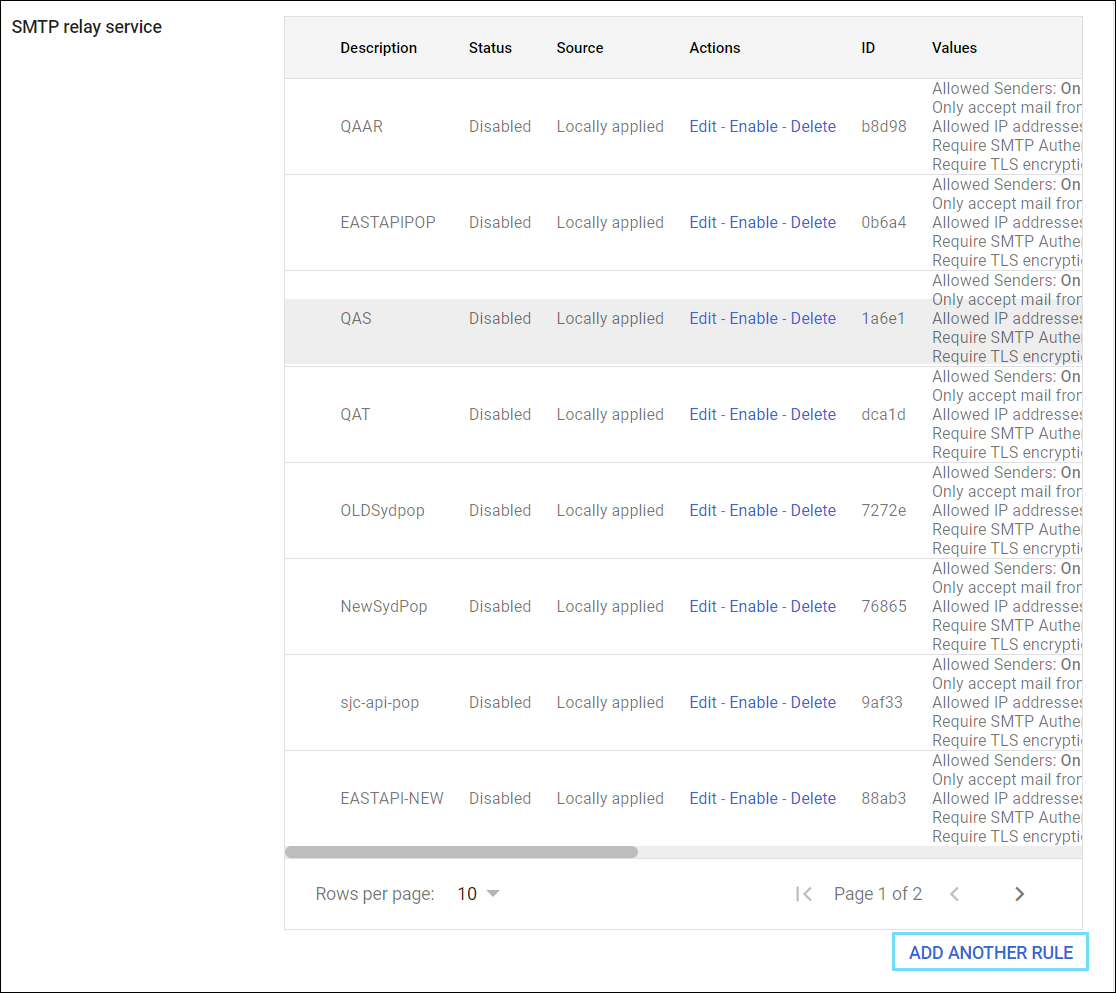
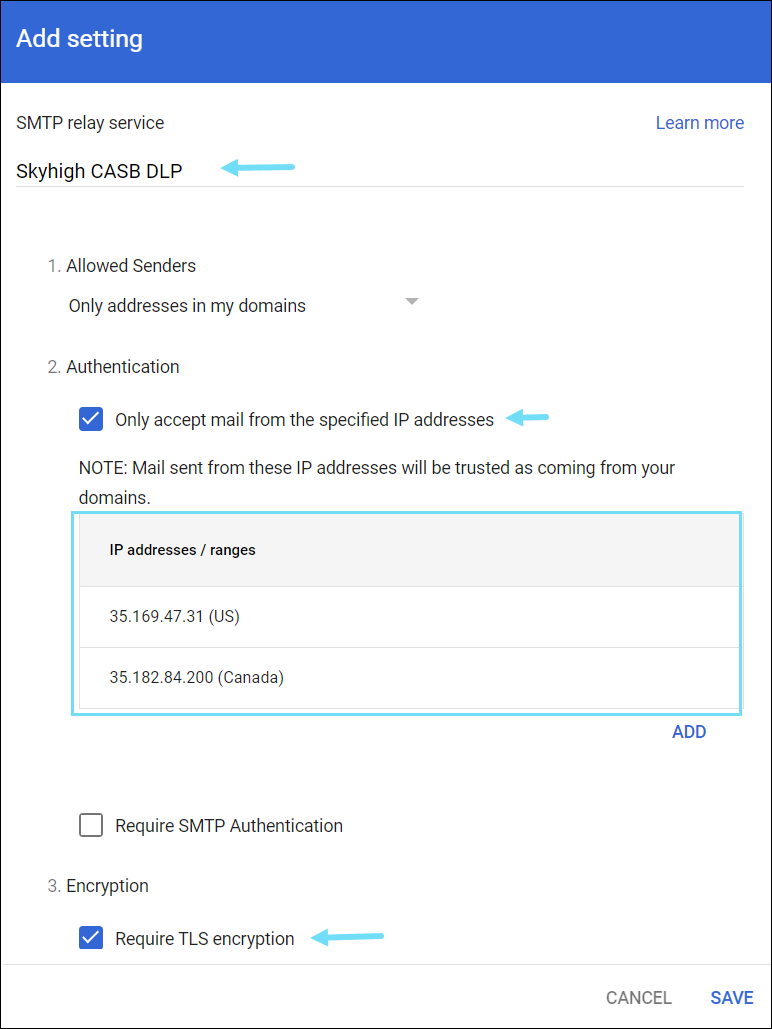
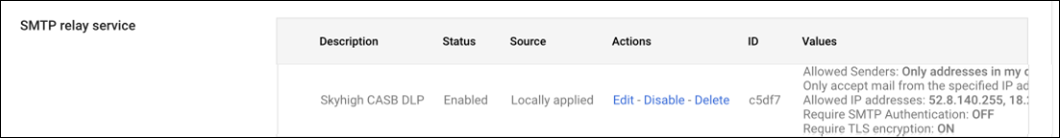
- Configure the SMTP relay service rule as follows:
- SMTP rely service. Enter a name for the rule (for example, Skyhigh CASB DLP).
- Allowed Senders. Set to Only addresses in my domains.
- Authentication. Select Only accept mail from the specified IP addresses and enter the following based on the environment.
- You must add each IP address to the list as in the following Gmail rule:
Skyhigh CASB Source IP Addresses
|
- Encryption: Set Require TLS encryption and click SAVE.
- Once saved, you can view the compliance and SMTP relay configurations.
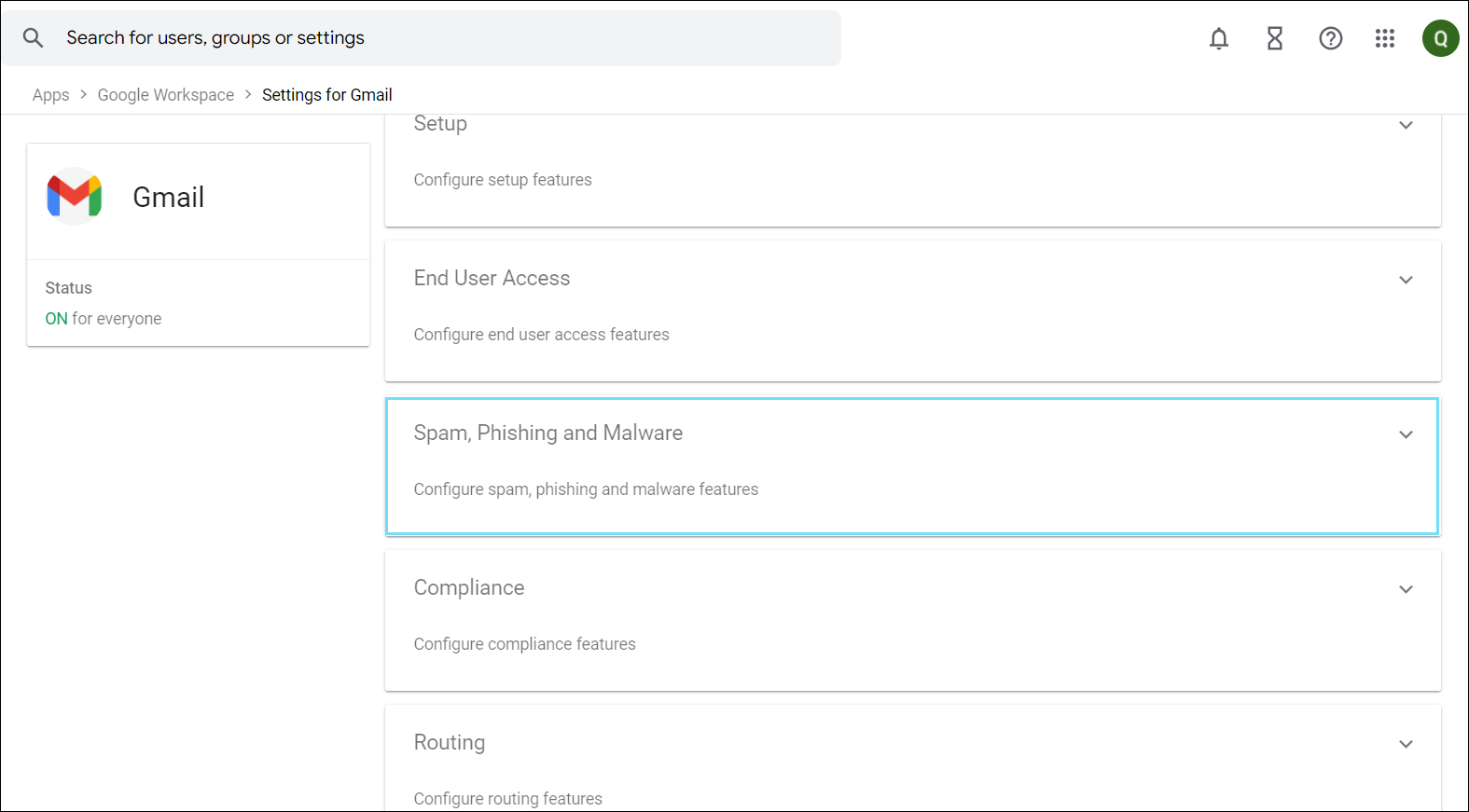
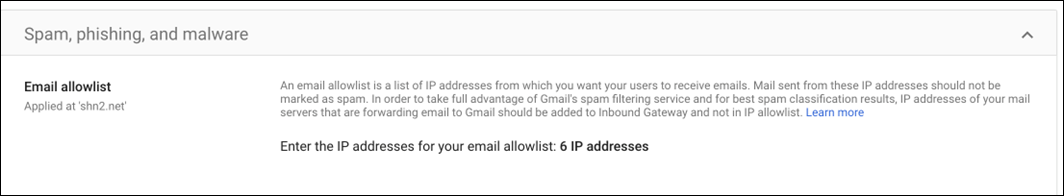
- Under the Settings for Gmail tab, select Spam, Phishing and Malware.
- Under Email allowlist, click the Edit icon.
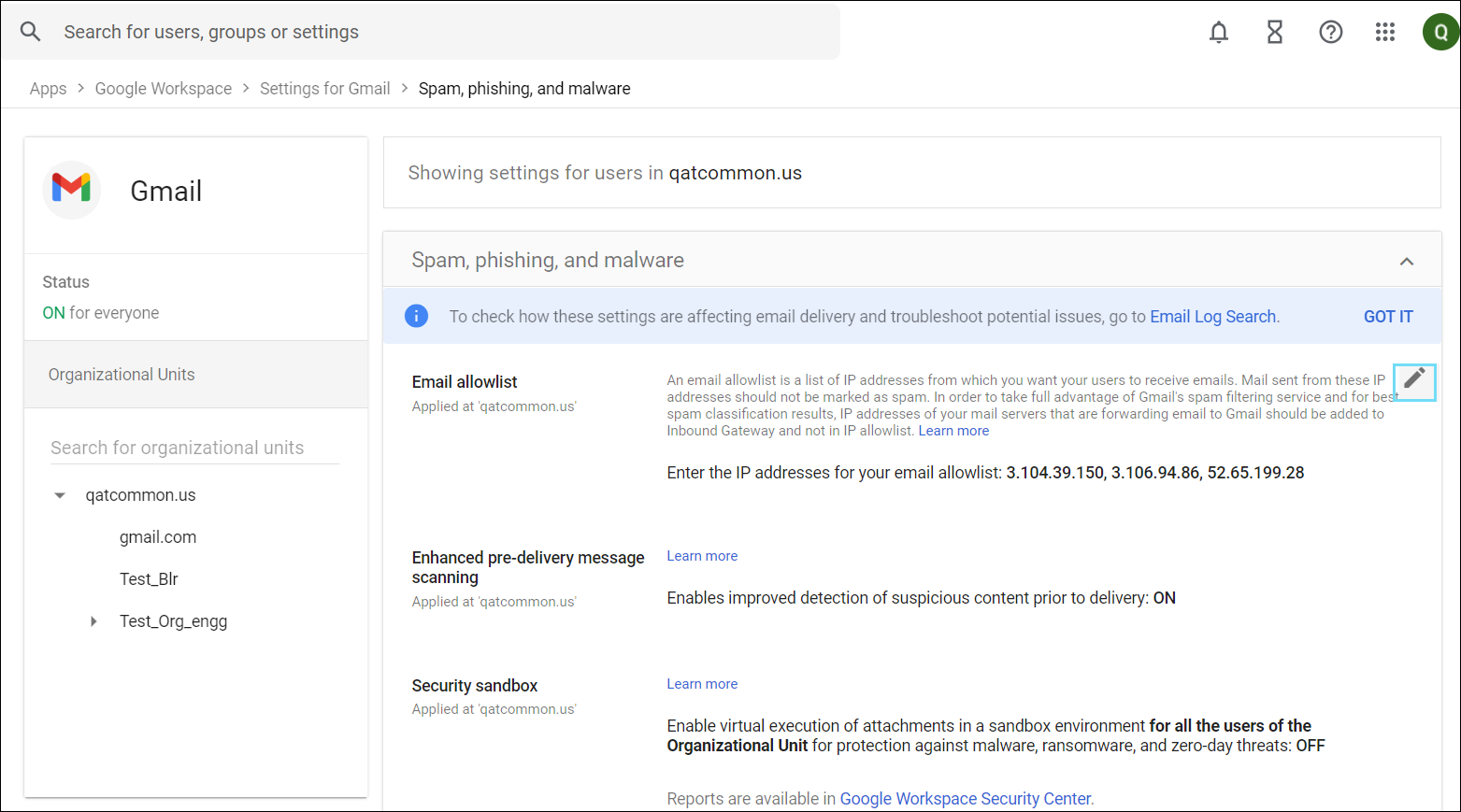
- Add the IP addresses that were added in Step 12 based on your environment separated by commas.
- Click SAVE.
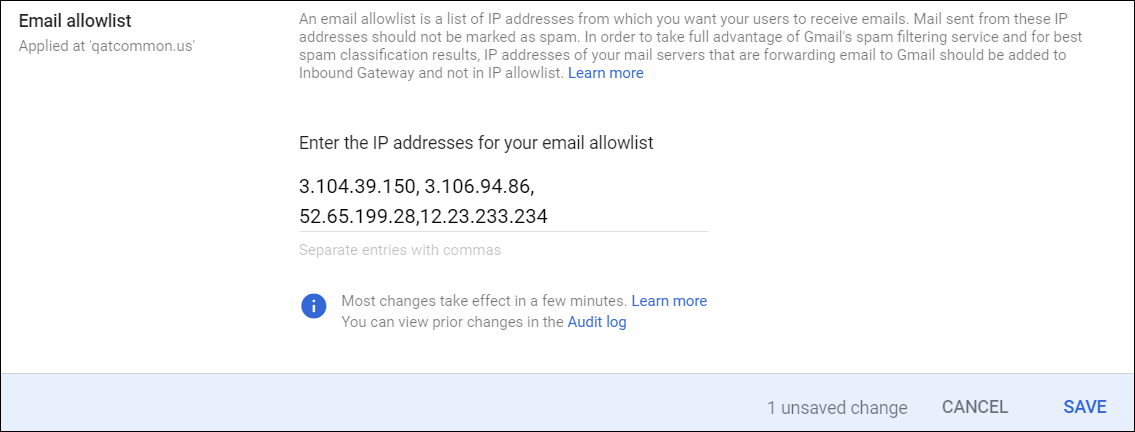
- Once saved, you can view the following message.
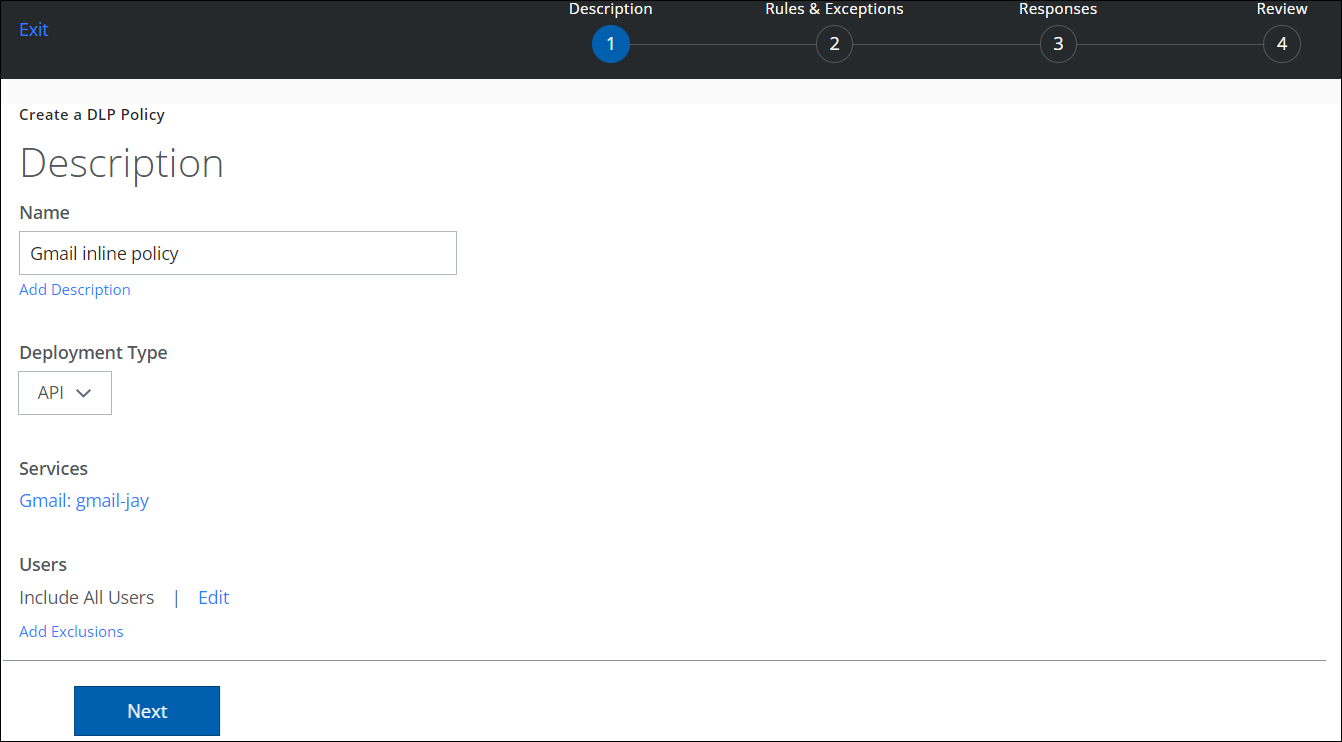
Step 3: Configure a DLP Rule
- Log in to Skyhigh CASB
- Go to Policy > DLP Policies and configure a new rule to Gmail. An example is shown below.
- Name. Enter the unique name for your DLP Policy.
- Deployment Type. Select API from the menu.
- Services. Select Gmail as the service instance you created earlier.
- Add the required rule for your DLP policy. For Example, select rule as Collaboration.
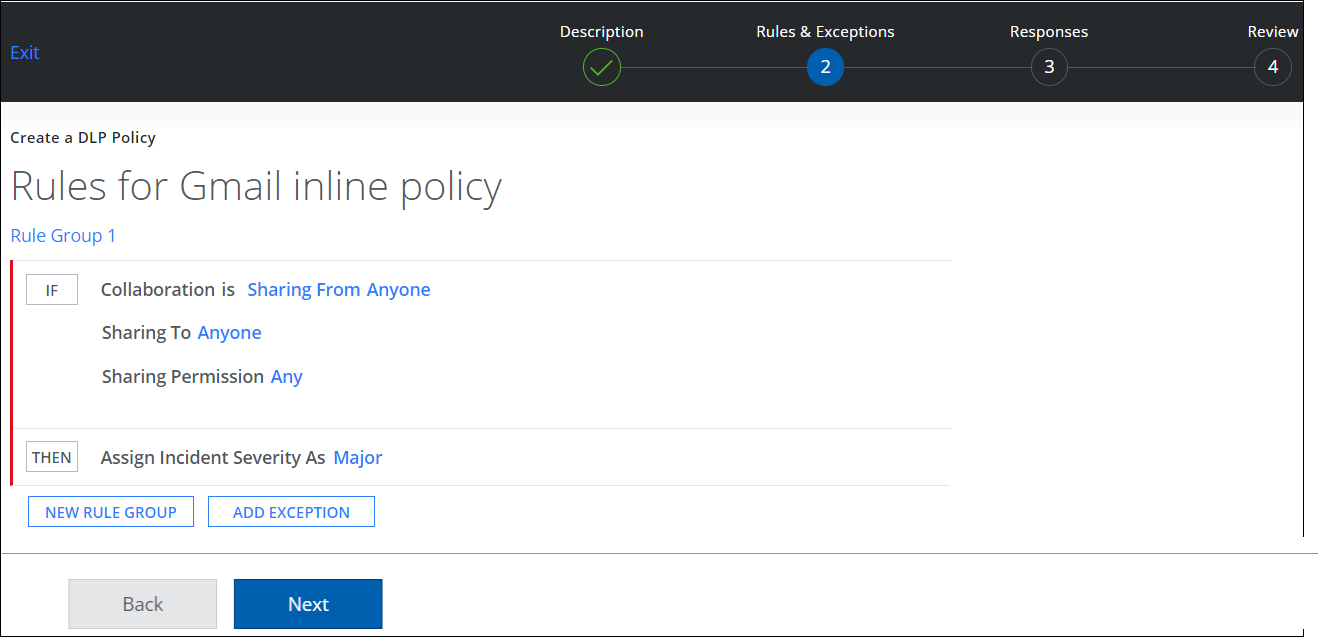
- Select the response to trigger when the DLP policy is violated. For example, select response as Block Email.
NOTE: The only response actions supported are Generate Incident or Block Email.
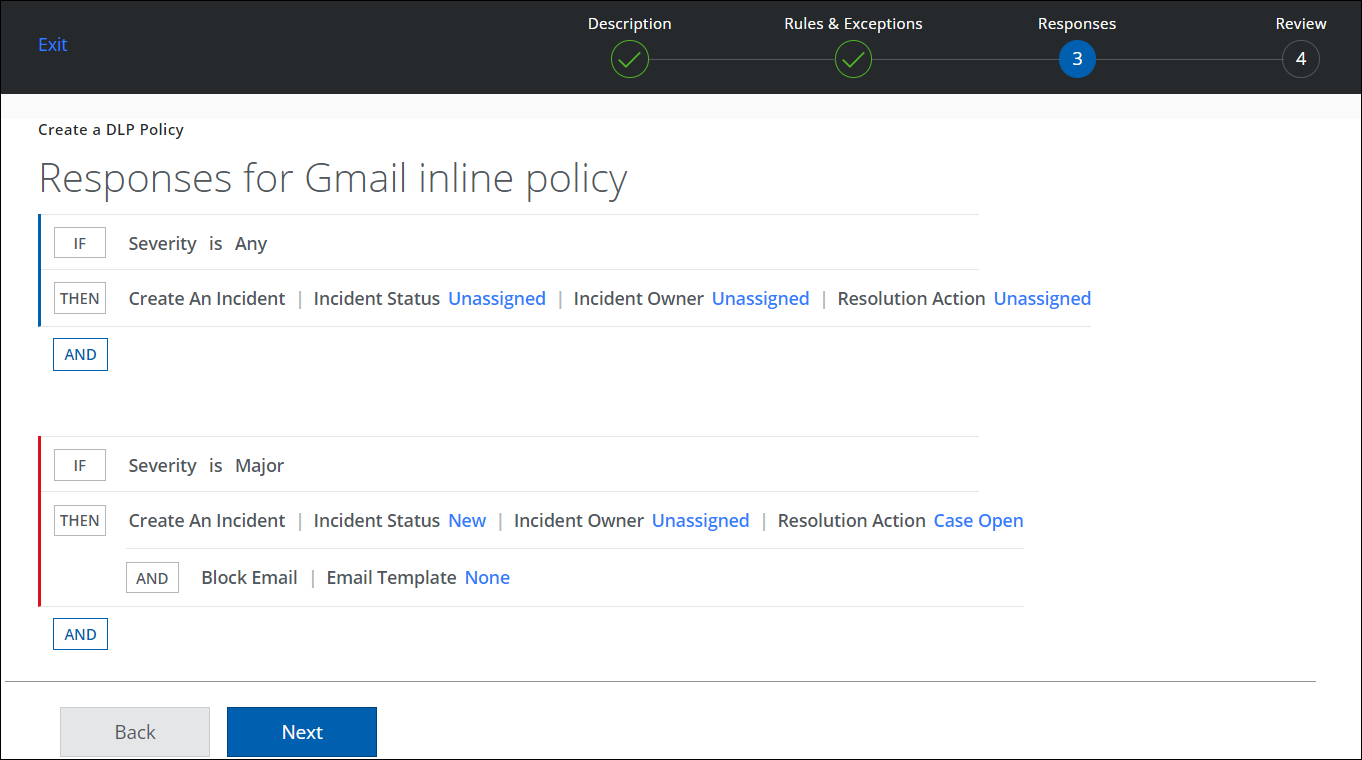
- Review and activate the new DLP policy and click Save.
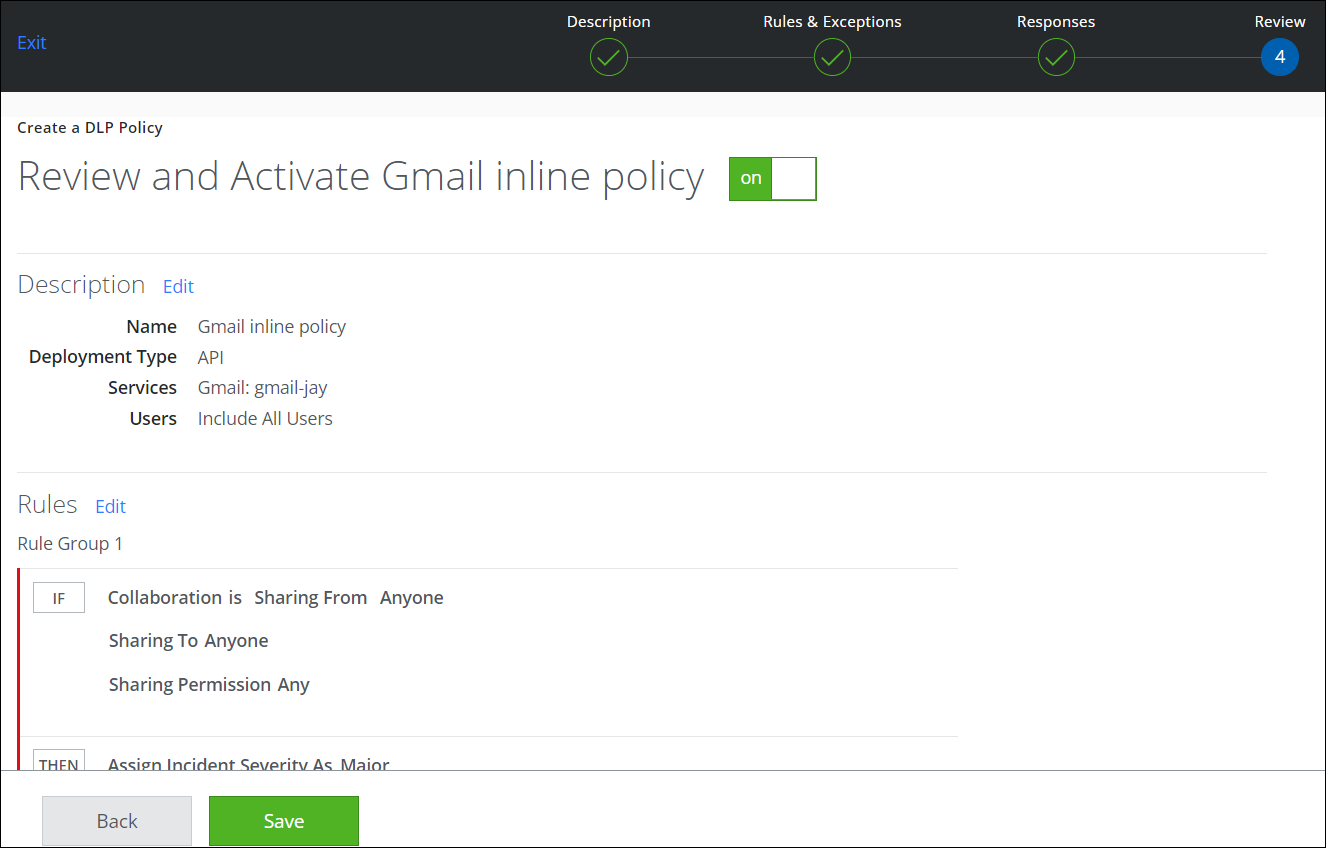
- The new DLP policy is created and saved on your DLP Policies page.
NOTE: The only actions supported are Generate Incident or Block Email.
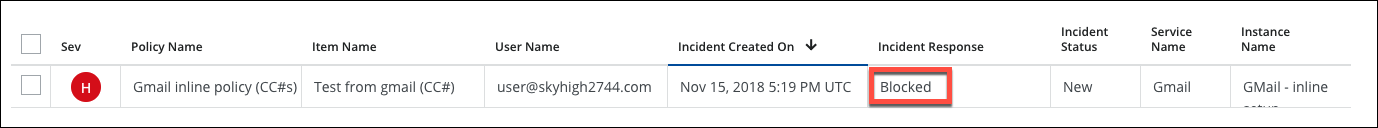
Step 4: Test the Configuration
- Log in to Gmail using a user account, and send an email with content that will trigger the configured DLP rule.
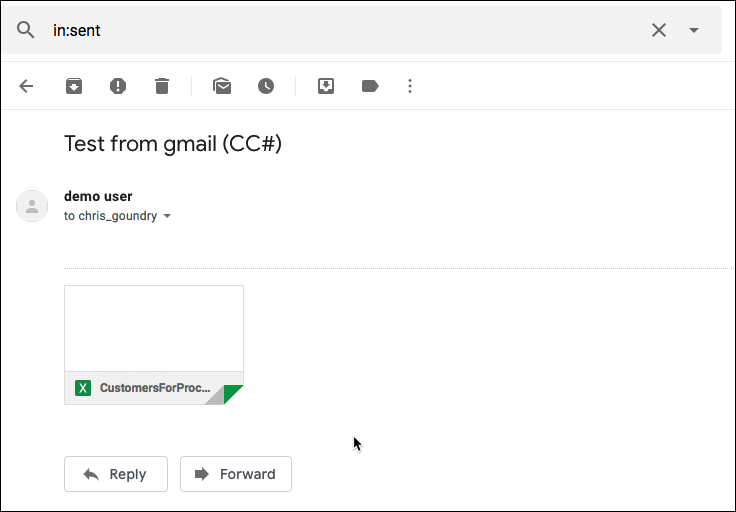
- Confirm that the email is NOT received by the recipient.
- Confirm that a policy incident is created and the action blocked the email.