About Match Highlighting and Match Obfuscation
Match Highlighting
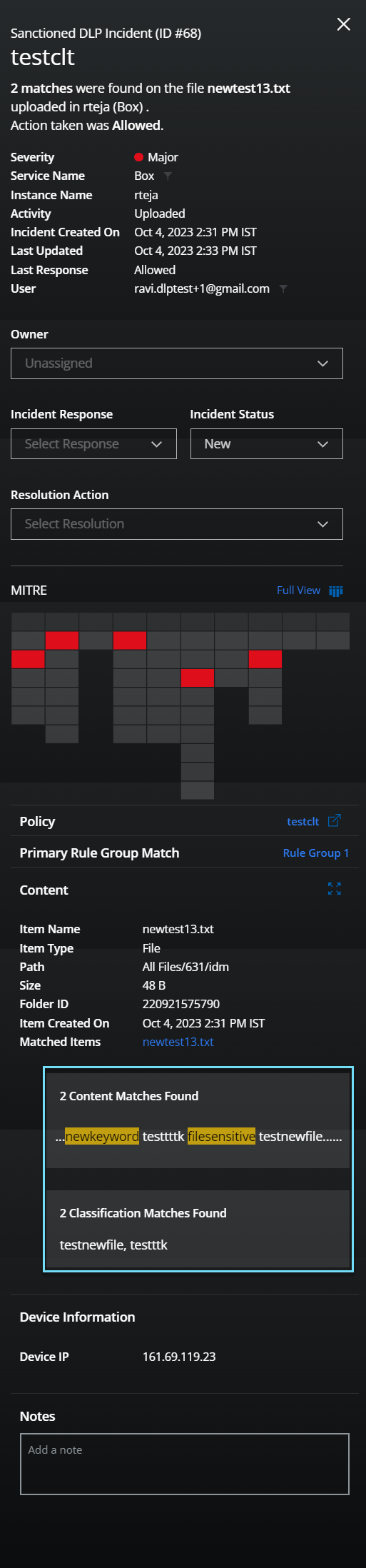
Match Highlighting displays an excerpt of a document when it includes content that violates a Data Loss Prevention policy. Incident response teams can view the text that contains the match for the DLP rule; surrounding text is included with the highlighted matches to help identify false positives. Match Highlighting provides evidence for DLP incidents.
When a policy violation involving the document’s contents occurs, the Policy Incidents Cloud Card displays the specific violation under Content. Only 50 matches will be displayed for any single policy violation at a time.
To manage your DLP policies, Skyhigh Security offers Match Highlighting for classification matches. Let's say, you have set up two classifications with different criteria, such as Data Identifiers and Advanced Patterns, and defined specific keywords for each classification. DLP policies evaluate the content for each classification and look for matches. If a match is found, the corresponding DLP policy will trigger and highlight the matched keywords on the Policy Incident Cloud Card. You can also view the Classification name that triggered the DLP Policy. This feature is designed to make it easier for you to identify potential security issues and act upon them promptly.
You can disable Match Highlighting at any time. Disabling match highlighting does not delete matches. You can disable and re-enable highlighting and preserve any matches as long as no other changes were made to the data in storage. You can delete your saved matches at any time by deleting them from storage.
For Match Highlighting data storage, you can use Skyhigh Security data storage, Microsoft Azure, IBM Cloud, or Amazon Web Services (AWS). For details on configuring data storage, see Data Storage. For Skyhigh Security data storage, your data is purged after 100 days.
Match Obfuscation
If you enable Match Obfuscation, Skyhigh CASB masks data that matches the form of PII data identifiers. This protects highly sensitive data from others in your organization who have access to Skyhigh CASB but should not see such data. Because data is masked, it cannot be reverted to non-obfuscated data.
IMPORTANT: If you choose to use Skyhigh Security storage for Match Highlighting, then you must enable Match Obfuscation. If you provide your own data storage for Match Highlighting, then selecting Match Obfuscation is optional.
Enable Match Highlighting
For details, see Enable Match Highlighting and Match Obfuscation.
FAQ
Where is Match Highlighting data stored?
Strings or values that trigger policy violations are written directly to the data storage you configure. As this is input by you and encrypted, Skyhigh CASB does not have access to the secret key which is controlled exclusively by you.
Is data encrypted in transit?
Skyhigh CASB’s DLP scan engine uses TLS 1.2 to protect all data in transit to data storage.
Is data encrypted at rest?
Before transmitting the Match Highlight data, Skyhigh CASB uses AES 256 encryption in Galois/Counter block cipher mode to encrypt the Match Highlighting data. This is implemented by using the BouncyCastle Java crypto library.
Does Skyhigh Security manage data after it is written to data storage?
Aside from using the provided account to read the data into the Match Highlighting policy violation view, Skyhigh CASB does not manage the data. When an incident is deleted, corresponding Match Highlights are deleted as well. If a policy archival process is in place and you want to delete the records, you would need to do this manually. For information, contact Skyhigh CASB Support.
If you're using Match Obfuscation and Skyhigh Security data storage, obfuscated data is stored in a bucket that is provided and owned by Skyhigh Security. This data is protected in with server-side encryption, application-side encryption (policy engine), tenant-specific keys (KMS), and is access-restricted for Skyhigh Security personnel.
IMPORTANT: If you do not want to have your organization's data stored in Skyhigh Security, do not select Skyhigh Security Data Storage.
Limitations
Incomplete Data Identifiers are Not Obfuscated
There is a limitation in Match Obfuscation where incomplete data identifiers may not be completely obfuscated in the Match Highlighting the section of the Skyhigh CASB user interface. Because the data identifier is incomplete, there is no way to determine that the string matches a Social Security Number, credit card number, or other identifier. If this is a concern for your organization, configure your own data storage.

