Skyhigh CASB 6.1.1 Release Notes (August 2022)
Shadow Cloud Services Monitoring
Skyhigh Security allows you to manage user activities for all shadow cloud services in the Skyhigh Cloud Registry. Skyhigh Security detects user activities across all shadow cloud services using generic or custom signatures and determines whether the user activity should be blocked based on the web policy settings.
NOTE: Users with Secure Web Gateway Cloud license can access these features in the Skyhigh CASB dashboard.
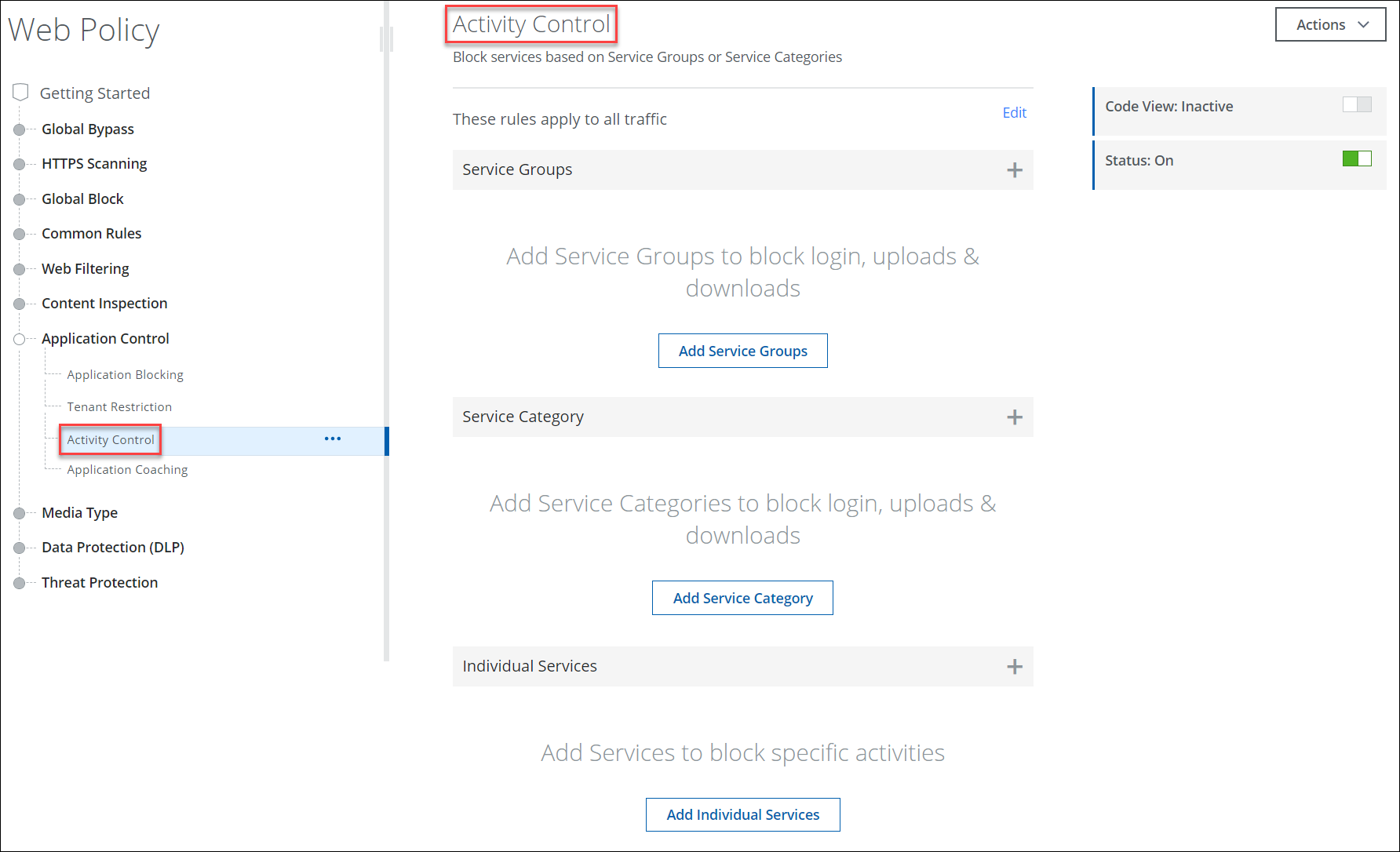
Activity Control for Shadow Cloud Services
Skyhigh CASB provides you fine-grained control over user activities for all shadow cloud services in the registry. The Activity Control page/ruleset (found under Policy > Web Policy > Policy > Web Policy tree > Application Control > Activity Control) allows you to configure your web policy to restrict user activities based on service groups, service categories, and individual services. You can use activity control to protect your users from threats such as viruses and malware that can be obtained via unauthorized web access. For details, see About Activity Control.
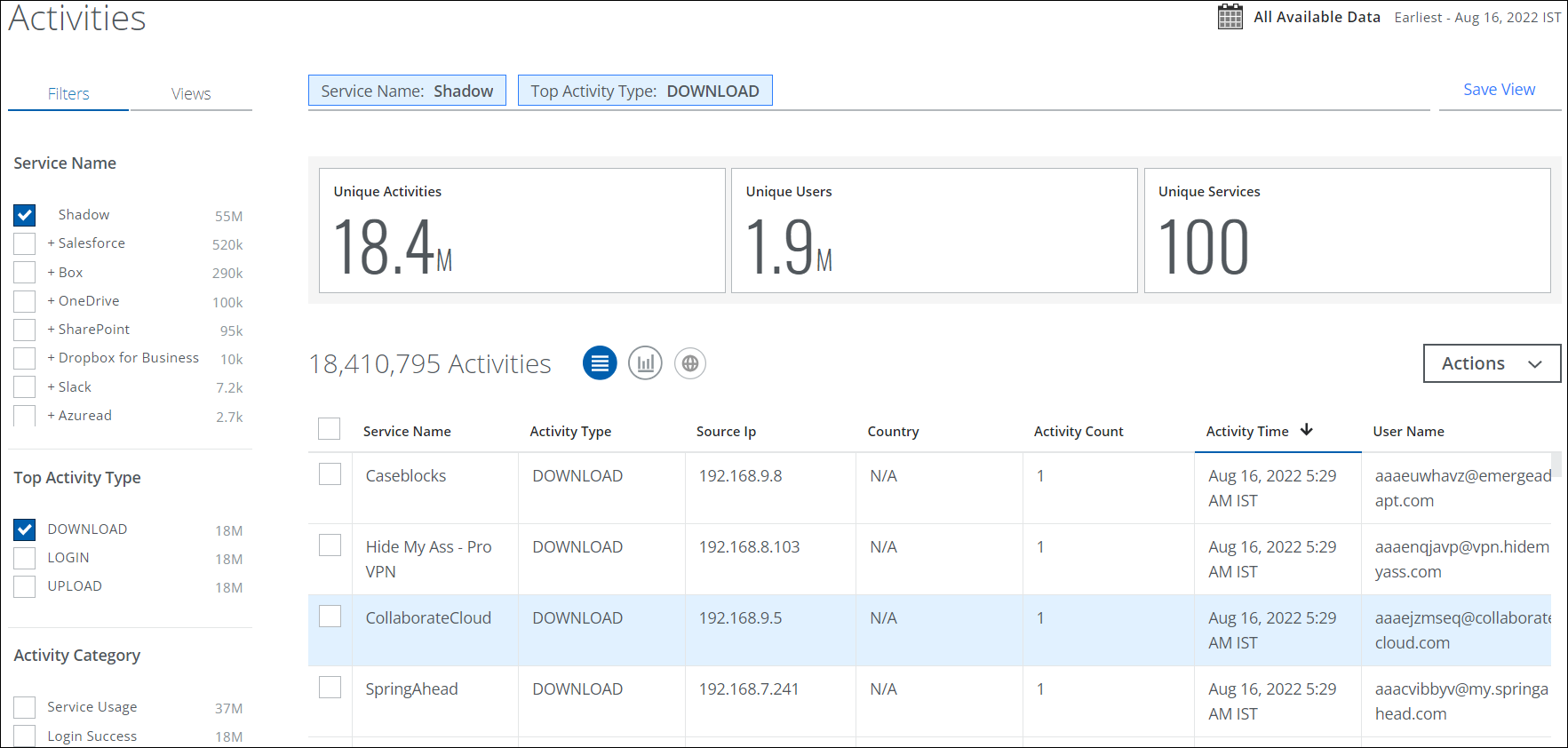
Activity Monitoring for Shadow Cloud Services
Skyhigh CASB provides you visibility into a user's download, login, and upload activities on any shadow cloud service in the registry. The Activities page (found under Incidents > User Activity > Activities) allows you to monitor user activities for shadow cloud services and view the user activity details associated with a user based on the selected activity type. You can use activity monitoring to protect your users from risky activity trends. For details, see Monitor User Activities for Shadow Cloud Services.
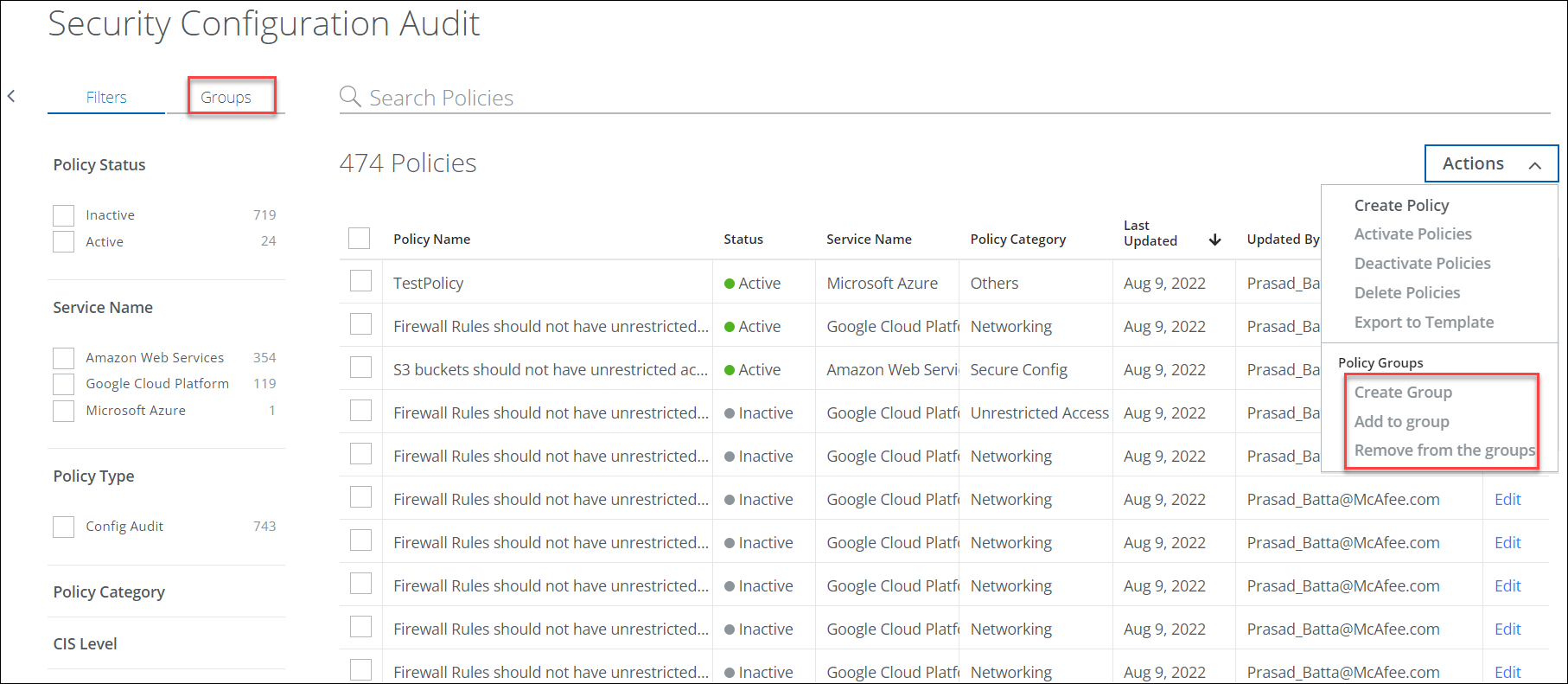
Security Configuration Audit Policy Groups
The Security Configuration Audit page (found under Policy > Configuration Audit) provides Policy Groups where you can aggregate and save the custom config audit policies into specific group. Additionally, you can edit or delete the policy group, add new policies, and remove policies from the group. This feature is supported only for IaaS services (AWS, Azure, GCP) and now available for all customers. For details, see About CSPM Security Configuration Audit.
The Policy Groups intended use case is to create and run Custom Configuration Audit Scan for the selected policies on the Policy Group. This use case is not supported in the current release but will be available in future releases.
New and Updated Amazon EKS Container Policies
We have added eight new Amazon EKS Policy Templates, and 18 others are updated and improved for Docker and Containerd.
- EKS Docker Host policy templates have been renamed EKS Container Host. Rules and exceptions were added for both Docker and Containerd. They will evaluate rules based on runtime or container, whichever is applicable.
- Docker and Containerd remediation steps have been added to the Incident Cloud Card to guide you through resolving incidents. Now you can determine which runtime is raising a violation under the Marked Attributes parameter. For details, see Policy Templates for EKS.
Note: This change is available for new customers now, and will be available for all customers in the next release.
Policy Templates for Azure Updated and Deprecated
Azure Microsoft Defender has updated and deprecated multiple security recommendations. For a list of Policy Templates that have recently been updated due to changed recommendations, see Find New and Updated Policy Templates. For deprecated Policy Templates, see Policy Templates for Azure - DEPRECATED.
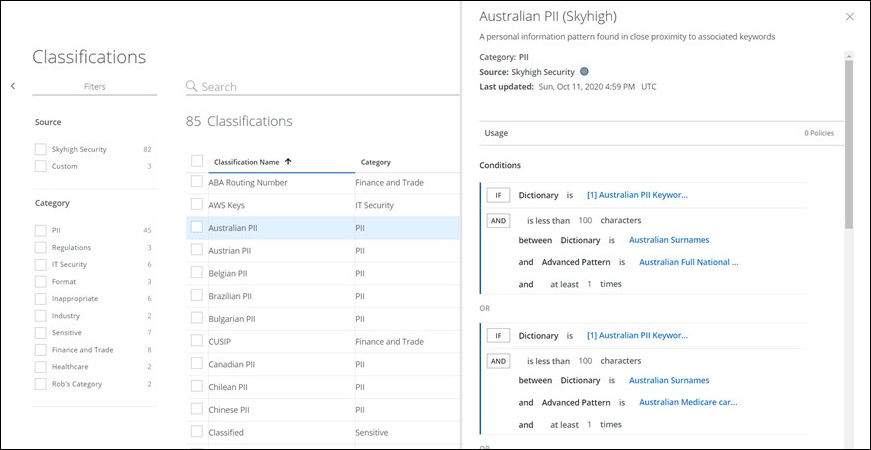
Classifications Page Redesign
The redesigned Classifications page (found under Policy > DLP Policy > Classifications) helps customers define their Classifications to be used in DLP policies to prevent sensitive data from leaving their organization. The new Classifications page provides all previous Classifications actions, plus powerful new search and filtering features. It also provides access to the redesigned Classifications Editor, which quickly and easily guides you in creating your DLP policies. This feature is now available for all customers. For details, see About Classifications.