Remediate CSPM Policy Incidents
- Last updated
- Save as PDF
Skyhigh CASB allows you to automatically remediate all incidents that are triggered when a Cloud Service Provider's Configuration policy is violated.
These are the following states of the incidents along with their description:
- Archived. An incident is marked Archived if the incident is no longer valid. This could happen if the entity that triggered the violation (such as a user) is deleted from the Service Provider.
- Escalated. An incident is marked escalated when it is moved to the next level of review.
- False Positive. When an incident is manually changed to False Positive status, it won't change back even when a new scan finds a violation for it.
- New. When an incident is found for the first time in a scan, it is marked as a new incident.
- Open. An incident is marked opened when it is resolved on the dashboard but found again in the scan.
- Pending. An incident is marked pending when it is pending review.
- Resolved. Incidents are marked Resolved if the configuration that caused the incident is resolved by a member of your team.
- Suppressed: When an incident is manually changed to Suppressed status, it won't change back even when a new scan finds a violation for it.
NOTE: Suppressed is not listed in the UI, but you can search for it in the Omnibar.
- Suspended. The incident has been suspended.
- Under Investigation. An incident is marked Under Investigation when it is being actively reviewed.
- Viewed. An incident is marked Viewed when it has been viewed for review, but not otherwise categorized.
Skyhigh CASB scans once in every 24 hours, so incidents are updated every 24 hours.
When AWS policy incidents are generated, you can view those incidents and the recommended remediation steps in Skyhigh CASB.
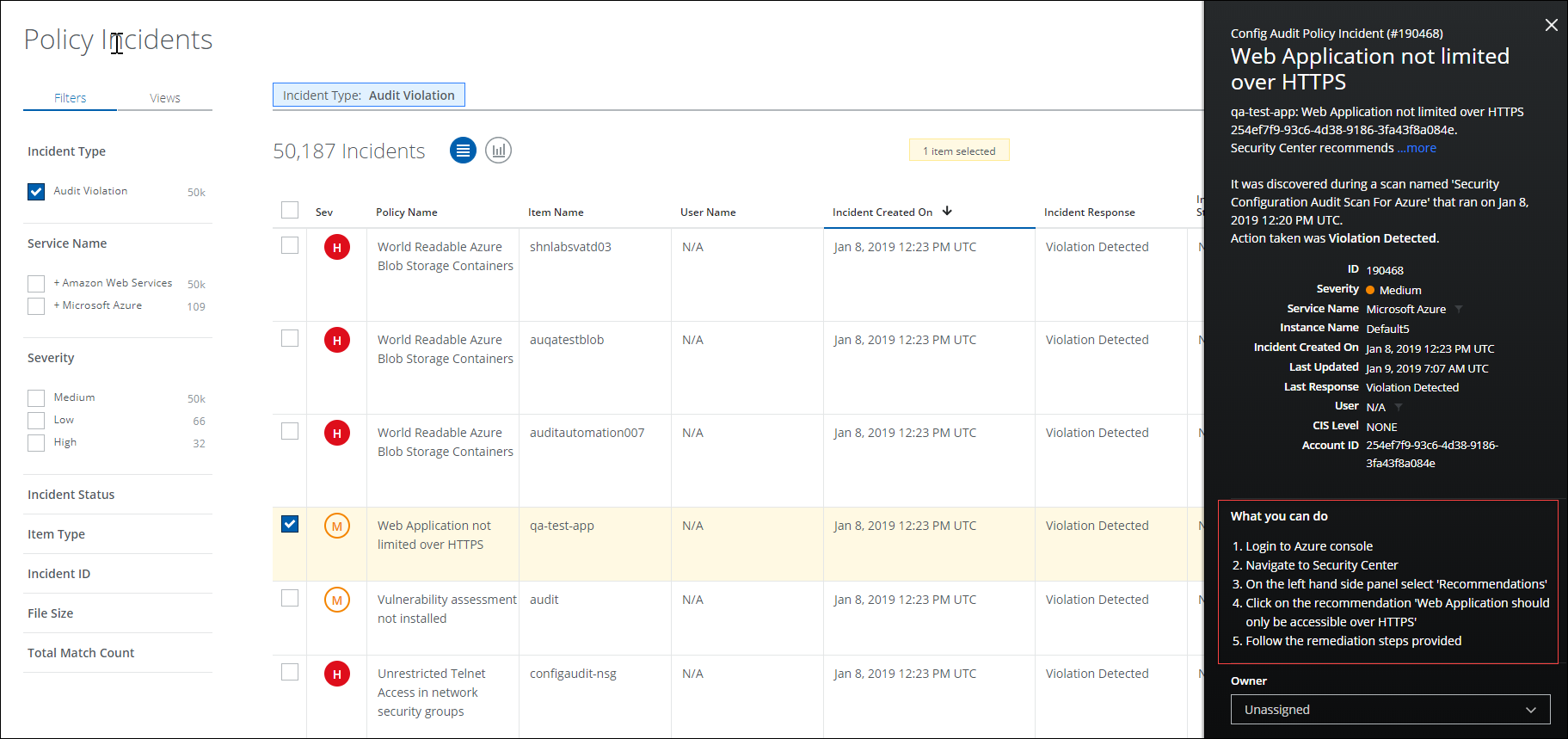
To view AWS incident remediation steps:
- Go to Incidents > Policy Incidents.
- Find the incident and click the row to show the Cloud Card.
- Follow the steps displayed under What you can do.
The refresh feature is used to view the most recent AWS violations on the Policy Incidents page. You can use this feature to refresh an AWS incident in real-time. You can also refresh incidents created from Custom Configuration Audit policies.
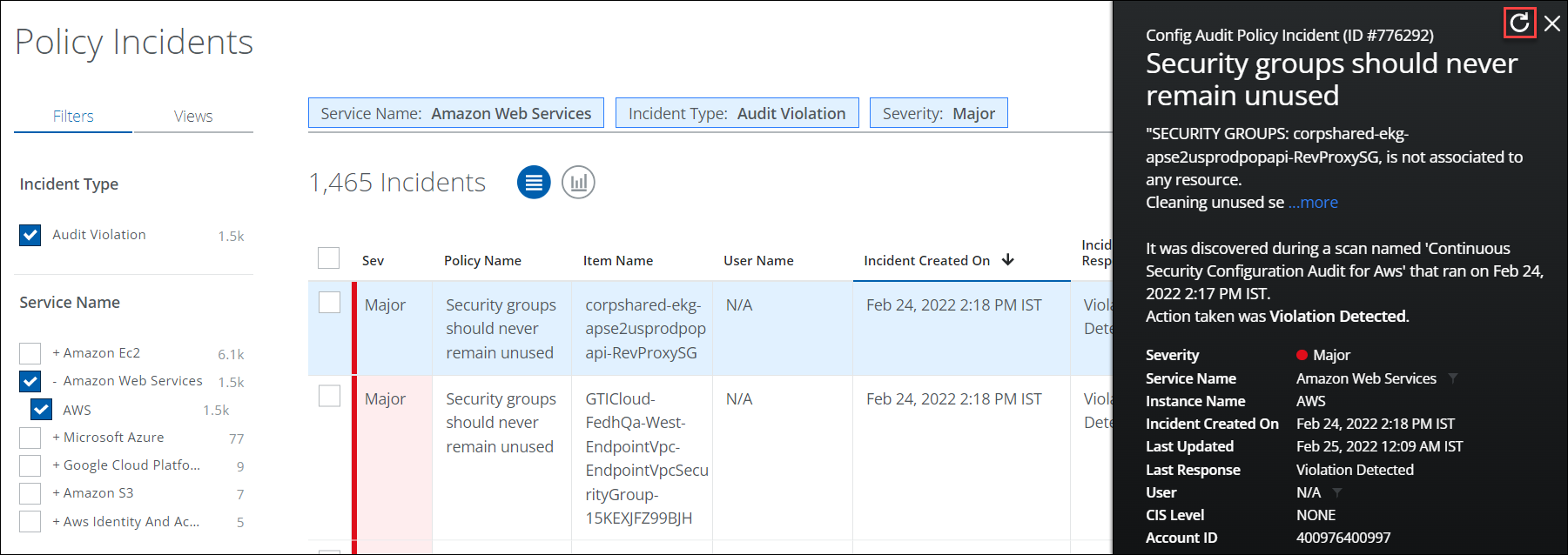
- Go to Incidents > Policy Incidents.
- Filter for Incident Type > Audit Violation, and Service Name > AWS.
- Click any incident in the table to view the Cloud Card for the specific incident.
- On the Cloud Card, click Refresh.
- A status message is displayed on the Cloud Card as the account is rescanned.
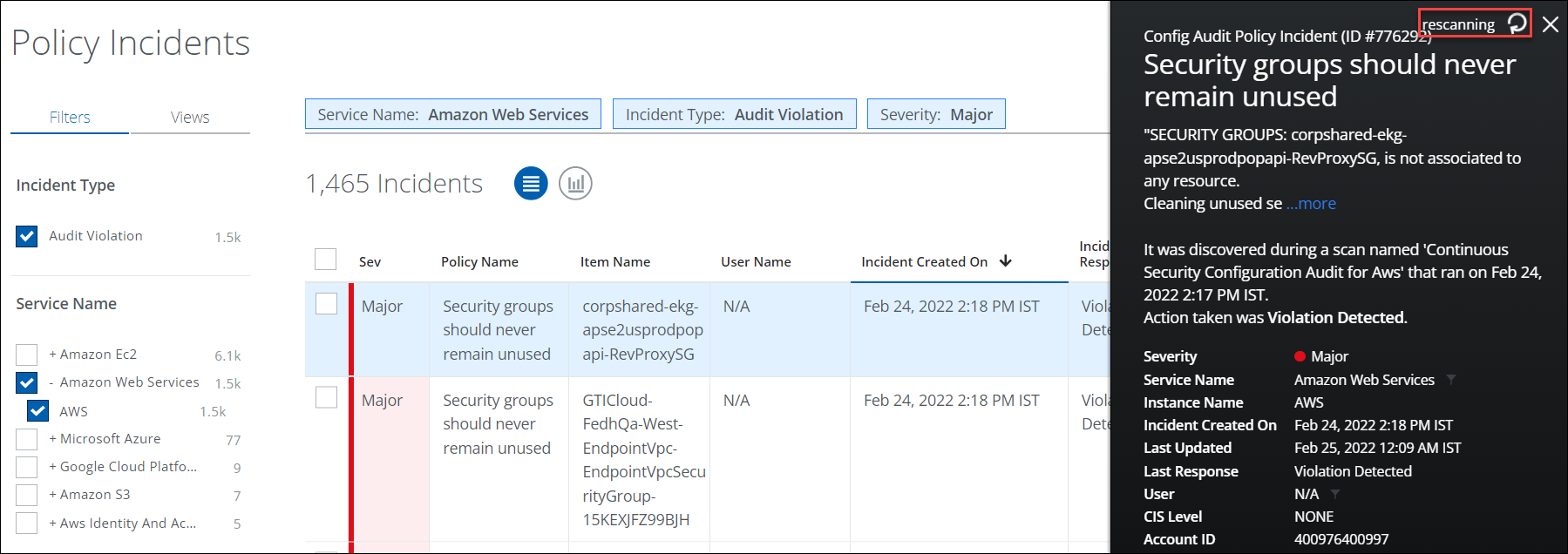 Any updates to the violation are displayed once the scan is complete.
Any updates to the violation are displayed once the scan is complete.

