Deploy the CWPP Functions on VMs, Clusters, and Containers
The CWPP Agent, or functions, can be installed in different ways on Virtual Machines (VMs), clusters, and in containers. This topic lists some of the ways you can deploy it.
Deploy CWPP Agent on Virtual Machines
For Virtual Machines, Skyhigh Security supports using packages to be installed with package managers such as YUM and dpkg:
- .rpm (for example, CWPAgent-1.5.0-1061.x86_64.rpm)
- .deb (for example, CWPAgent-1.5.0-1061.x86_64.deb)
To install on VMs, use the following command:
ubuntu@ip-172-31-28-242:~$ dpkg -i CWPAgent-1.5.0-316.deb
Deploy CWPP Agent in a Container
Skyhigh Security supports the CWPP Agent in container form, for example, nanosecco/cwpagent:1.5.0.803.
If your workload constitutes AWS clusters such as Amazon ECS and EKS, Azure AKS, or Google Cloud Platform GKE, then we recommend that you deploy to a container.
The CWPP Agent container can be deployed in three modes: DaemonSet, Sidecar, and Fargate.
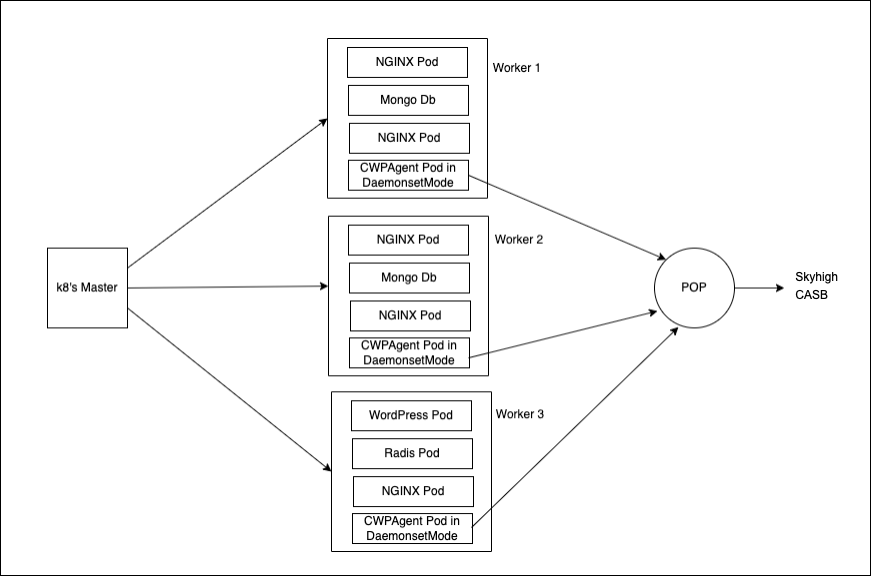
DaemonSet Mode
In DaemonSet mode, a single container or pod of the CWPP Agent runs per secondary node. For example, if you have a cluster with five secondary nodes, then each secondary node will run one instance of the CWPP Agent, and it will monitor all the instances of pods or containers running on that particular secondary node.
If you want to monitor all the containers running in a cluster, or to know when the cluster administrator doesn’t have control over what pods or containers are running in the cluster, for example, in Dev/Test environments, then we recommend deploying the CWPP Agent in DaemonSet mode.
k8daemonset-cwp-agent.yaml:
apiVersion: apps/v1
kind: DaemonSet
metadata:
name: cwp-agent
spec
selector:
matchLabels:
app: cwp
template:
metadata:
labels:
app: cwp
spec:
containers:
- name: cwp-agent
image: nanosecco/cwpagent:1.5.0.803
imagePullPolicy: Always
env:
- name: CWPP_CLUSTER_NAME
value: ${CWPP_CLUSTER_NAME}
volumeMounts:
- name: docker-data
mountPath: /var/lib/docker/
- name : dockersock
mountPath: /var/run/docker.sock
- name : dockershim
mountPath: /var/run/dockershim.sock
- name : contrd
mountPath: /run/containerd/
- name : criosock
mountPath: /run/crio/crio.sock
- name: cwpp-host-mount
mountPath: /opt/.../cwpagent/cwpp-host-mount
readOnly: true
- name : certs
mountPath: /opt/.../certs
volumes:
- name : docker-data
hostPath:
path: /var/lib/docker/
- name : dockersock
hostPath:
path: /var/run/docker.sock
- name : dockershim
hostPath:
path: /var/run/dockershim.sock
- name : contrd
hostPath:
path: /run/containerd/
- name : criosock
hostPath:
path: /run/crio/crio.sock
- name: cwpp-host-mount
hostPath:
path: /
- name: certs
configMap:
name: cicdcerts
defaultMode: 0755
imagePullSecrets:
- name: nanosecco
Use the command:
Cmd: kubectl apply -f k8daemonset-cwp-agent.yaml
Sidecar Mode
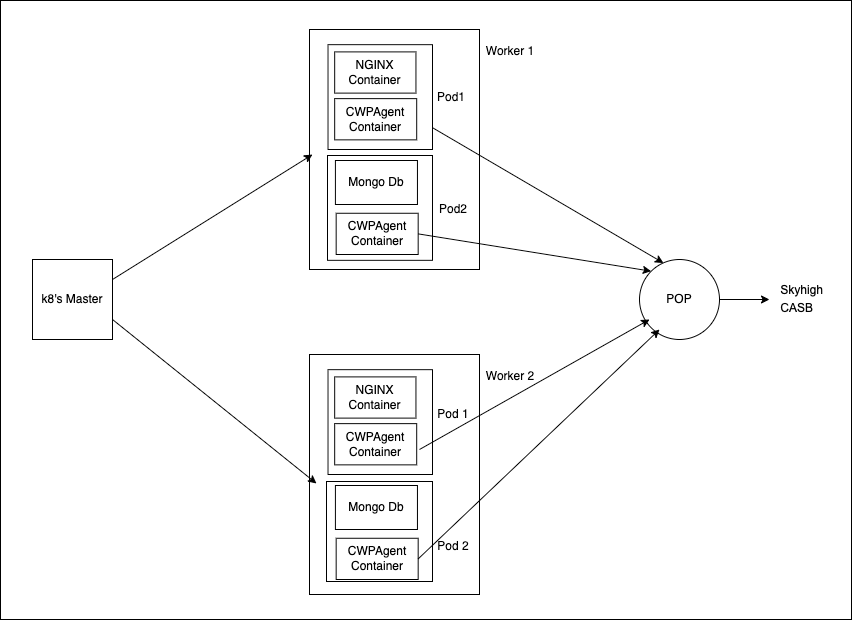
In Sidecar mode, the CWPP Agent container runs along with the application container. So, each instance of the application container has a CWPP Agent container attached to it.
If you want to monitor only specific applications and not all the containers running in a cluster, then we recommend deploying the CWPP Agent in Sidecar mode.
k8sidecar-cwp-agent-sample.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-deployment
labels:
app: nginx
spec:
selector:
matchLabels:
app: nginx
replicas: 1
template:
metadata:
labels:
app: nginx
spec:
volumes:
- name: mvc-certs
configMap:
name: cicdcerts
- name : docker-data
hostPath:
path: /var/lib/docker/
- name : dockersock
hostPath:
path: /var/run/docker.sock
- name: cwpp-host-mount
hostPath:
path: /
containers:
- name: nginx
image: nginx:latest
- name: cwpagent
image: nanosecco/cwpagent:1.5.0.803
imagePullPolicy: Always
env:
- name: CWPP_CLUSTER_NAME
value: ${CWPP_CLUSTER_NAME}
volumeMounts:
- name : mvc-certs
mountPath: /opt/.../certs
- name: docker-data
mountPath: /var/lib/docker/
- name : dockersock
mountPath: /var/run/docker.sock
- name: cwpp-host-mount
mountPath: /opt/.../cwpagent/cwpp-host-mount
imagePullSecrets:
- name: nanosecco
Use the following command:
Cmd: kubectl apply -f k8sidecar-cwp-agent-sample.yaml
AWS Fargate Mode
If you are using serverless computing with EKS Fargate to deploy containers, then you can inject the CWPP Agent into the application container and start it as shown in this configuration.
k8fargate-cwp-agent-sample.yaml:
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-deployment
labels:
app: nginx
spec:
selector:
matchLabels:
app: nginx
replicas: 3
template:
metadata:
labels:
app: nginx
spec:
volumes:
- name: mvc-pkg
emptyDir: {}
- name: mvc-certs
configMap:
name: cicdcerts
- name : docker-data
hostPath:
path: /var/lib/docker/
- name : dockersock
hostPath:
path: /var/run/docker.sock
- name: cwpp-host-mount
hostPath:
path: /
containers:
- name: nginx
image: nginx:latest
env:
- name: CWPP_CLUSTER_NAME
value: ${CWPP_CLUSTER_NAME}
command: ["/bin/sh","-c"]
args: [ 'cd /mvc-store && bash CWPAgent-service.sh install && nginx -g "daemon off;"']
volumeMounts:
- name: mvc-pkg
mountPath: /mvc-store
- name: docker-data
mountPath: /var/lib/docker/
- name : dockersock
mountPath: /var/run/docker.sock
- name: cwpp-host-mount
mountPath: /opt/.../cwpagent/cwpp-host-mount
initContainers:
- name: cwpagent
image: nanosecco/cwpagent:1.5.0.803
imagePullPolicy: Always
command: ["/bin/sh","-c"]
args: [ 'bash CWPAgent-service.sh build && ls -lrt /mvc-store']
volumeMounts:
- name: mvc-pkg
mountPath: /mvc-store
- name : mvc-certs
mountPath: /opt/.../certs
imagePullSecrets:
- name: nanosecco
Use the following command:
Cmd: kubectl apply -f k8fargate-cwp-agent-sample.yaml

