About File Integrity Monitoring
When installed with the CWPP Agent, the File Integrity Monitoring (FIM) plugin validates containers and virtual machines to assure compliance for files against a known good baseline. If the agent is installed and the plugin is running on the managed resource, the validation is automatic. No scan is required. Skyhigh CASB supports FIM for files managed by cloud workloads.
FIM is supported for AWS, Amazon Elastic Kubernetes Service (EKS), Microsoft Azure, Azure Kubernetes Service (AKS), Google Cloud Platform (GCP), and Google Kubernetes Engine (GKE).
File Integrity Policies Page
FIM policies are managed on the Policy > File Integrity Policies page.
To create a FIM policy, see Create a File Integrity Monitoring Policy.
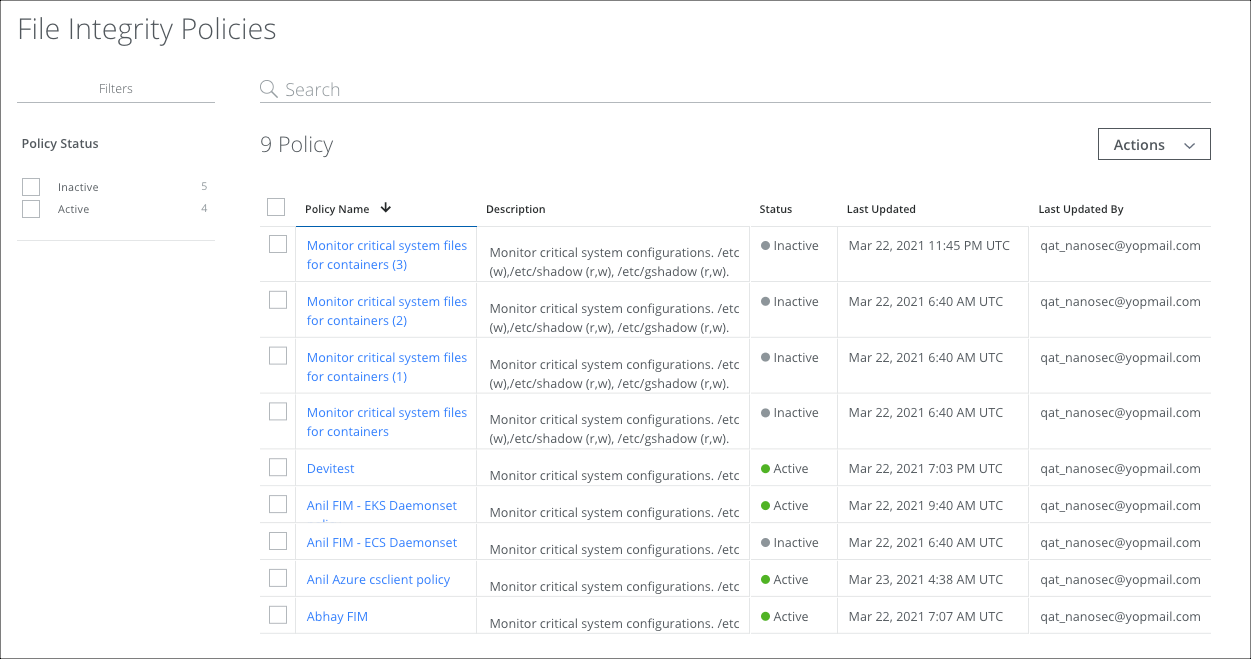
The File Integrity Policies page provides the following actions and information:
- Filters. Select options on the Filters tab to scope down your search.
- Search. Search via the Omnibar.
- Actions. Click Actions to:
- Activate Policy
- Deactivate Policy
- Delete Policy
- Settings
- Edit Table Columns
- Policy Name. Displays the name of the DLP Policy. Click the link to edit the policy.
- Description. (Optional.) Display the description of the DLP Policy.
- Status. Displays the status of the policy: Active or Inactive.
- Last Updated. Displays the date and time that the policy was last updated.
- Last Updated By. Displays the username that last updated the policy.
FIM Policy Incidents are reported on the Policy Incidents Page.
FIM Resources are displayed on the Resources Page.

