About On-Demand Scans
On Demand Scans (ODS) support targeted investigations and continuous audits of sensitive data at rest, allowing you to examine cloud services for any content that violates your DLP and malware policies. Skyhigh ODS provides flexible and efficient scanning to detect data security violations without impacting inline traffic performance. Delta scans when scheduled provide utmost efficiency in scanning only new data.
Skyhigh On Demand Scans give you a lot of flexibility to inspect various aspects of your deployment. You can create scans for a specific purpose by scanning more than one policy, which allows more than one remediation action. You can run an ODS against a targeted cloud service provider and run your scans immediately or schedule daily or weekly scans at convenient times.
- ► Benefits of On Demand Scan
-
On-Demand Scan applicable to:
- Skyhigh CASB use cases only and Shadow IT use cases are not supported
- Skyhigh CASB scans all data where NRT cannot see older data
- Account for retroactive actions for policy revisions or changes
- Prompts admins to run a scan for the risky users who are leaving organizations
- Compliance use cases
- ► Examples of On Demand Scans
-
When you first configure your tenant, run an On-Demand Scan to set a baseline for activity in your cloud services.
- For example, you could limit scans to new or updated files for malware each time it performs a scan, or just for specific users or folders.
- Another example, you can scan for specific users before they are off-boarded.
- ► About ODS File Storage and Supported Deployment Modes
-
- During an On-Demand Scan, files are processed in Skyhigh CASB to inspect sensitive content, and the files are deleted immediately after processing. Your files are never stored in Skyhigh CASB.
- On-Demand Scans are only available with API-based deployments. Proxy-based deployments are not compatible with On-Demand Scans.
- ► How On-Demand Scan Work?
-
During the scanning procedure, files undergo indexing. This indexing process involves analyzing the content of files, email messages, and other content stored in your cloud service, and categorizing them based on their information, including words and metadata. The scanning is done asynchronously, and it is carried out in batches using separate containers or compute resources assigned to individual users or dedicated resources. When scans are conducted in a process-wise manner, scans are focused on top-level items such as objects, users, and more. In case a scan is paused, it can be resumed from the point where it was paused. The system effectively manages rate limits by incorporating an auto-pause feature.
- ► On-Demand Scan Completion: What You Need to Know?
-
Once the ODS is completed, Skyhigh Security provides the following information:
- Incidents are generated. If your content violates the policy, the incidents are triggered on the Policy Incidents page.
- Scan Report. A scan report is not produced, however, the User Interface displays statistics on the scan, such as the amount of data scanned and the number of violations. There is no option to export a report.
- Scan History. Maintains the statistics of previous runs.
- ► Additional Information
-
- There are no limits on the amount of data that can be scanned in a day, and it is possible to perform multiple scans simultaneously.
- Currently, there is no specific date option available for scans, except for a few Cloud Service Providers (CSPs) that offer APIs to facilitate it. However, there is potential for us to incorporate a different approach in the future for other CSPs. Currently, you can specify a start date but not an end date.
For information about file size, see Manage the Size of On-Demand Scans. To create and manage On-Demand Scans, go to Policy > On-Demand Scan. For details, see About the Scans Page.
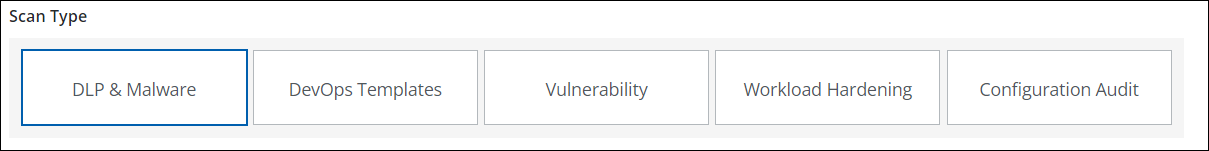
Scan Types
On-Demand Scans are powered by four other engines in addition to the DLP and malware policy engines. Five types of On-Demand Scans are run by different engines.
- DLP & Malware Scan. The DLP and Malware engine checks for content violations.
- DevOps Templates Scan. The Configuration Audit engine will check DevOps templates for policy violations. DevOps is a set of practices that combines software development (Dev) and IT Operations (Ops).
- Vulnerability Scan. The Container Vulnerability Scan engine checks Common Vulnerabilities and Exposures (CVEs) for policy violations. This is related to Containers.
- Workload Hardening. Workload Hardening Scan engine checks benchmarks for cloud workloads to secure the system, such as keeping installed software up-to-date, securing the file system, remediating network misconfigurations, and more.
- Configuration Audit. Configuration Audit allows you to discover and monitor the configuration of your IaaS cloud services, such as AWS, Azure, and GCP. Config Audit use cases support both DLP ODS and NRT DLP scans.
You can include more than one policy and more than one remediation action to create scans that return results for a specific purpose. You can schedule a scan to run once or regularly. You can also change the specified schedule at any time.
Secure Collaboration
You can use On-Demand Scans to detect folder/file collaboration events and make sure the proper remediation action occurs, supporting collaboration/sharing related remediation actions. In addition to removing shared links and modifying permissions, scans can support the following workflows:
- Folder Collaboration rules can be defined with File Content rules. That means if a user shares a folder, and then a file is uploaded with forbidden content, then any DLP policies are triggered and remediation actions are executed. Also, if a folder (or any of its subfolders) already contains a file with sensitive content, and then the folder is shared by the user, a DLP policy can be executed
- If a Shared Link rule is defined along with a File Content rule, DLP policies are executed if a user shares a file link and then updates the file with sensitive content, or if a user uploads a file with sensitive content and then shares the link for the file.
Supported Services
On-demand scans are only available with API-based deployments. Proxy-based deployments are not compatible with On-Demand Scans.
|
Legend: |
On-Demand Scan is available for the following Cloud Services:
| Types of CSPs | Availability | Available Cloud Services |
|---|---|---|
| File Based |  |
Box, Google Drive, Microsoft OneDrive, Sharepoint |
| Blob/Object-based |  |
Microsoft Azure, Google Cloud Platform, Amazon S3 |
| Message Based |  |
Microsoft Teams, Slack |
| Email Based |  |
Microsoft Exchange Online |
| Structured Based |  |
Microsoft Dynamics 365, Salesforce, ServiceNow |
| Specification Based (CASB Connect ) |  |
NA |
For Amazon S3, since there is no concept of a user, Skyhigh CASB scans documents by S3 bucket. For Azure, Blobs are scanned. For SharePoint, Sites are scanned. For all other services such as OneDrive, and Box, documents are scanned by the user.
NOTES:
- Google Drive does not provide file size information, so Skyhigh CASB cannot evaluate file size rules
- ODS is currently not compatible with Gmail since emails in Gmail are archived and there is currently no API integration available for Gmail.
On-Demand Scan Scope
Full Data Scope
To scan the full contents of a folder, use Full mode as the data scope, but only when needed, as it takes a long time. The first time you run a scan, you must use Full mode.
NOTE: We do not recommend scheduling content-based scans using the Full data scope, as it takes a long time for the scan to complete, and might generate duplicate incidents because the same content is scanned multiple times.
Incremental Data Scope
IMPORTANT: Incremental Mode behavior changed in Skyhigh CASB 3.9. Previously, if you modified a policy, the next scan would revert to Full mode automatically. As of Skyhigh CASB 3.9, this no longer happens. Incremental mode always only scans incrementally, except for the first time it is run.
Any delta scans that are conducted after the completion of a main scan is called incremental scan. To scan only changes that have occurred since the last scan, use Incremental mode as the data scope. Incremental scans run faster than Full scans.
Technically, the first time an Incremental scan is run, it always runs as a Full scan. Then after the first scan, each Incremental will always scan new documents from the last scan's start time. It does not pick up earlier documents.
During incremental scanning, files that have not been updated are skipped for scan. Instead, CSP is used to provide a list of files that have been modified after a specific timestamp. The CSP keeps a record of all the files that have already been scanned.
For example, if you run an On-Demand Scan in Incremental mode within the last 7 days, the first scan picks up documents from the last 7 days. Going forward, the scan always picks up newly added documents. It does not pick up documents from the last 30 days, even if you change the scan's data scope configuration.
NOTE: For Amazon S3 scans, the first time a scan is run, it uses Full mode. Subsequent scans always use Incremental mode. If new documents in a previously scanned S3 bucket are found during the scan, the scan continues as Incremental. If new S3 buckets are found during the scan, the new S3 buckets are scanned in Full mode. Subsequent scans of the new S3 buckets always use Incremental mode.
On-Demand Scan Configurations
Legend:  Supported Supported  Not Supported NA - Not Applicable Not Supported NA - Not Applicable |
The following table provides an overview of the supported scan configuration features for each CSP:
|
Scan Features |
Box |
OneDrive |
SharePoint |
Microsoft Exchange Online |
Google Drive |
|---|---|---|---|---|---|
| Full/Incremental |  |
 |
 |
 |
 |
| Scan only public content |  |
 |
 |
 |
 |
| Include/exclude users |  |
 |
 |
 |
 |
| Include/exclude Sites |  |
 |
 |
 |
 |
| Sent/Received/All Mail |  |
 |
 |
 |
 |
| Time-based filter |  |
 |
 |
 |
 |
| Scheduling |  |
 |
 |
 |
 |
Known Limitations and Best Practices
- Configure FULL Scan only for the first time to scan the historical content. Create INCREMENTAL scans after the FULL SCAN is done and disable Full Scan.
- Do not configure and run multiple FULL Scans, with the same scan configurations (which are duplicate scans).
- Follow the necessary steps before scanning large repositories:
- Define exclusions
- Start smaller segments (time or folder-based)
- Smaller set of users
- Always do scan estimation before scanning
- Use classifications in favor of DI in policies
NOTE: If you are using any third-party SharePoint add-on app to migrate on-premise files to Office 365 SharePoint sites or OneDrive, then DLP in NRT mode may not work. It is recommended to plan ODS scan/s after the migration is completed.
More Information
For more information, see:

