Secure Web Gateway Network IP Address Ranges to Allow in Access Lists
Secure Web Gateway uses the Global Routing Manager (GRM) service for intelligent routing, load balancing, and failover. Web traffic is routed to the best available Point of Presence (PoP), which is a geo-located entry point into the cloud.
To avoid issues with this traffic management, complete the following as needed:
-
Configure your firewall — If you have set up a firewall to protect your network, allow traffic to the inbound IP address ranges of the networks for the Points of Presence (PoPs) in the firewall access list.
This ensures access to the PoPs is not blocked by your firewall. - Configure access to business-to-business services — If you are running business-to-business services with business partners who restrict access based on source IP addresses, forward outbound IP address ranges of the networks for the Points of Presence (PoPs) to them, so they can enter these in their access lists.
This ensures you can connect to your business-to-business services through the PoPs.
A list of the IP address ranges you should allow in your firewall access list and forward to your business partners is provided on a status site, see Skyhigh Security Status. The list is available there under Setup > IP Addresses/Ranges.
In this list:
-
IP address ranges are marked according to whether they are used for inbound or outbound traffic, or for both.
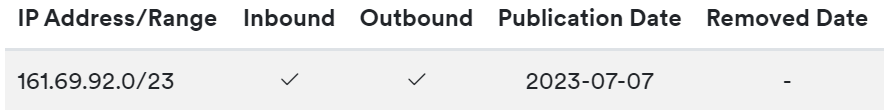
- IP address ranges of networks that have been deactivated are crossed out.
You can export this list as a file in .txt (for inbound or outbound IP address ranges), .cvs, or .json format.
A map that shows the physical location of the networks for our PoPs is also provided on this site, as well as information about statuses and maintenance windows.
Additional Lists of Network Parameters
In the following, two more lists of parameters you can use when configuring settings for our networks are provided. In these lists, you will find information about:
-
Protocol and ports for backend services
- IP address ranges for configuring access logging and other functions
List of Protocols and Ports for Backend Services
The following table lists network protocols and ports for backend services that are related to web filtering under Secure Web Gateway.
| Protocol | Port | Purpose |
|---|---|---|
| TCP | 80 | HTTP or HTTPS proxy: SCP, explicit, and forwarding |
| TCP | 8080 | HTTP or HTTPS proxy: SCP, explicit, and forwarding |
| TCP | 443 | HTTP or HTTPS proxy: forwarding |
| TCP | 8081 | SCP Secure Channel |
| TCP | 8084 | SAML authentication |
| UDP | 500 | IPsec |
| UDP | 4500 | IPsec |
| ESP | IPsec |
List of IP Address Ranges for Configuring Access Logging and Other Functions
The following table lists IP address ranges you can use to configure access logging and other functions under Secure Web Gateway, such as reporting or Hybrid policy synchronization.
Information about ports, physical location, and related DNS names is also provided.
| Physical location (major world region) | Physical location (country) | IP address range | Port | Purpose | Related DNS name |
|---|---|---|---|---|---|
| Americas | Canada | 161.69.9.0/24 | 443 | Access logs, reporting | ca.logapi.skyhigh.cloud |
| Americas | United States | 161.69.8.0/24 | 443 | Hybrid policy synchronization | policysync.skyhigh.cloud |
| Americas | United States | 161.69.8.0/24 | 443 | Access logs, reporting | us.logapi.skyhigh.cloud |
| Americas | United States (Las Vegas) | 161.69.8.0/24 |
443 | Fetching server certificates on the user interface | n/a |
| Asia/Pacific | Australia | 161.69.58.0/24 | 443 | Access logs, reporting | au.logapi.skyhigh.cloud |
| Asia/Pacific | India | 161.69.14.0/24 | 443 | Access logs, reporting | in.logapi.skyhigh.cloud |
| Asia/Pacific | Singapore | 161.69.13.0/24 | 443 | Access logs, reporting | sg.logapi.skyhigh.cloud |
| Europe | England | 161.69.11.0/24 | 443 | Access logs, reporting | gb.logapi.skyhigh.cloud |
| Europe | Germany | 161.69.12.0/24 | 443 | Access logs, reporting | de.logapi.skyhigh.cloud |
| Middle East | Saudi Arabia | 161.69.62.0/24 | 443 | Access logs, reporting | sa.logapi.skyhigh.cloud |
| Middle East | United Arab Emirates | 161.69.104.0/24 and 161.69.85.0/24 |
443 | Access logs, reporting | ae.logapi.skyhigh.cloud |

