mwginternal.com - Get Creative with your Rules
What is mwginternal.com, and why should I care?
mwginternal.com is a domain that was registered by McAfee (and will continue to be for the foreseeable future) for you to make use of when creating internal requests. McAfee holds this domain, and has a wildcard DNS entry, so any subdomain will resolve.
The host is: *.mwginternal.com
The underlying IP is: 78.46.136.174
This is useful because it will give you a definitive 'dummy URL' to use for any request referencing the Secure Web Gateway itself. For example, to easily collect troubleshooting info you could use 'tsinfo.mwginternal.com' and return a block page that contained useful information(client IP, authenticated username/groups, user-agent, etc).
The fact that this is a wildcard DNS is especially useful in transparent deployments (WCCP, Transparent Router/Bridge, etc). In these situations, the clients are not aware of the proxy, and will do a DNS request for the URL in question. Since *.mwginternal.com will always return the IP of 78.46.136.174, we can be sure that internal requests will always work as expected for both direct proxy and transparent deployments.
How should I use it?
As this is intended to be used as an internal-only domain, all actions referring to mwginternal.com should always result in a 'Block' action of some sort -- as there is no point in sending any traffic to the actual domain. As a general rule of thumb, for our internal server rules we'd want to use Criteria along the lines of:
URL.Host matches *.mwginternal.com OR
URL.Destination.IP equals 78.46.136.174
If you happen to forget to set a block action -- the web server will return a simple message of:
Use Case Examples
These are examples intended to give some high level ideas of what mwginternal.com can dofor you.
Troubleshooting Information
Perhaps the most common use I've seen for internal requests is the ability to pull up a page that will display all of the information we have on a test client. This can be very useful to troubleshooting authentication issues, policy mapping issues, and sometimes it's just an easy way to get your end-user to pull up their IP address.
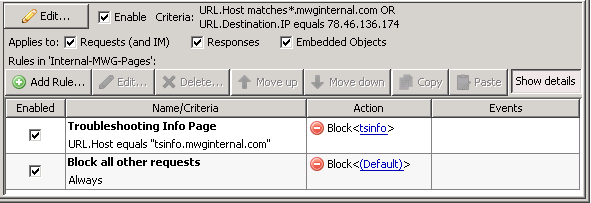
After creating this rule, I customized a new error template to include the information I was looking for:
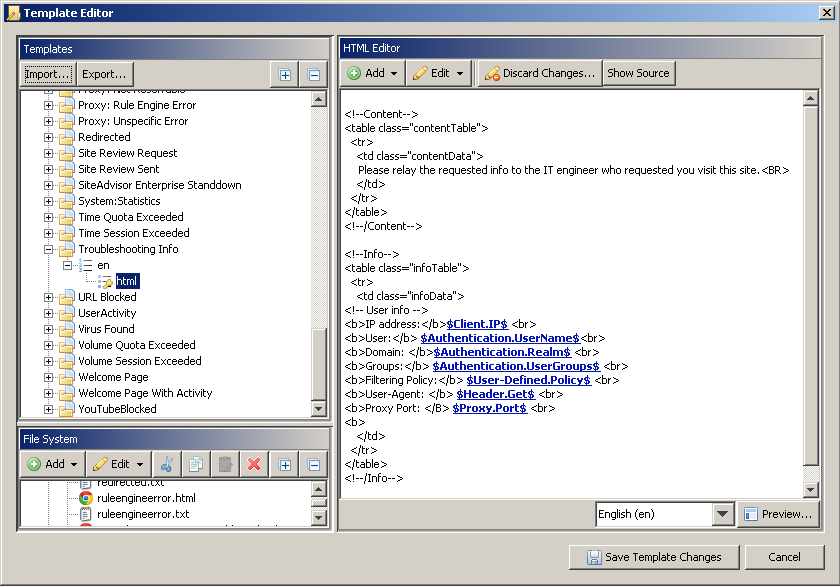
For example, to aid in troubleshooting an end-user's workstation that is going through the Secure Web Gateway - I can ask the end user to visit http://tsinfo.mwginternal.com. By doing so, they'll see the info displayed on the error template and can read back to me any of the values the Secure Web Gateway populated, as pictured below.
Authentication Server
If you are using the Time/IP or Cookie auth server - and would like to clean things up a bit, you can make use of a mwginternal domain to give you something a bit more obvious to look for within requests. Under the 'IP Authentication Server' information, you can replace the stock value, shown here:
http://$<propertyInstance useMostRecentConfiguration="false" propertyId="com.scur.engine.system.proxy.ip"/>$:$<propertyInstance useMostRecentConfiguration="false" propertyId="com.scur.engine.system.proxy.port"/>$
with the much more user-friendly value shown here:
http://authserver.mwginternal.com
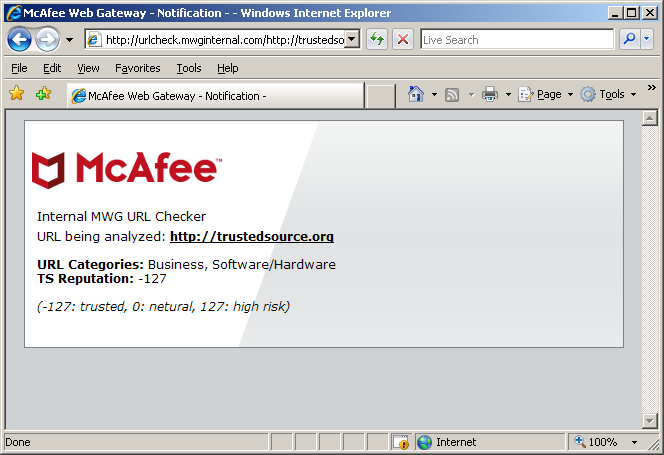
URL Checker
One useful thing that you can utilize the mwginternal domain for is doing quick URL checks against your local SWG. This can be especially useful if you are making wide use of extended lists to recategorize sites.
I've crafted the following rule that allows you to simply enter a website as a 'path' to a mwginternal subdomain.
The customized blockpage I created takes the 'URL.Path' value and uses it to performa check against 'URL.CategoriesForURL' and 'URL.ReputationForURL'. The check results are displayed on the blockpage (see below).
To use the checker, you can simply visit http://urlcheck.mwginternal.com/http...stedsource.org on a machine navigating through your SWG, and get some info on how your Secure Web Gateway categorizes the site.
Other Ideas
The sky is the limit. Some have configured internal 'site review' requests, so that if a user is blocked, they can send an e-mail to their local admin requesting access. Other people have created diagnostic rules to enable rule engine tracing. Any time you need to be referencing the Secure Web Gateway itself, or simply need a 'dummy' URL to trigger something, mwginternal.com is available and should be the domain of choice.

