Providing SSO services for SAML 2.0 cloud applications
Web Gateway supports cloud services and applications that use SAML 2.0 authentication to log on users by providing cloud connector templates.
A cloud connector is the configuration that allows Web Gateway to connect to and provide identity and SSO services for an application or service in the cloud. Web Gateway provides connector templates for many individual cloud services and applications. Web Gateway also provides a generic SAML2 connector template. The generic template can be configured for any cloud service or application that uses SAML 2.0, but is not included in the SSO Catalog.
NOTE: Configuring single sign-on for a SAML 2.0 cloud application requires configuration in your SAML 2.0 application administrator account and in the Web Gateway user interface.
How SAML single sign-on is initiated
The SAML SSO process is initiated by the Identity Provider (IdP) or the Service Provider (SP).
The Identity Provider is the service that authenticates the user. The Service Provider is the SAML cloud service or application that the user wants to access. In the following examples of SAML single sign-on, Web Gateway performs the Identity Provider role.
The SSO process begins when the user requests access to a SAML application in the cloud. Web Gateway authenticates the user, then redirects the authentication result to the SAML application through the user's browser. The redirected messages are automatic and take place quickly, so that the user is not aware of the authentication process running in the background.
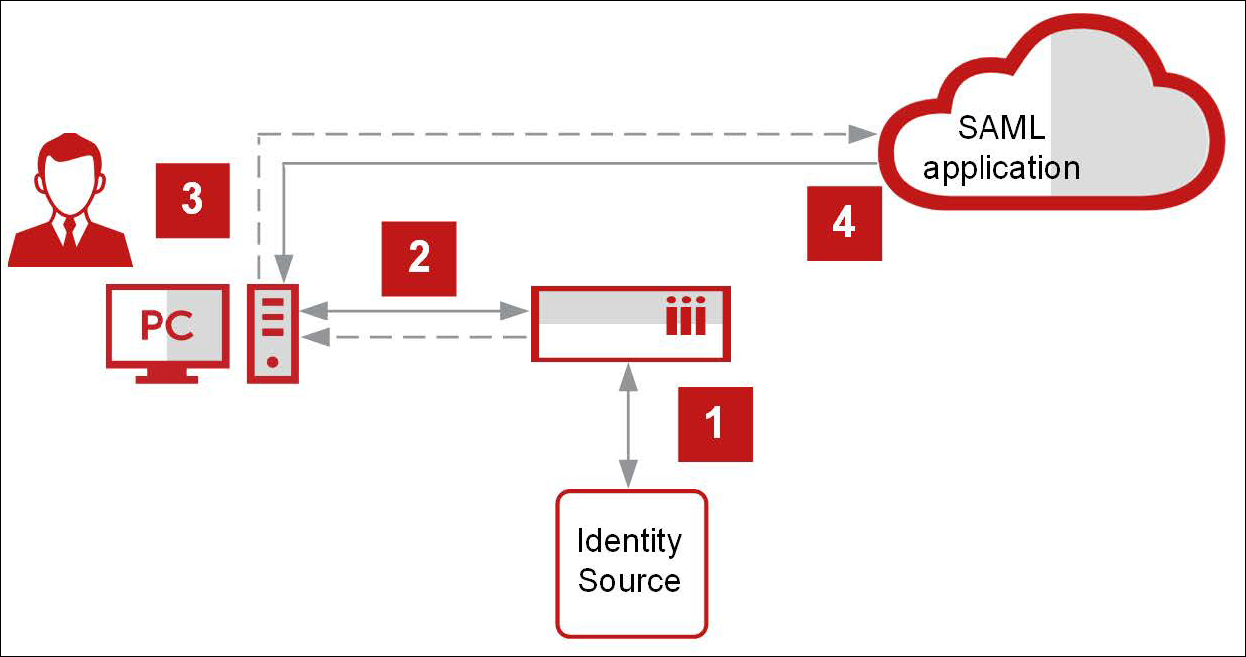
IdP-initiated SAML single sign-on
Web Gateway initiates the SSO process, which consists of the following overall steps:
- Web Gateway authenticates the user.
- Web Gateway presents the user with a launchpad that includes icons for all SAML applications the user is allowed to access. The user requests access to a SAML application (the Service Provider) through Web Gateway (the Identity Provider) by selecting an icon on the launchpad.
- Web Gateway redirects the authentication result to the SAML application through the user’s browser.
- The SAML application grants access to the user.
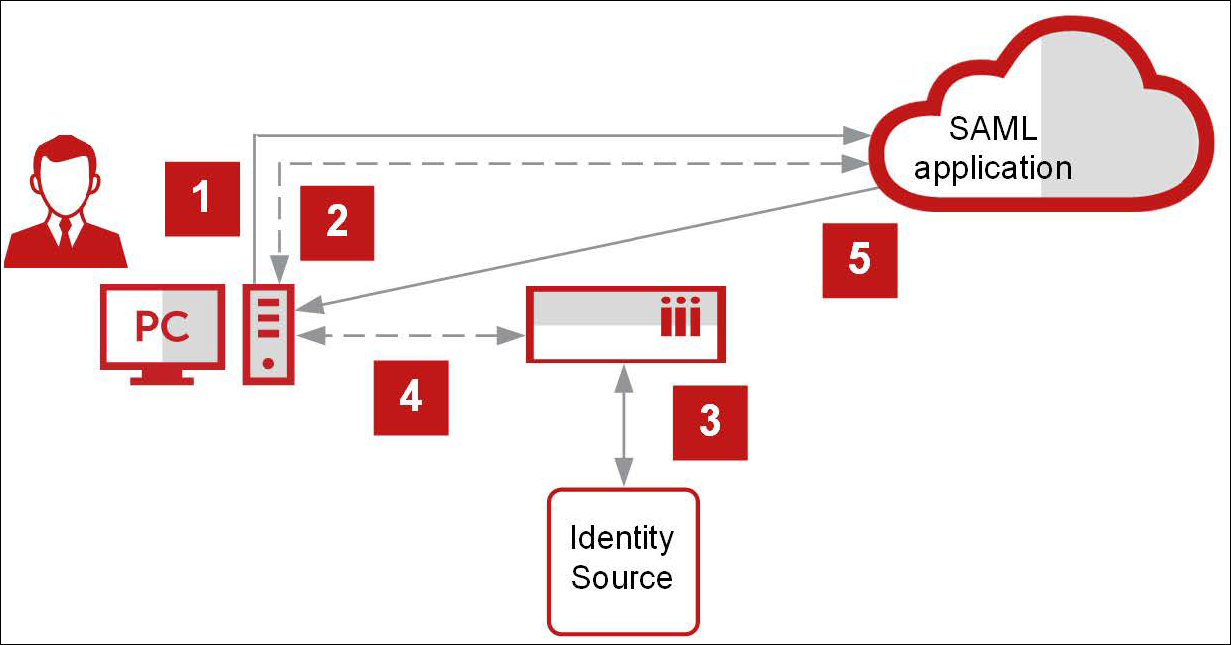
SP-initiated SAML single sign-on
The SAML application in the cloud initiates the SSO process, which consists of the following overall steps:
- The user requests access to a SAML application (the Service Provider) directly.
- The SAML application redirects the user’s request to Web Gateway (the Identity Provider) through the user’s browser.
- Web Gateway authenticates the user.
- Web Gateway redirects the authentication result to the SAML application through the user’s browser.
- The SAML application grants access to the user.
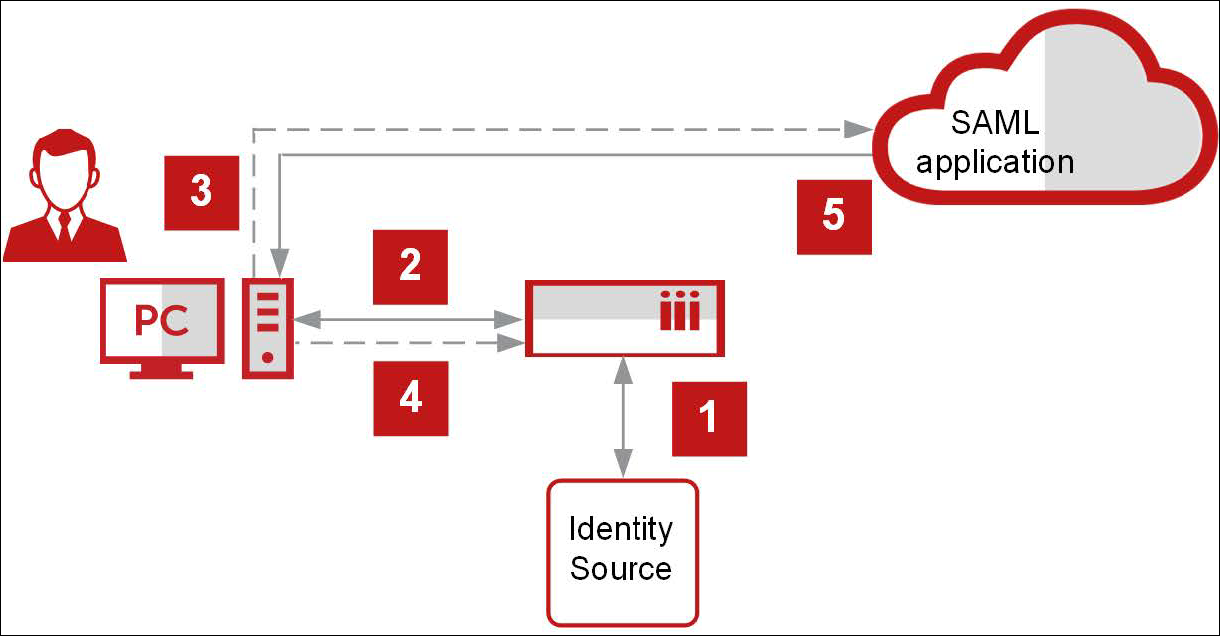
Pure SP-initiated SAML single sign-on
Not all SAML applications support IdP-initiated and SP-initiated single sign-on. Some SAML applications support only one. SAML applications that support only SP-initiated single sign-on present a special use case called pure SP-initiated single sign-on.
- Web Gateway authenticates the user.
- Web Gateway presents the user with a launchpad that includes icons for all SAML applications the user is allowed to access. The user requests access to a SAML application (the Service Provider) through Web Gateway (the Identity Provider) by selecting an icon on the launchpad.
- Because the SAML application only supports SP-initiated single sign-on, Web Gateway redirects the user's request to the application through the user's browser. Because the user is not authenticated, the SAML application redirects the user to Web Gateway with an authentication request.
- Web Gateway redirects the authentication result to the SAML application through the user’s browser.
- The SAML application grants access to the user.
Certificate management for SAML single sign-on
SAML single sign-on requires an X.509 certificate and private key.
Together, the X.509 certificate and private key are known as the X.509 certificate key pair. The X.509 certificate contains the public key that makes up the key pair and a signature. The certificate can be self-signed or signed by a certificate authority.
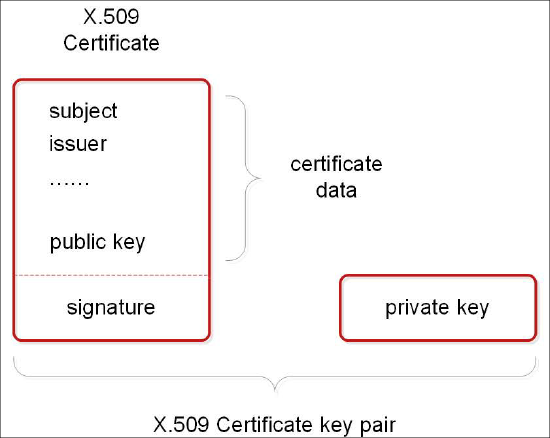
The private key is used for signing outgoing SAML assertions and requests, and the X.509 certificate is used for verifying incoming signatures. The SSO party signing SAML assertions or requests with the private key provides the X.509 certificate to the SSO party verifying the signatures.
SAML services and applications have different certificate requirements. The following scenarios are common.
| SSO process | Certificate management steps | SSO steps |
|---|---|---|
|
IdP-initiated and |
|
|
|
SP-initiated SSO |
|
|
Configure a SAML2 cloud connector
Configure a connector to a SAML 2.0 service or application using a template.
Task
- Select Policy | Lists.
- In the Lists tree, expand System Lists | SSO Catalog, then click Custom connectors.
- Click the Add icon.
The Add Connector dialog box opens. - Provide values for the fields and settings common to all connectors.
- From the Template drop-down list, select the template corresponding to the SAML 2.0 service.
- Provide values for the SAML settings.
- Click OK.
The newly configured SAML2 connector is added to the SSO Catalog | Custom connectors list.
Configure a generic SAML2 cloud connector
Configure a generic SAML2 cloud connector when you want to connect to a SAML 2.0 service that Web Gateway does not support with an individual connector template.
Task
- Select Policy | Lists.
- In the Lists tree, expand System Lists | SSO Catalog, then click Custom connectors.
- Click the Add icon.
The Add Connector dialog box opens. - Provide values for the fields and settings common to all connectors.
- From the Template drop-down list, select Generic SAML2 Connector.
- Provide values for the generic SAML2 settings.
- Click OK.
The newly configured SAML2 connector is added to the SSO Catalog | Custom connectors list.
Configuring external data sources for SAML single sign-on
While credentials for single sign-on to HTTP services are stored in the credential store that comes integrated with Web Gateway, SAML credentials come from external data sources, such as one or more LDAP servers, a database, or a web service. Several external data sources are configured using the external lists feature.
Identity information is fetched from external data sources as user attribute name-value pairs. The names must match the attribute names configured when the cloud connector was created.

