Nodes in a Cluster
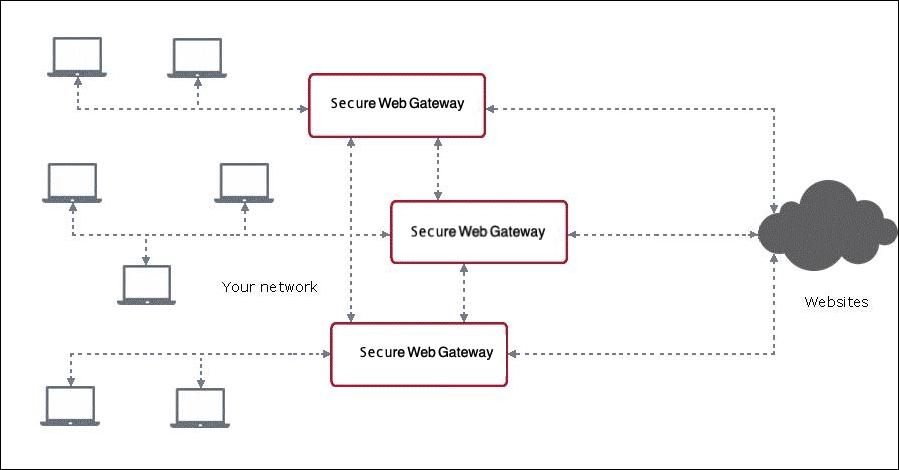
In a cluster, multiple appliances run as nodes and can be administered from any of these nodes. They are connected to each other and to other systems within your network as follows:
-
Each node is connected to the client systems of your network that direct their web traffic to it for filtering purposes.
-
Nodes are assigned to node groups.
-
Node groups allow common administration activities for the group members, for example, transferring data for updates from one node to another node or several other nodes.
When configuring appliances as nodes, make sure that they can "see" (connect to) each other. The default port on an appliance that listens to messages from other appliances is 12346.
Using the ping command is a method to verify that appliances can connect. This method is, however, not applicable to all networks.
-
-
There are different types of node groups that allow different kinds of data transfer between the group members.
The following diagram shows how several appliances run as nodes in a cluster.
Types of Node Groups
When the appliances in a cluster are configured as nodes, they can be assigned to the following types of node groups:
- Runtime group — A node that is a member of a runtime group can share runtime data with all other nodes in the group.
Runtime data is data that is created at runtime on an appliance. For example, the amount of time that is left for a user at a given point in time when a quota restriction has been imposed on web usage is runtime data.
A node can only be a member of one particular runtime group. -
Update group — A node that is a member of an update group can share updates with all other nodes in the group.
A node can only be a member of one particular update group. -
Network group — A node that is a member of a network group can immediately connect to all other node in the group.
A node can be a member of different network groups at the same time.
When a node is a member of different node groups, for example, of groups A and B, it is possible to transfer data through that node from other nodes in group A that are not members of group B to nodes in group B that are not members of group A.
Secure Cluster Communication
Communication between the nodes in a Central Management cluster is usually SSL-secured. Certificates for Certificate Authorities (CAs) with Private Keys are implemented to enable this kind of communication.
When setting up a cluster you can begin by generating the required security items on one appliance and import them to every other appliance that you include in the cluster later on.
Including Appliances as Nodes in a Cluster
Once you have begun to set up a Central Management cluster by using a particular appliance as your first node, you can include more appliances.
To include an appliance, you can work on the user interface of another appliance that is already a cluster node or on the user interface of the appliance you want to include.
The following terms are used for the two methods.
-
Add — Adding an appliance to a cluster means that you work on the user interface of another appliance that is already a cluster node.
- Join — Letting an appliance join a cluster means that you work on its own user interface.
Both methods require that the necessary items for performing secure cluster communication are already implemented on the appliance that is to be included in the cluster.
Web Policy in a Cluster
The web policy that is implemented in a Central Management cluster to ensure web security is always the same for all cluster nodes.
When you set up a cluster, you begin with the web security policy that is implemented on the appliance that is your first node in the cluster. Any other appliance that you include as a node adopts the policy that already exists in the cluster.
If you make changes to this policy on one node, the changes are distributed to all other nodes.
In contrast to the common web security policy on the nodes in a cluster, the system settings for an individual appliance are retained when this appliance is included as a node.
If you change the system settings for an individual appliance, the other appliances in the cluster are not affected.
Scheduled Jobs
You can schedule jobs on an appliance that is a node in a Central Management cluster, such as creating a configuration backup or downloading files, for execution at a particular time and date or in regular intervals.
You can also configure the schedule in the interface of the node where you are currently working and execute the job on another node in the cluster.

