About Skyhigh CASB for Azure Information Protection
Azure Information Protection (AIP) allows organizations to classify and optionally protect sensitive documents using default and custom labels. You can learn more about AIP and the way labels work in Azure Information Protection. Once you configure AIP, you can use AIP labels in Skyhigh CASB DLP policies for supported CSPs.
For more information on how Skyhigh CASB integrates with API and proxy, see Using AIP Labels in DLP Policies.
| To enable Azure Information Protection, contact Support. |
Policy Validation Logic
AIP is not supported for all CSPs. If AIP labels are used in a policy and the policy is attached to a service instance that doesn't support AIP, then the policy rule evaluation or policy action execution is skipped for that service instance.
For supported CSPs, it is important to choose labels from only those AIP instances that are mapped to a service instance.
If a policy uses labels from an AIP instance that is NOT mapped to the service instances selected in the policy, an error or warning is displayed. This is a critical error that must be resolved. If you select the Save Anyway option and ignore this error, it could result in documents in one department or organization being encrypted with AIP labels from another organization.
Supported Cloud Services
The following cloud services are supported in API and/or Proxy mode.
KNOWN ISSUES:
- When you upload a file with an AIP label, it is not applied to the following CSPs via Reverse Proxy*.
- **When you upload a file with an AIP label for Salesforce, it is applied to the following object types: Attachment and Document.
- **When you upload a file with an AIP label for Salesforce, it is not applied to the following object types: ContentVersion and Chatter File Upload. It is due to Salesforce API limitations and unable to Quarantine these objects.
| Cloud Service | Mode |
|---|---|
| OneDrive | API, Reverse Proxy* |
| SharePoint | API, Reverse Proxy* |
| Microsoft Teams | API, Reverse Proxy* |
| G Suite | API, Reverse Proxy* |
| Box | API, Reverse Proxy* |
| Salesforce | API**, Reverse Proxy |
| Workday | Reverse Proxy |
| ServiceNow | Reverse Proxy |
| SuccessFactors | Reverse Proxy |
How It Works
Scanning protected content
Skyhigh CASB has the ability to apply DLP policies for protected and encrypted documents. If Skyhigh CASB is configured to apply DLP policy and encounters a AIP-protected document, the engine will request decryption from the AIP SDK with the configured permissions.
The permissions are granted by default when setting up the AIP connection using "admin consent" (see Configure Azure Information Protection in Skyhigh CASB) and can be given selectively when using a custom oAuth app (see Custom oAuth Application for Office 365 and Azure API Integration)
This feature allows scanning plain text data of AIP-protected and encrypted documents. Please take care when configuring DLP policy that applies AIP labels based on content, as this can also be used to change the existing AIP label and can be used to apply both labels with protection/encryption enabled and labels with protection/encryption disabled..
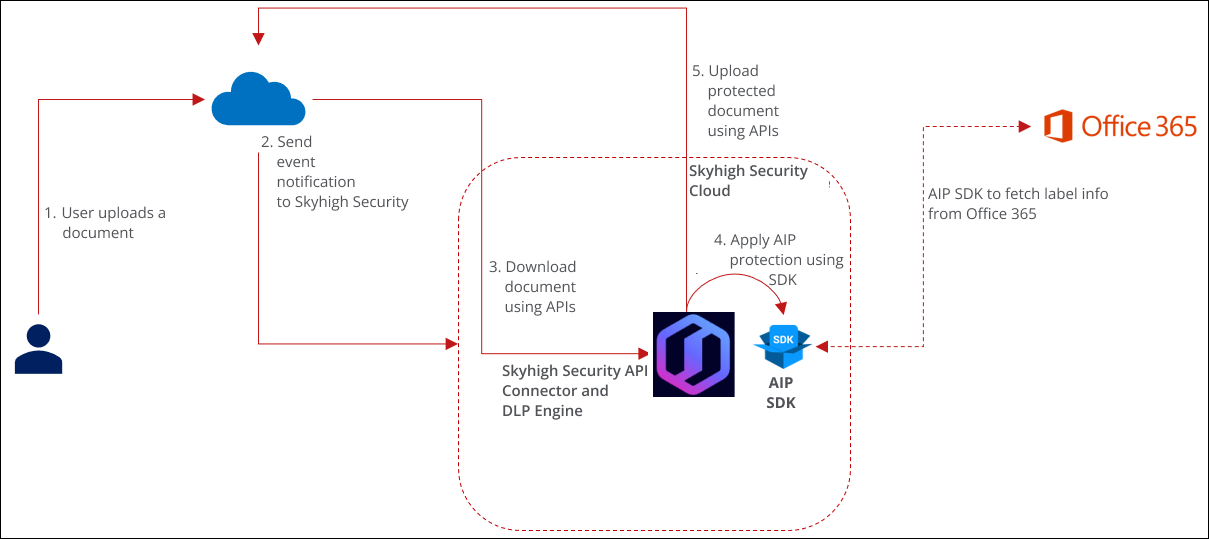
API Mode
- The user uploads a document to the cloud service.
- Skyhigh Security receives an event notification from the cloud service (through APIs).
- Skyhigh Security downloads the document contents, scans the content to identify sensitive data, and applies the classification label using Microsoft's SDK.
- A label is applied to a document in the Skyhigh Security cloud. If a label has the Encryption enabled, as well as applying the label to the document metadata, the SDK will also encrypt the document.
- The document with the label applied is now uploaded back to the application by Skyhigh Security.
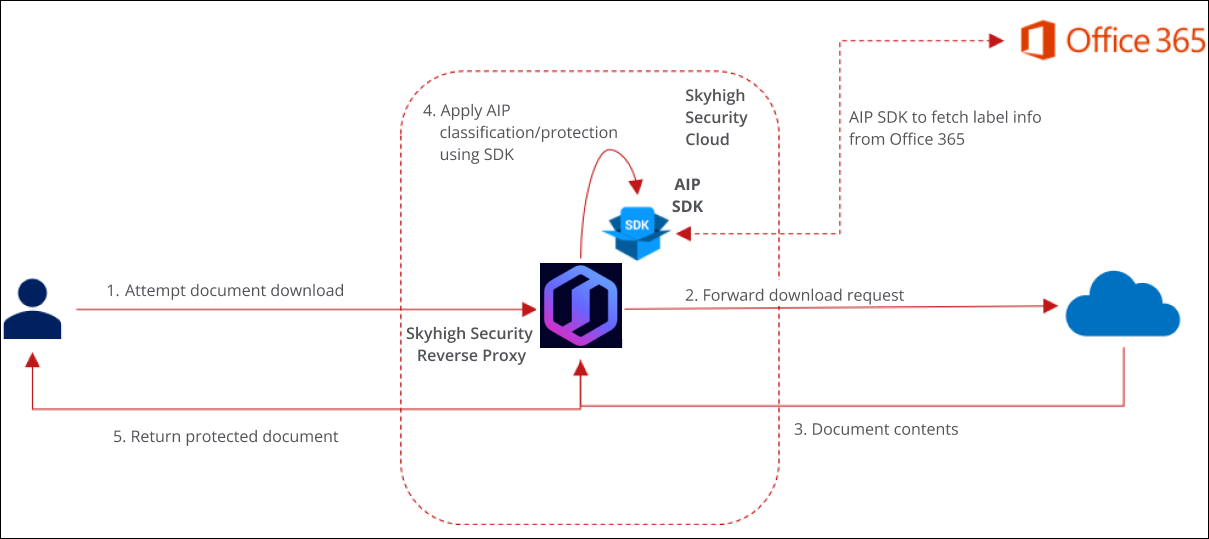
Reverse Proxy Mode
- The user attempts an upload or download activity.
- Forward download request.
- Document contents.
- Skyhigh CASB inspects document contents inline and applies the AIP classification.
- The downloaded or uploaded document is protected by AIP.