Configure an IdP in ServiceNow
Use the following steps to configure identity providers such as ADFS and Okta in ServiceNow.
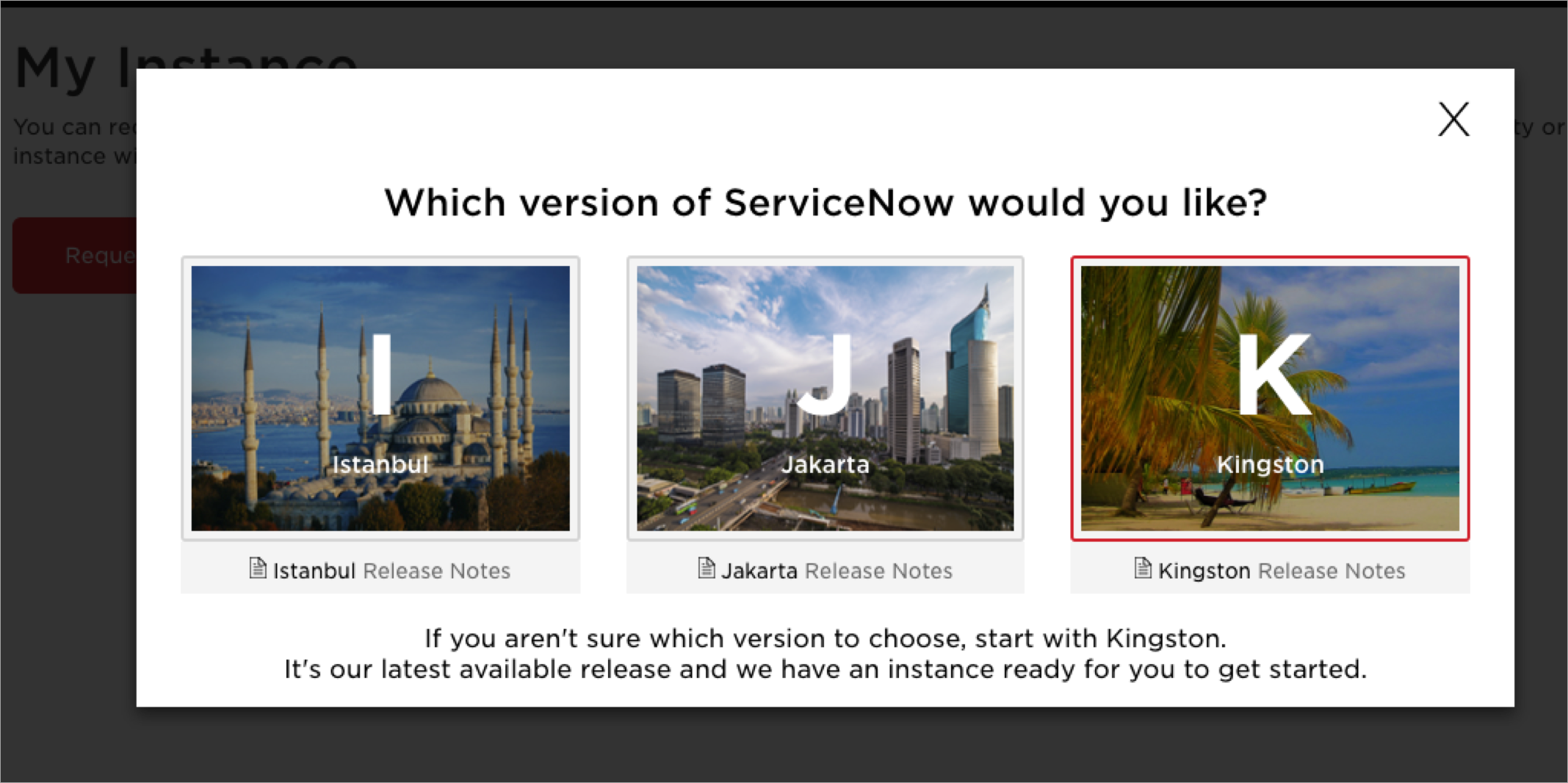
NOTE: This topic is covered for the Kingston release. You might see some changes in the later releases of ServiceNow.
Step 1: Create a ServiceNow Instance
Before you create a ServiceNow instance, register and create a ServiceNow Developer account using the link https://developer.servicenow.com/. Once the account is created, perform the following actions:
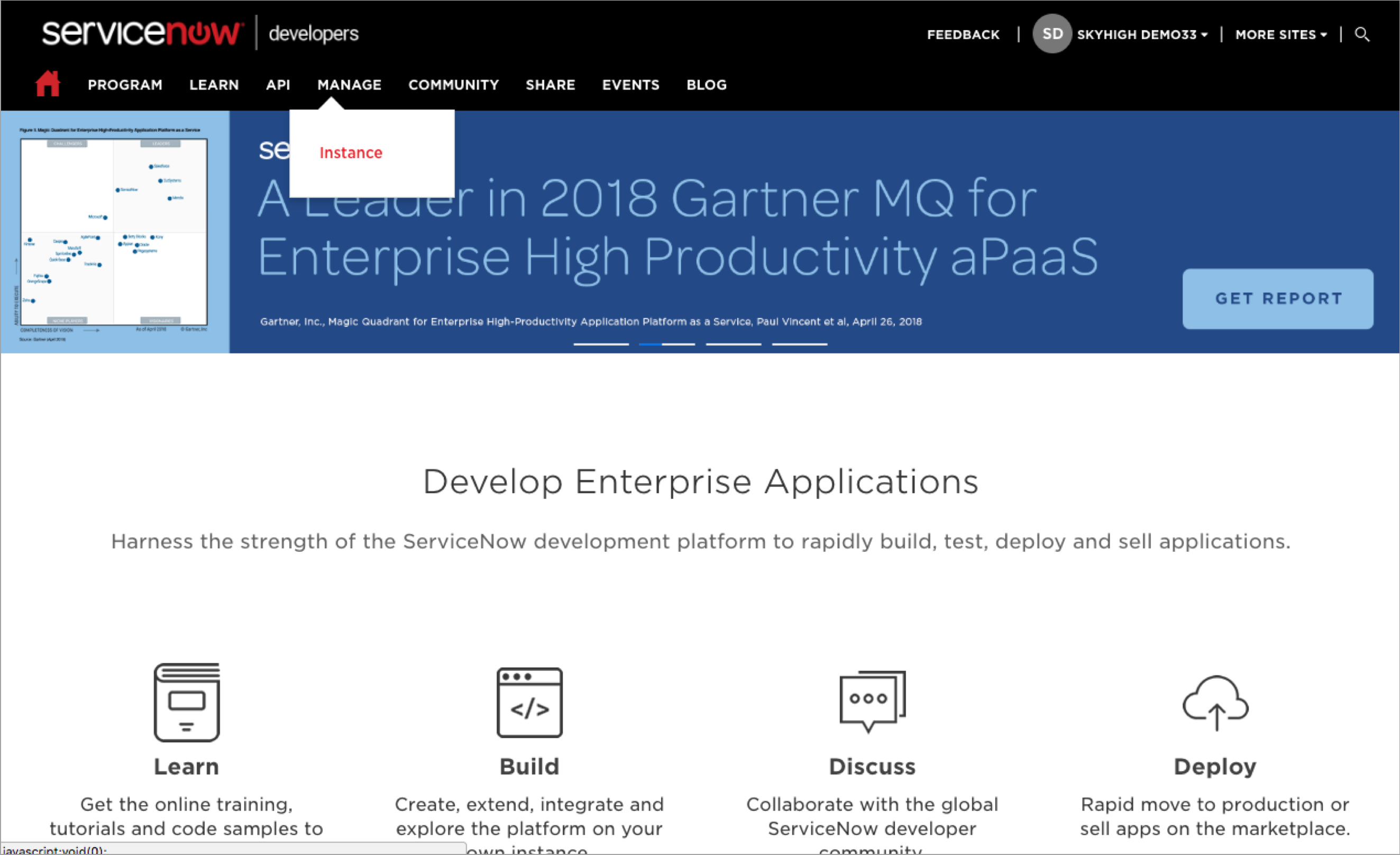
- Log in to the ServiceNow Developer account and go to Manage > Instance.
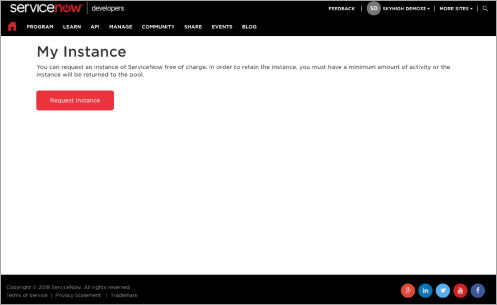
- Click Request Instance.
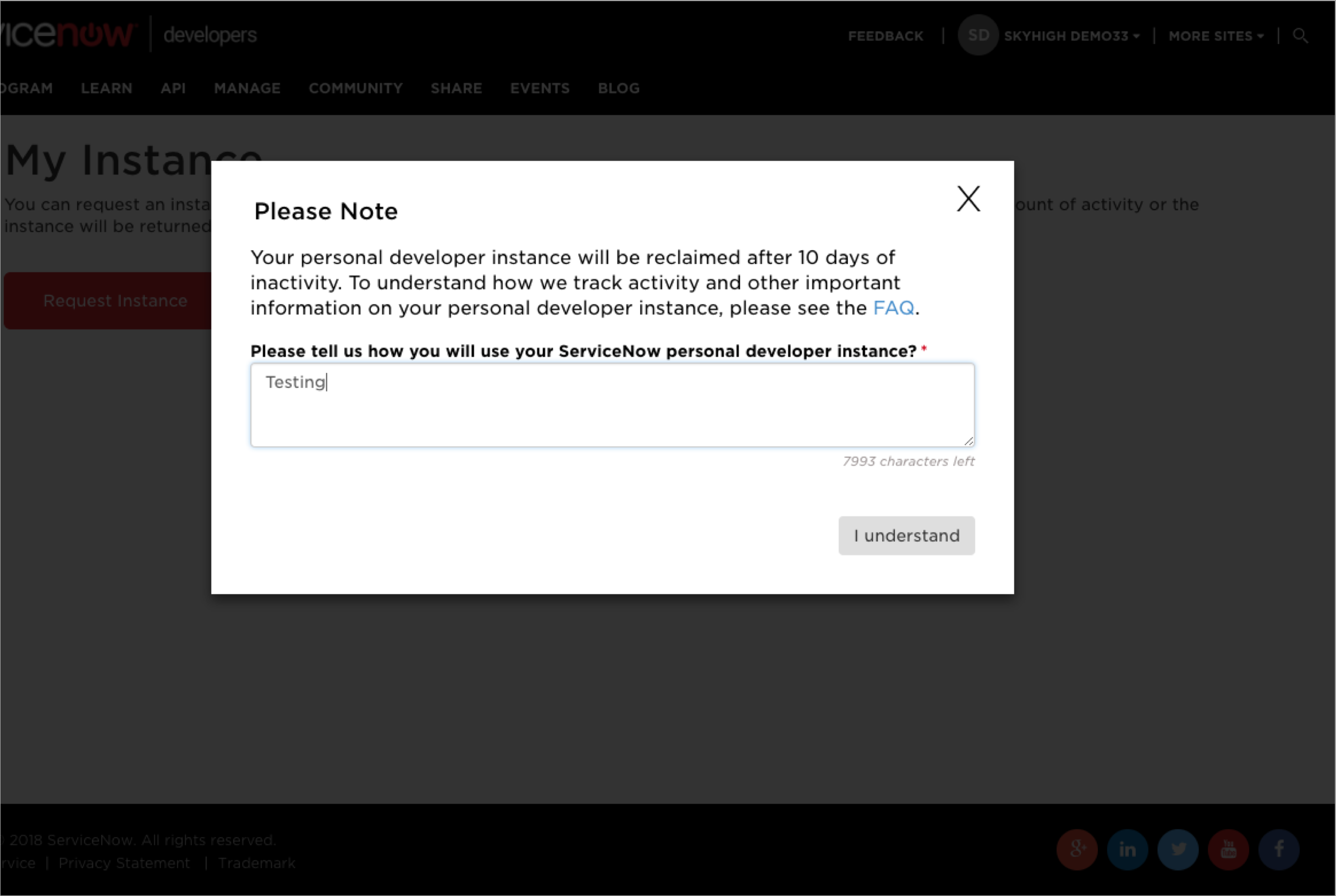
- Enter the reason for using the ServiceNow personal developer instance and click I understand.
- Click the ServiceNow version as Kingston.
- Your ServiceNow instance is created. Make sure to take a note of the ServiceNow URL and it is used to Configure the ServiceNow via Skyhigh CASB Proxy.
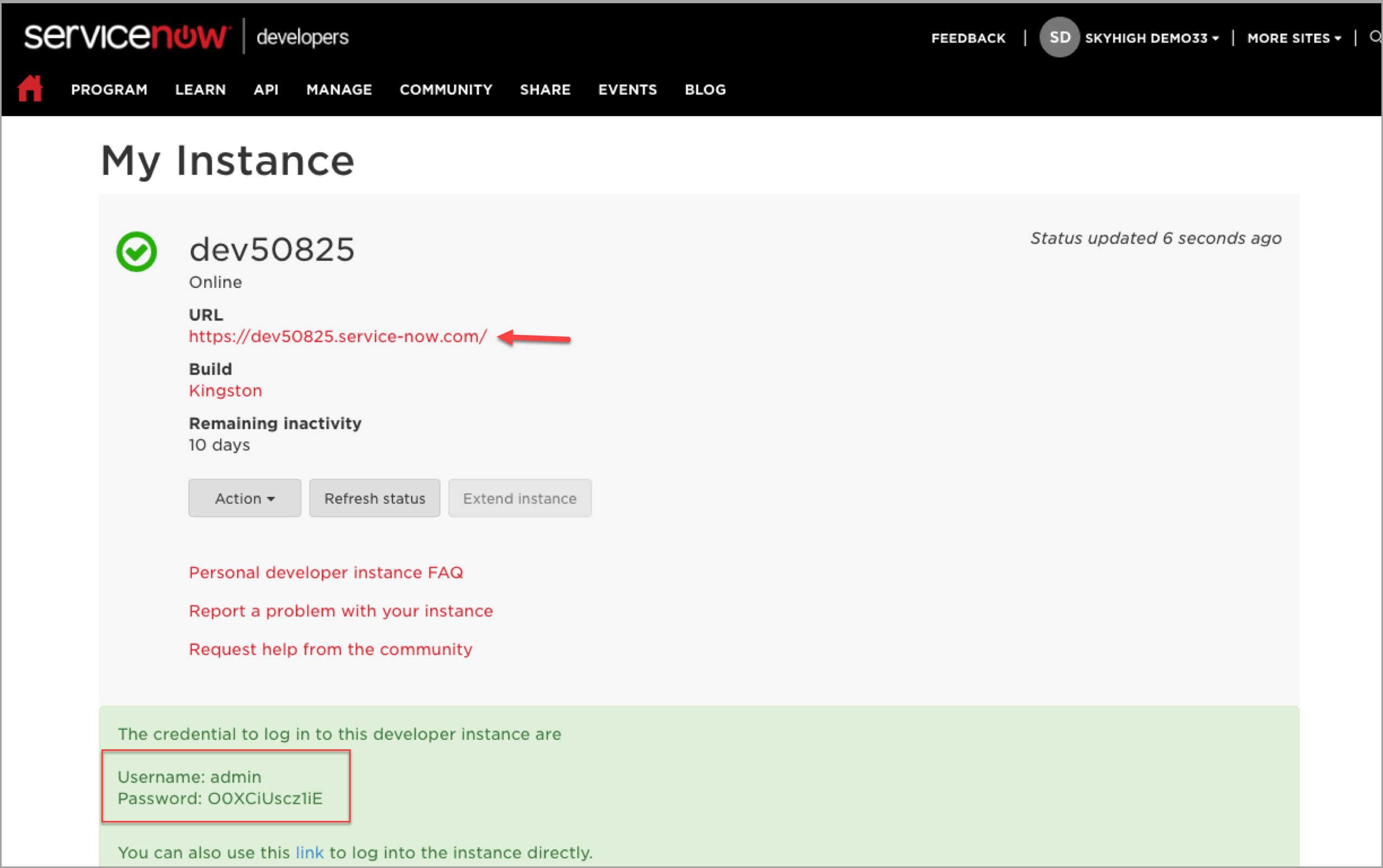
NOTE: When you first log in to your ServiceNow developer instance, you are directed to change the admin password, so take note of the password provided above. Then change the admin password before continuing.
Step 2: Configure ServiceNow via Skyhigh CASB Proxy
NOTES:
- You need a configured ServiceNow proxy to support Skyhigh CASB Gateway. If you do not have configured proxy, a contact Skyhigh Security Support to allocate your IP address with your tenant.
- You have a configured ServiceNow proxy but you are using a different ServiceNow instance, then unmanage this service and manage again using the new ServiceNow URL.
- The ACS can be modified to use the manage device check. So it is not necessary to set up SAML proxy for ServiceNow.
To configure ServiceNow instance via Skyhigh CASB proxy:
- Login to Skyhigh CASB with your tenant.
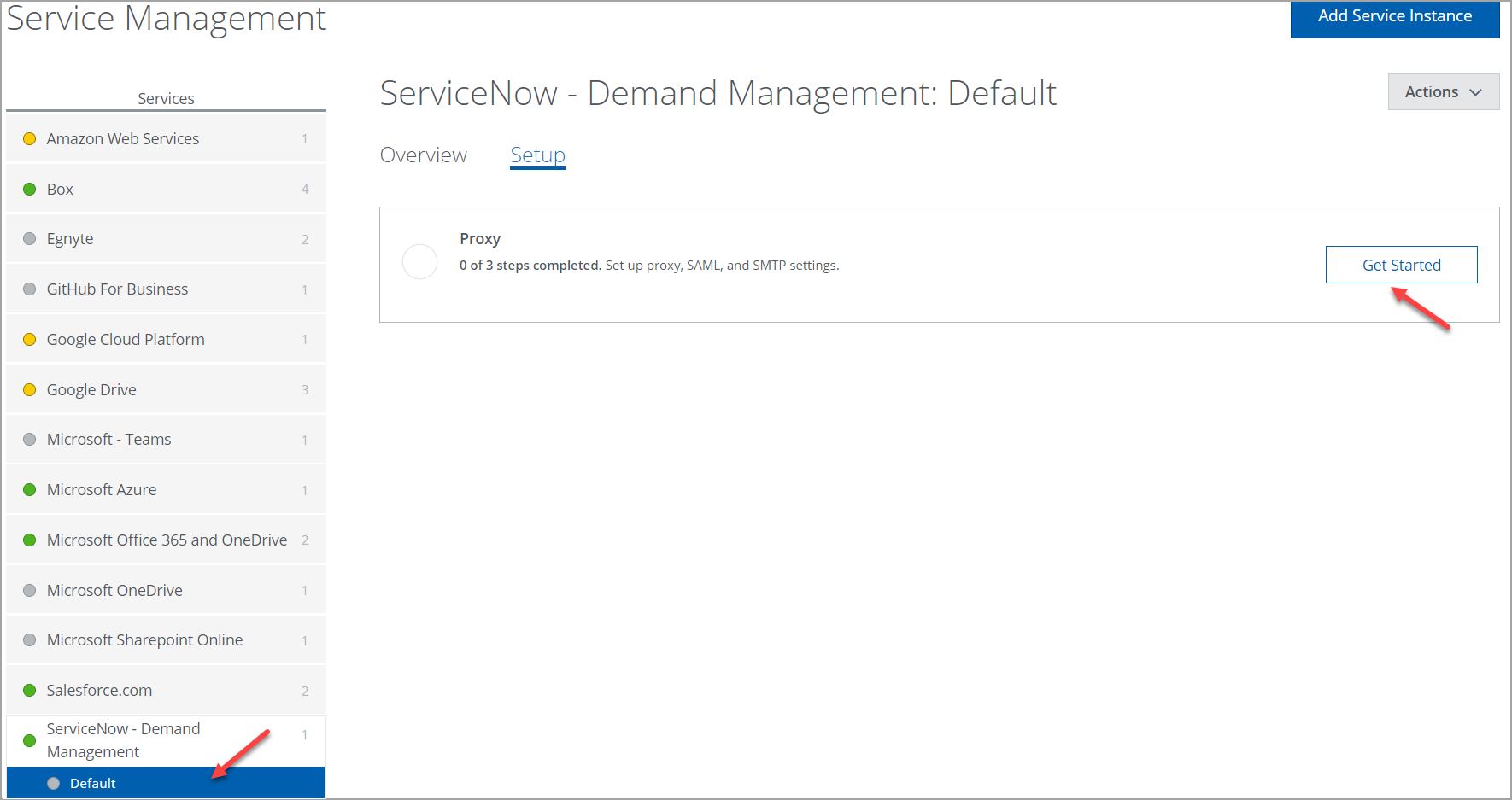
- Go to Settings > Service Management.
- Under the Services list, click ServiceNow and select your instance.
- Click the Setup tab, and under Proxy, click Get Started.
- Under Configure proxy, click Configure.
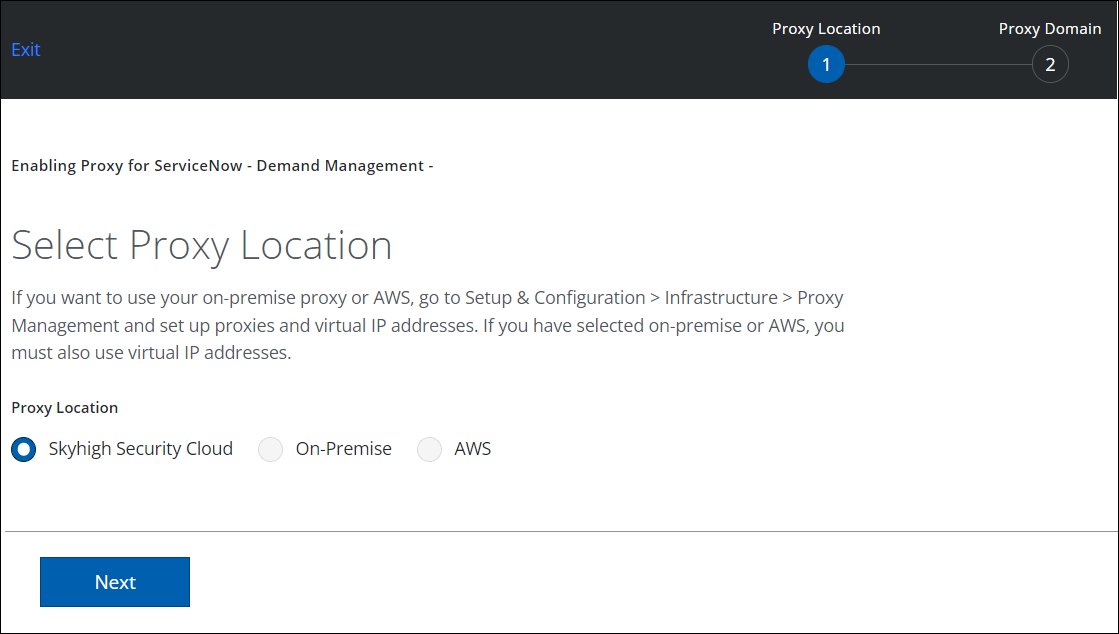
- For Select Proxy Location, select Skyhigh CASB. Click Next.
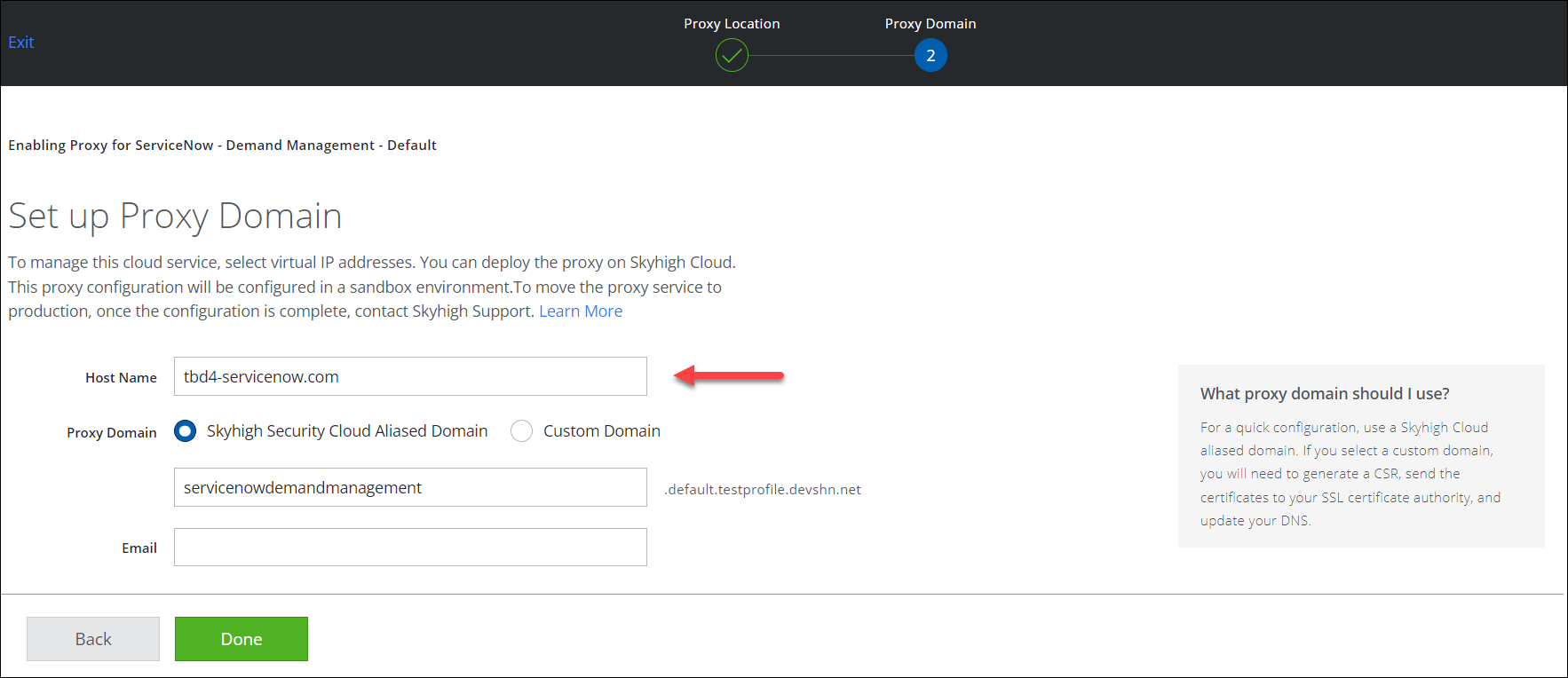
- Enter the ServiceNow URL received from Step 1 in the Host Name and click Done.
- Once the proxy is configured, you are redirected to the Setup page. Under Configure proxy, click Show Details and copy the Proxy URL.
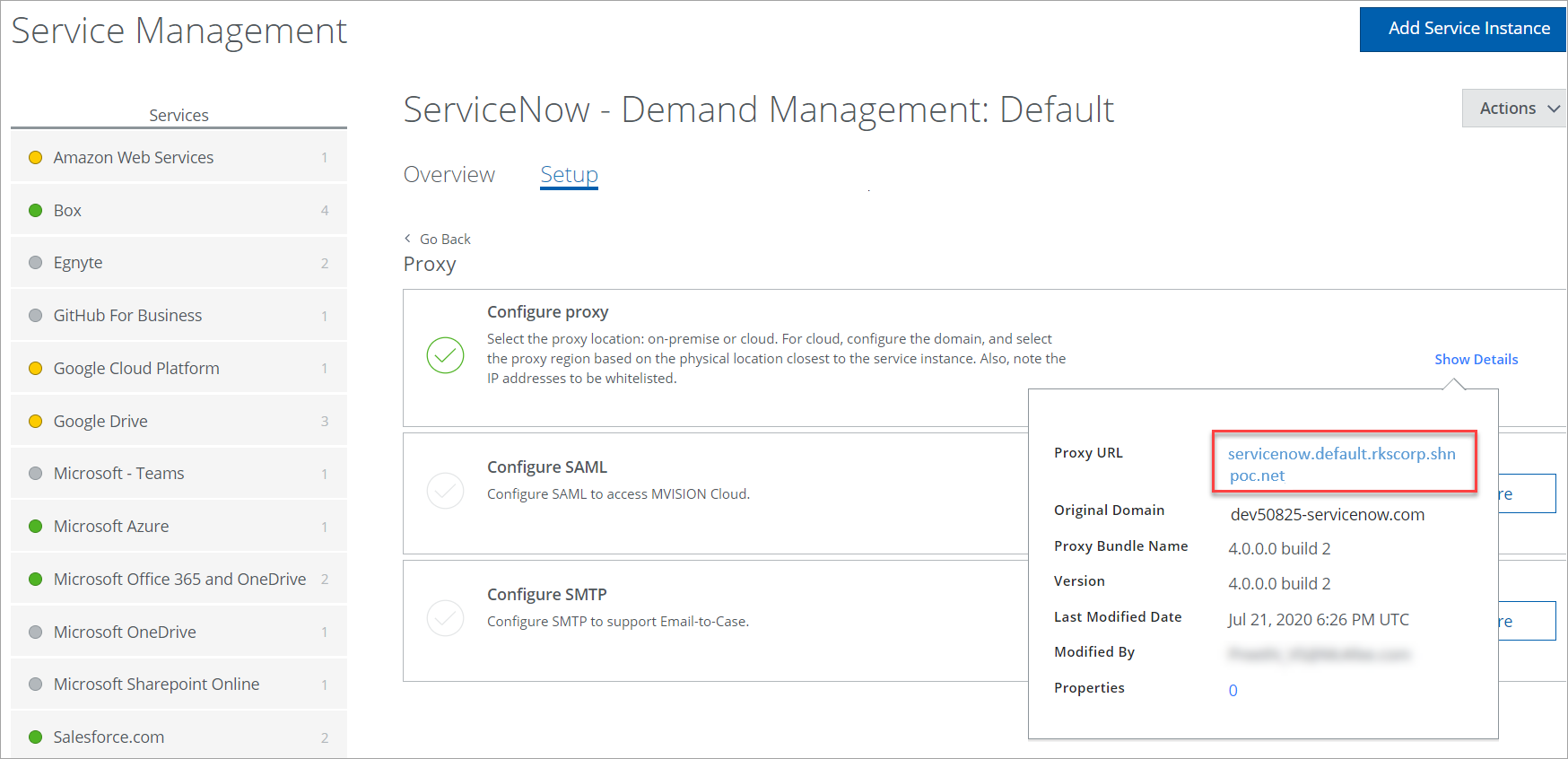
Click the Proxy URL link to open in the new browser window or paste the Proxy URL in the new browser window. If you can access the ServiceNow Proxy URL through Skyhigh CASB, you have successfully configured ServiceNow via Skyhigh CASB Proxy.
NOTE: Make sure to take a note of the Proxy URL (including the prefix www) to complete the IdP integration with ADFS. For example, www.servicenow.default.rkscorp.shnpoc.net.
Step 3: Activate and Configure SAML for ServiceNow
SAML activates through the Integration - Multiple Provider Single Sign-On Installer plug-in.
To enable the Multiple Provider Single Sign-On in ServiceNow:
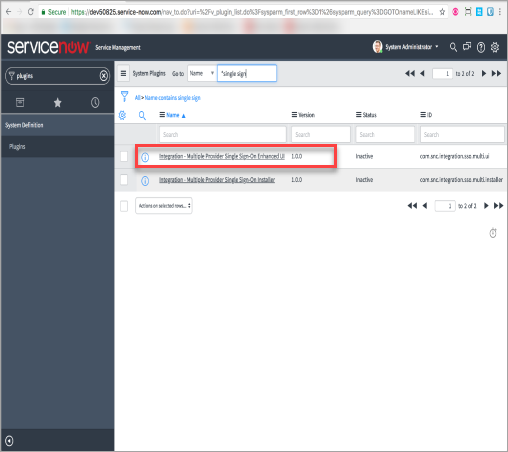
- Open the ServiceNow URL in the direct browser.
- Go to Plugins and search for single sign.
- Click the Integration - Multiple Provider Single Sign-On Installer link.
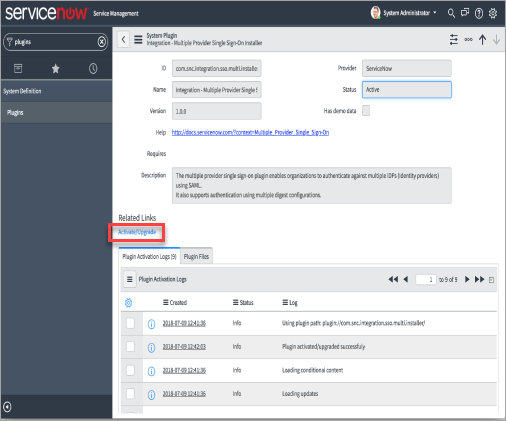
- Click Activate / Upgrade.
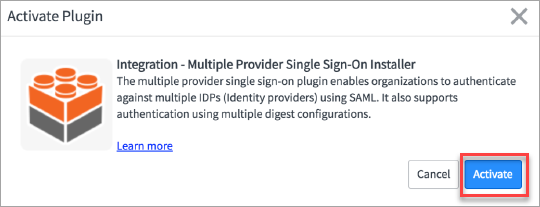
- You are redirected to Activate Plugin dialog. Click Activate.
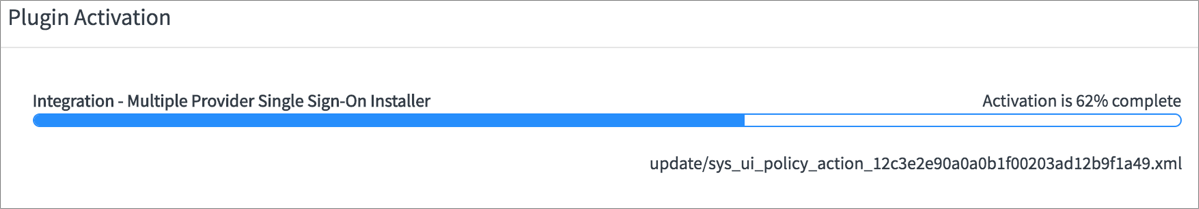
- Now, you can see the progress bar in the Plugin Activation window.
- On the successful completion of Plugin Activation, click Close & Reload Form.
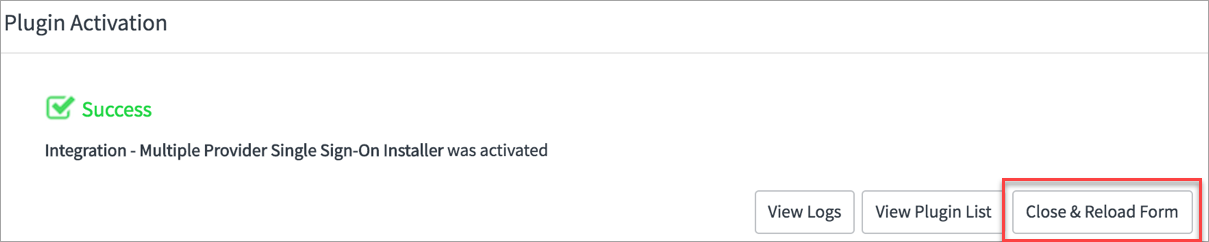
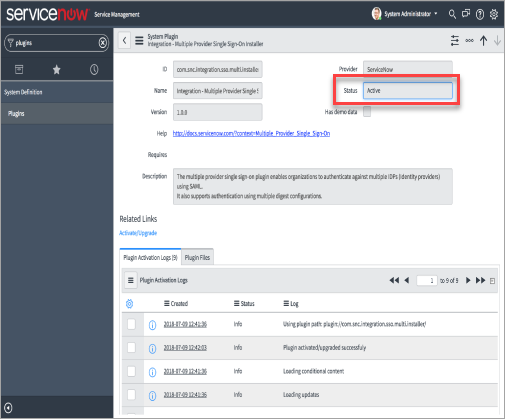
- You can see the status as Active in the reloaded form.
Step 4: Configure System Property in ServiceNow
Skyhigh Security Skyhigh CASB supports IdP configuration in ServiceNow only when the following configurations are met.
Before you configure IdP in ServiceNow, make sure to configure the system property in ServiceNow:
- In the Filter navigator, enter sys_properties.do and click enter.
- Create a System Property and configure the following parameters:
- Name. Enter the name as glide.authenticate.multisso.test.connection.mandatory.
- Type. Select the type as true|false from the menu.
- Value. Set the value as false.
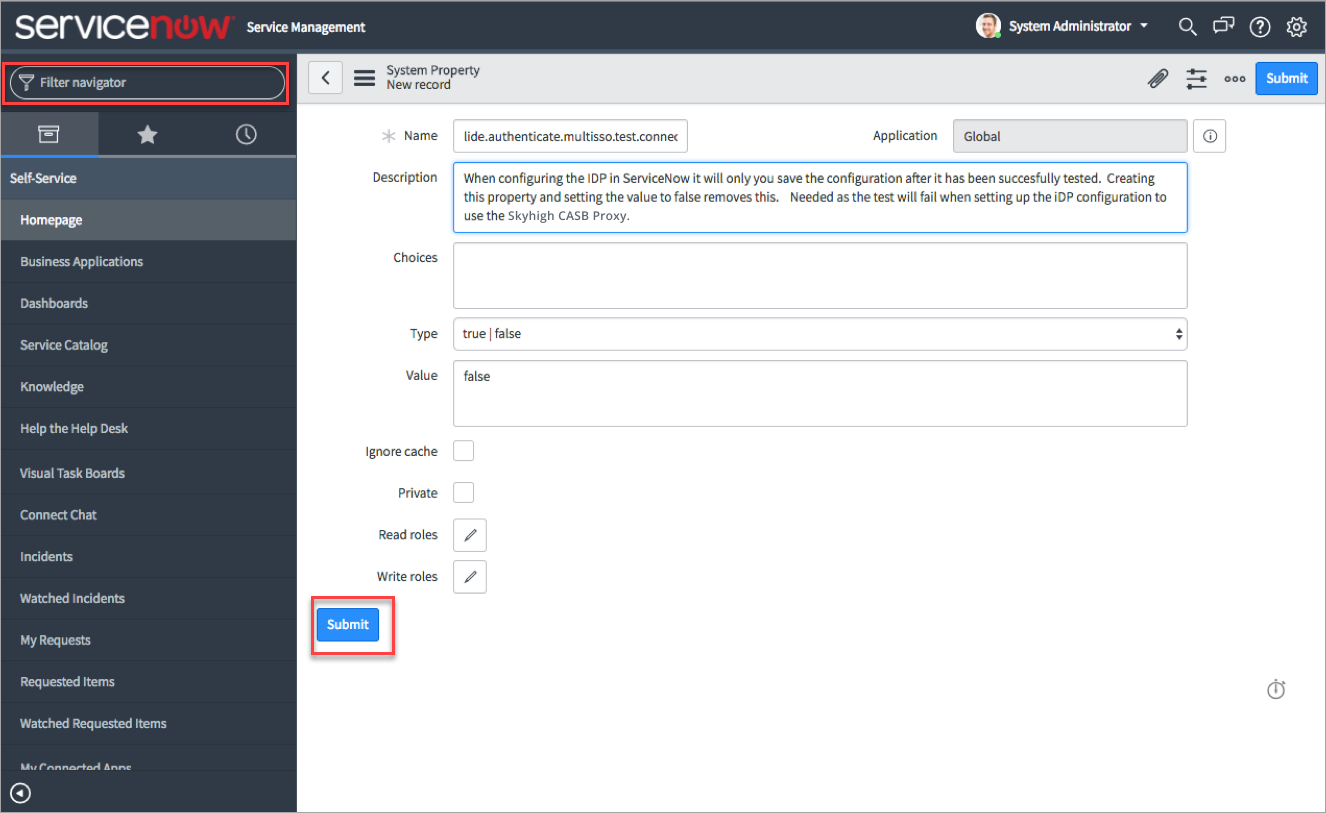
- Click Submit.
Step 5: Modify the SAML Script in ServiceNow
To support the SP initiated login for ServiceNow, modify the SAML Script file.
- Go to Multi Provider SSO and click Single Sign-On Scripts.
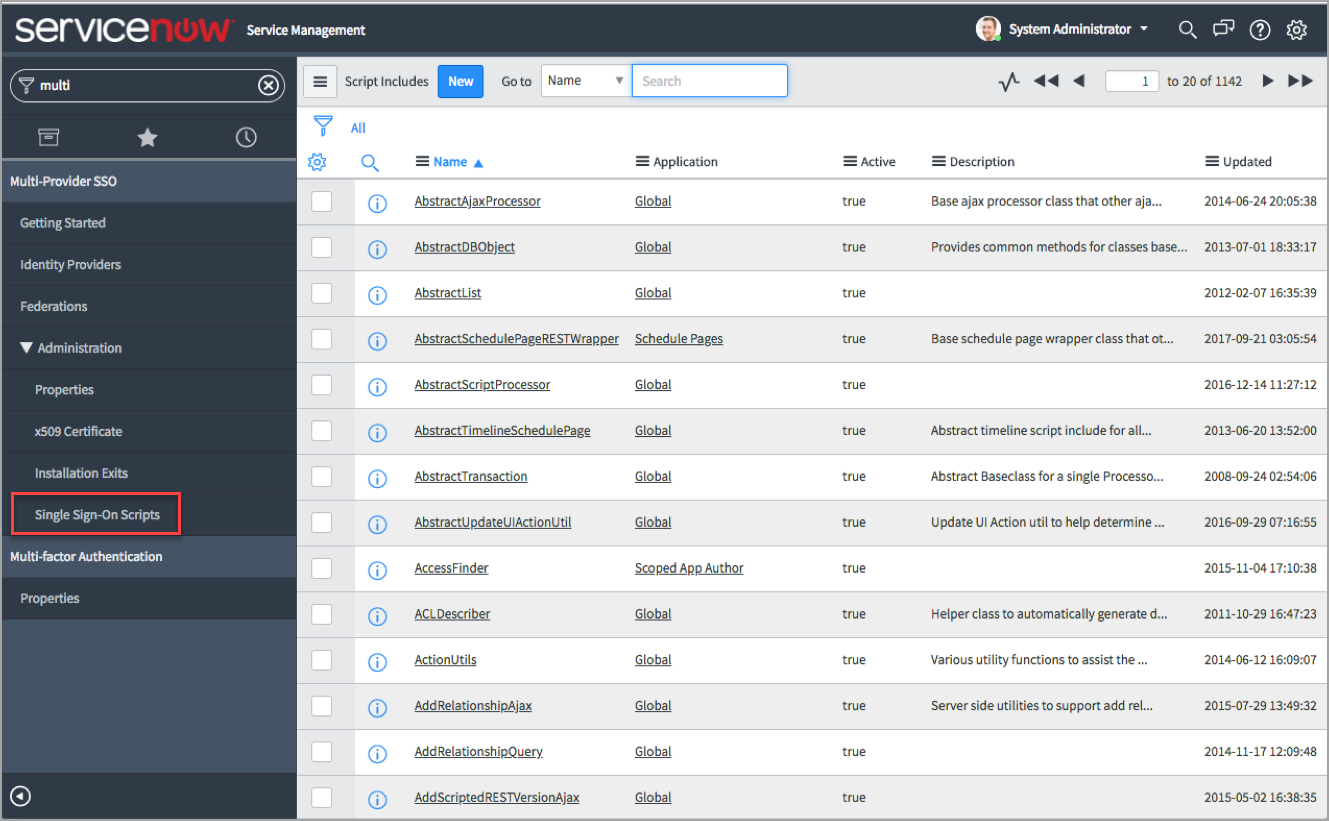
- Deselect the existing filter Name starts with MultiSSO and search for SAML 2.
- Click SAML2_update1 and scroll down to line 915 of the script. This line is for the Kingston version. It can be modified to use for other ServiceNow versions.
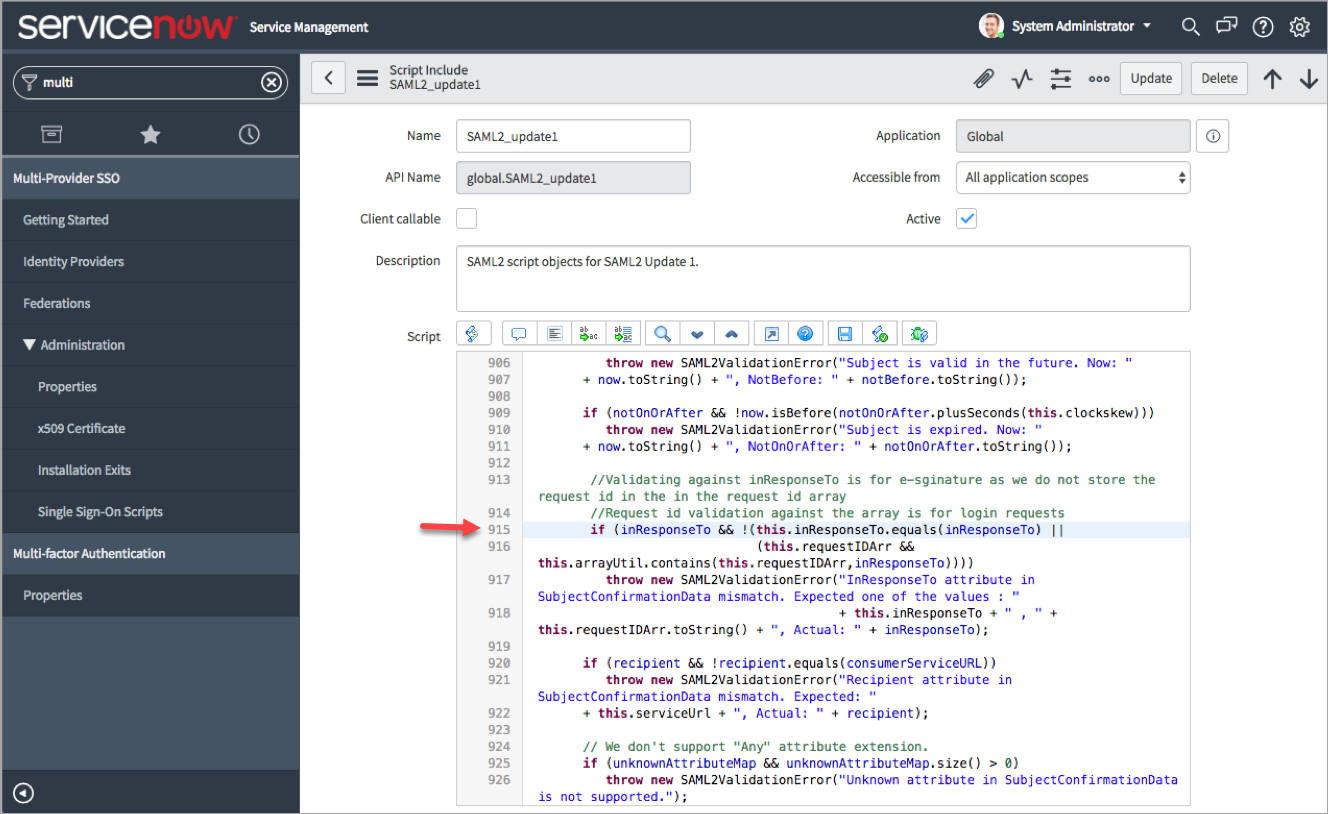
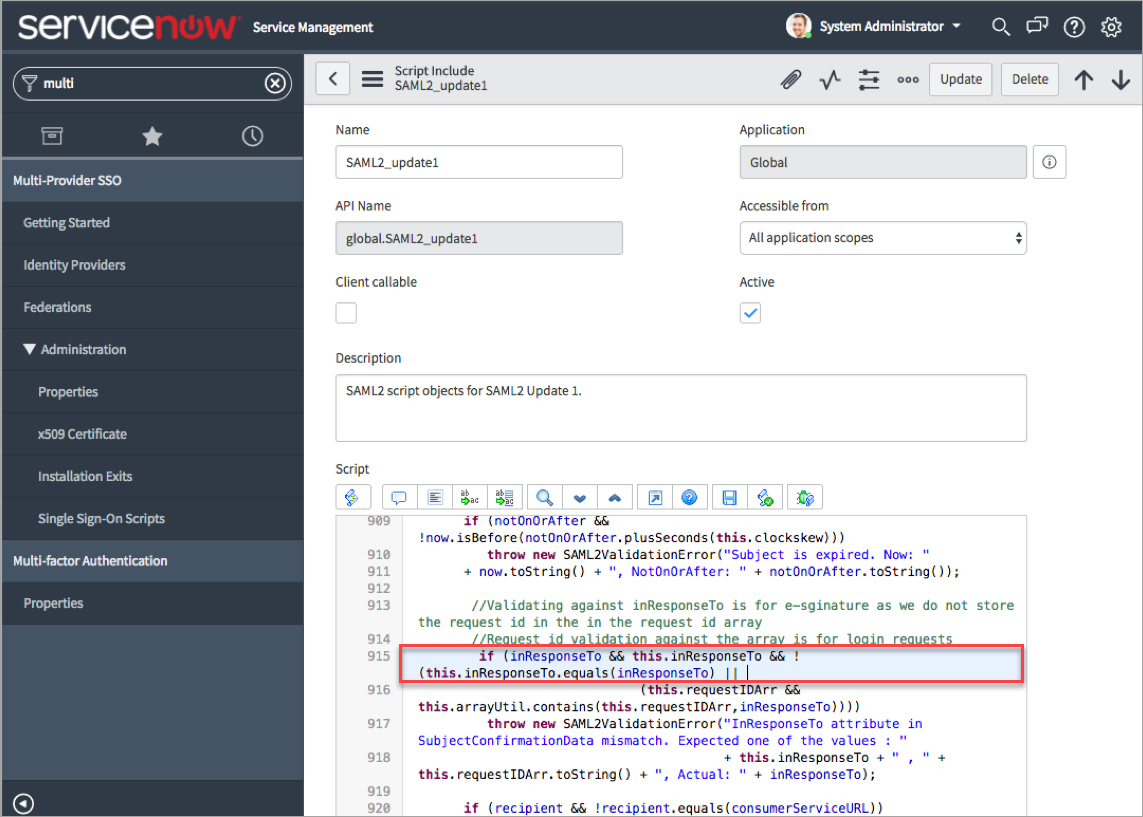
- Update line 915 of the script with the following code:
if (inResponseTo && this.inResponseTo && !
(this.inResponseTo.equals(inResponseTo) ||
-
Click Update.
Now, the ServiceNow is successfully configured to use the IdPs. To configure ADFS and Okta, see ServiceNow SSO Integration with ADFS using SAML and ServiceNow SSO Integration with Okta using SAML.

